Troj/Zbot-CCH
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
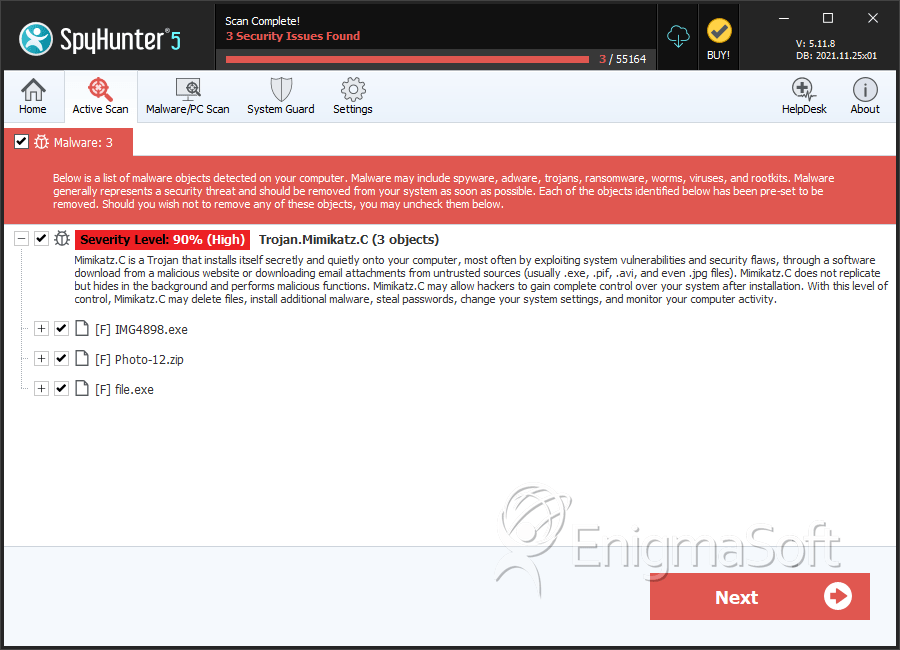
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Ranking: | 7,531 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 1,290 |
| First Seen: | June 26, 2012 |
| Last Seen: | September 13, 2023 |
| OS(es) Affected: | Windows |
Troj/Zbot-CCH is a dangerous Trojan in the Zbot or Zeus family and among the most common malware included in spam campaigns. The role of the Troj/Zbot-CCH Trojan in a malware attack is to establish a backdoor into the victim's computer system and to download a Remote Access Tool (RAT) that allows criminals to control the infected computer system from a remote location. The Troj/Zbot-CCH Trojan may also have keylogger capabilities and have components designed to steal financial information and sensitive data such as online passwords and credit card numbers. Like most Trojans from the Trojan.Zbot or Zeus Trojan family, Troj/Zbot-CCH does not have the ability to spread on its own and will rely on other malware or on social engineering in order to infect a computer system.
Table of Contents
Troj/Zbot-CCH and Spam Email Campaigns
Spam email messages are among some of the most common ways in which criminals spread malware such as the Troj/Zbot-CCH Trojan. ESG security researchers have found a widespread outbreak of the Troj/Zbot-CCH Trojan associated with a recent spam email campaign. This spam email campaign will try to convince victims that it contains an email attachment with compromising photos of the victim or of the victim's girlfriend. To do this, most of the messages that have been associated with this spam email campaign will use threatening language blackmailing the victim with the supposed compromising photographs or will attempt to make the victim think that the photos in question have been leaked.
All messages in this spam email campaign share the same file attachment, a ZIP file that is named 'Photos'. However, opening this ZIP file will actually install Troj/Zbot-CCH itself or a downloader Trojan which will then contact a remote server to download and install Troj/Zbot-CCH and other malware threats onto the victim's computer system. In some cases, actual nude photos may be shown in order to distract the victim while the installation of Troj/Zbot-CCH or other malware occurs in the background.
What You Can Do to Protect Yourself from Troj/Zbot-CCH
The best things you can do to protect your computer system from a Troj/Zbot-CCH infection include using reliable security software and common sense when going online. Most malware infections can be prevented by following basic online safety guidelines such as never opening unsolicited email attachments, staying away from websites considered unsafe (such as pornographic websites and file sharing web pages) and always keeping your security software fully up to date.
Aliases
11 security vendors flagged this file as malicious.
| Anti-Virus Software | Detection |
|---|---|
| Fortinet | W32/Zbot.ACM!tr |
| Ikarus | Trojan.Win32.Ransom |
| AhnLab-V3 | Trojan/Win32.Birele |
| Sophos | Troj/Zbot-CCH |
| McAfee-GW-Edition | Artemis!B4E77546C5A7 |
| DrWeb | BackDoor.Andromeda.22 |
| BitDefender | Trojan.Generic.KDV.658377 |
| Kaspersky | Trojan.Win32.Jorik.Androm.qi |
| Symantec | Downloader.Dromedan |
| F-Prot | W32/Trojan2.NRTE |
| McAfee | Generic.dx!b2u4 |
SpyHunter Detects & Remove Troj/Zbot-CCH
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | IMG4898.exe | b4e77546c5a762987fafe289e401aa57 | 0 |
| 2. | Photo-12.zip | 0fcd721f02143fd8f9ca5c4a2ccadde5 | 0 |
| 3. | file.exe | f24446bf2bb69ff8bcb377c0cbf6a955 | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.