Unlckr Ransomware
The Unlckr Ransomware is a variant of the Unlock92 Ransomware, a ransomware Trojan that was released to carry out attacks mainly in Russia and surrounding countries. The Unlckr Ransomware is a modified version of this previous threat that has some upgrades and improves its encryption method, using the RSA-2048 to make the victim's files inaccessible. Like most encryption ransomware Trojans, the Unlckr Ransomware is designed to make the victim's files unusable by encrypting them, then demanding the payment of a ransom from the victim. The Unlckr Ransomware will target numerous file types, but its main focus is the user-generated files such as those associated with Adobe Acrobat, Microsoft Office, and Libre Office, as well as media files such as music, video and images. The Unlckr Ransomware may be delivered to victims through the use of corrupted spam email attachments.
Table of Contents
It may be Impossible to Unlock the Files Locked by the Unlckr Ransomware
The Unlckr Ransomware will scan the infected computer's drives and create a list with all the files that will be encrypted. The Unlckr Ransomware will target files on all local drives, as well as external memory devices connected to the infected computer. The Unlckr Ransomware also will gather information about the infected computer and relay it to its Command and Control server, then will receive the configuration instructions that will be used in the Unlckr Ransomware attack. The Unlckr Ransomware uses a strong encryption algorithm to target these files, which will become encrypted and no longer readable. The Unlckr Ransomware is designed to infect computers running the Windows operating system and will use corrupted macros and scripts to execute its corrupted code on the victim's computer. The files encrypted by the Unlckr Ransomware attack will have the file extension '.cr020801' to the end of their names.
How the Unlckr Ransomware Demands a Ransom Payment from Its Victims
The Unlckr Ransomware will deliver a text file named '_INSTRUKTSYA _ !.txt' ('Instructions') after encrypting its victim's files. This text file will be placed on the infected computer's desktop and contain information about the attack and instructions for the victim to carry out the ransom payment. Malware researchers have uncovered different variants of the Unlckr Ransomware, which may use slightly different ransom notes and file extensions in their attack, but underneath, these threats all function in very similar ways. The following is the ransom message that the Unlckr Ransomware delivers to its victims' computers:
'Your files are encrypted using the crypto-resistant RSA-2048 algorithm. If you want to recover them, please send one of the encrypted files and file yourkey.ttp to e-mail: unlckr@protonmail.com
If you do not receive a response within 24 hours or the letter is returned with an error, download the TOR browser from www.torproject[.]com and use it to go to the site h[tt]p://n3r2kuzhw2h7x6j5[.]onion - there you will see the current mailbox.
Attempts to repair files yourself can irretrievably ruin them!'
The ransom note leads computer users to the TOR network to pay the ransom associated with the Unlckr Ransomware attack. Computer users should refrain from making the Unlckr Ransomware payment or following the instructions contained in the Unlckr Ransomware ransom note.
Dealing with the Unlckr Ransomware Attack
The Unlckr Ransomware attack is typical of these infections. It is insistently advised to avoid following the Unlckr Ransomware's instructions, especially since paying these ransoms rarely results in regaining the affected files. The con artists are just as likely to ignore the victim, demand a larger ransom payment, or re-infect the victim's computer with threats. After the Unlckr Ransomware attack, the best way to recover is to restore the affected files from a backup copy. Because of this, make sure that you have file backups on an external device or the cloud. Having file backups is an essential part of protecting your computer from ransomware Trojans like the Unlckr Ransomware, which are becoming more common every day.
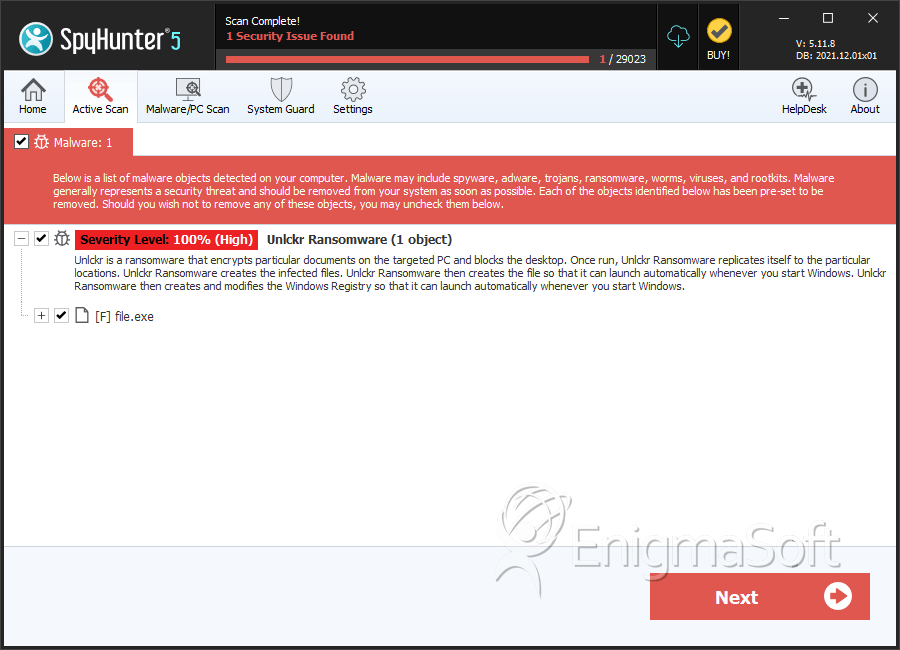
SpyHunter Detects & Remove Unlckr Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 391b5f07201cf813d09e45589e4c13a3 | 0 |
| 2. | file.exe | b53fb4a3db87bf0d4fd747fd7cc31505 | 0 |
| 3. | file.exe | 962d4693c8455aeb097141ddec4ef883 | 0 |
| 4. | file.exe | e21ef8d0bf74580f058be8bab8b36ffa | 0 |
| 5. | file.exe | 5fd79cc5b2afead17fae9befe63e65b1 | 0 |
| 6. | file.exe | e009494e60ddcc7eca6d233a9b08fca3 | 0 |
| 7. | file.exe | 61f1e0d5dd1842a83f39e11687419174 | 0 |
| 8. | file.exe | a58670b655ab9c9168a0d6c948c29889 | 0 |
| 9. | file.exe | 48b31eb1480fa550ccd29a4cbe601ee7 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.