Trojan.PornoAsset.B
Threat Scorecard
EnigmaSoft Threat Scorecard
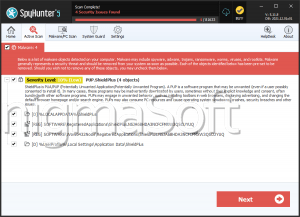
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 5,229 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 135 |
| First Seen: | March 20, 2024 |
| Last Seen: | May 6, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.PornoAsset.B |
|---|---|
| Packers: | UPX |
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
34b08b33f8d0237578a82f673682fedc
SHA1:
817d59d2b09ffe97daed0207b912cfadf87f6809
SHA256:
AEC6AA5FE12F7EE1F4E75A7487868650A6A854C44FA777076D2F715ECBA7E95C
File Size:
847.87 KB, 847872 bytes
|
|
MD5:
567c02696d4f1b66dbec1c424a1161d9
SHA1:
afaca143e61a4f2deed65444e374e9a71c9ce50c
SHA256:
282C9F330992F356BA2528FAD1483C9146F2BE53B66C34DD2B372F1FB1637853
File Size:
2.99 MB, 2985984 bytes
|
|
MD5:
d615984b7f9aa2876cd6fd86617a4d58
SHA1:
3f0cd85c97cd9b49bb90669d6e5481e2cd6989b5
SHA256:
739FFA1E03E73FE69DD08FAD3F55A6F8265DE649AEE0124E79E0FFB441114C34
File Size:
872.45 KB, 872448 bytes
|
|
MD5:
beb8e9af418beeb6dc4dde1928eb6b55
SHA1:
6cb7f67472327c37263f2471a07b6b5f428a6852
SHA256:
834BD86217DFE26B94D97620E68A30680E7C9D591A43D70E3E3F811AC860D0F5
File Size:
1.21 MB, 1212416 bytes
|
|
MD5:
ef681c7649d3839379b61910eb4dcdde
SHA1:
f86fb68434f54ff510c9187a5131f7ee6180361b
SHA256:
AFB269BD2A0D0638CFDDA5880B745B23BC43CB80A2C2BC5D8D68F150FAE79385
File Size:
3.10 MB, 3096576 bytes
|
Show More
|
MD5:
e9a8936a65dcfc456eb63190f3acd009
SHA1:
b8753105d2e9efcde383623544c5188176985aa6
SHA256:
1C13F5340D4BB4D8B9FEEB45FF27F29DFF904C6886ADD90C42C3619581D3CE81
File Size:
376.32 KB, 376320 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have relocations information
- File doesn't have security information
- File has been packed
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.File Traits
- HighEntropy
- No Version Info
- packed
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 2,699 |
|---|---|
| Potentially Malicious Blocks: | 780 |
| Whitelisted Blocks: | 1,422 |
| Unknown Blocks: | 497 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- PornoAsset.B
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKCU\system\currentcontrolset\control\mediaproperties\privateproperties\directinput\vid_0627&pid_0001\calibration\0::guid | 닀浨鈷ᇰƀ䕄呓 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::version | Ԁ | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::name | 817D59D2B09FFE97DAED0207B912CFADF87F6809_0000847872 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::id | 817D59D2B09FFE97DAED0207B912CFADF87F6809_00008478724187EBB6000CF000 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::mostrecentstart | RegNtPreCreateKey | |
| HKCU\system\currentcontrolset\control\mediaproperties\privateproperties\directinput\vid_0627&pid_0001\calibration\0::guid | 雠♊일ᇰƀ䕄呓 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::name | AFACA143E61A4F2DEED65444E374E9A71C9CE50C_0002985984 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::id | AFACA143E61A4F2DEED65444E374E9A71C9CE50C_00029859844AC6A46F002D9000 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::mostrecentstart | 錕寋ǜ | RegNtPreCreateKey |
| HKCU\system\currentcontrolset\control\mediaproperties\privateproperties\directinput\vid_0627&pid_0001\calibration\0::guid | 伀䛶ᇰƀ䕄呓 | RegNtPreCreateKey |
Show More
| HKCU\software\microsoft\directinput\mostrecentapplication::name | 3F0CD85C97CD9B49BB90669D6E5481E2CD6989B5_0000872448 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::id | 3F0CD85C97CD9B49BB90669D6E5481E2CD6989B5_000087244846EB1144000D5000 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::mostrecentstart | RegNtPreCreateKey | |
| HKCU\system\currentcontrolset\control\mediaproperties\privateproperties\directinput\vid_0627&pid_0001\calibration\0::guid | 싀뼽ᇰƀ䕄呓 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::name | 6CB7F67472327C37263F2471A07B6B5F428A6852_0001212416 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::id | 6CB7F67472327C37263F2471A07B6B5F428A6852_000121241649962AB300128000 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::mostrecentstart | 맓辻詤ǜ | RegNtPreCreateKey |
| HKCU\system\currentcontrolset\control\mediaproperties\privateproperties\directinput\vid_0627&pid_0001\calibration\0::guid | 僠禬ᝎᇱƀ䕄呓 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::name | F86FB68434F54FF510C9187A5131F7EE6180361B_0003096576 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::id | F86FB68434F54FF510C9187A5131F7EE6180361B_000309657646EB1144002F4000 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::mostrecentstart | 䨧ꮞǜ | RegNtPreCreateKey |
| HKCU\system\currentcontrolset\control\mediaproperties\privateproperties\directinput\vid_0627&pid_0001\calibration\0::guid | ꒫伇ᇱƀ䕄呓 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::name | B8753105D2E9EFCDE383623544C5188176985AA6_0000376320 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::id | B8753105D2E9EFCDE383623544C5188176985AA6_000037632046EB11440005BE00 | RegNtPreCreateKey |
| HKCU\software\microsoft\directinput\mostrecentapplication::mostrecentstart | ᑻ፣ǜ | RegNtPreCreateKey |