Trojan.Smeazymo
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
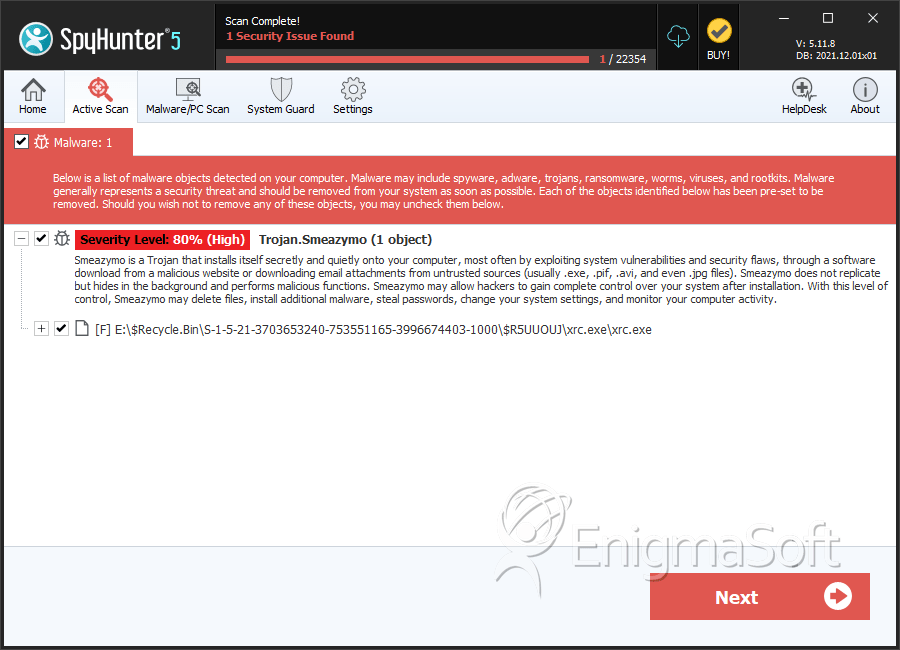
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 80 % (High) |
| Infected Computers: | 32 |
| First Seen: | September 24, 2015 |
| Last Seen: | May 31, 2023 |
| OS(es) Affected: | Windows |
The Smeazymo malware is a Trojan that is known to run as a hidden file in the AppData directory. Trojan.Smeazymo falls in the category of Trojan downloaders that are used by threat actors to deliver advanced threats to compromised PCs. The Smeazymo Trojan-Downloader is distributed via exploit kits like Flimkit and corrupted links. The main executable of the Smeazymo Trojan downloader is named after a legitimate company to dissuade the user from deleting the file if it is flagged as potentially unsafe by a security scanner.
The Smeazymo Trojan-Downloader is rather simple and contains two hard-coded URLs in its code that the program opens to download threats on the targeted PC. Computer users that run unpatched and outdated software are likely to be infected with the Smeazymo Trojan downloader and may be exposed to threats like the Globe Ransomware. As stated before, the Smeazymo Trojan is designed to connect to unsafe sites like Shoprdig.com, download and run advanced threats. Web filters may be able to intercept connections to unsafe locations, but Smeazymo may feature links to recently compromised sites that are not blacklisted yet. There are many versions of the Smeazymo Trojan that we are aware of, and they can be flagged as:
- Atros2.BZUD
- MSIL/Smeazymo
- TR/Smeazymo.50688
- PUP.Optional.Smeazymo
- Trojan:Win32/Dynamer!ac
- Trojan:Win32/Skeeyah.A!bit
- Trojan.win32.skeeyah.a!rfn
- Trojan-Downloader.MSIL.Crypted.hg
Typically, the samples of Smeazymo are found in C:\Users\%USERNAME%\AppData\Local\ and lack a description, as well as a valid digital signature. The Smeazymo appeared in August 2015 its development has been tracked since. Experts recommend users to install a reliable anti-malware suite to prevent the Smeazymo Trojan-Downloader from running on their systems.
SpyHunter Detects & Remove Trojan.Smeazymo
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | xrc.exe | d8d56fb34b9fc591e0aac102b8e013dd | 23 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.