Trojan.Agent.AIAH
Threat Scorecard
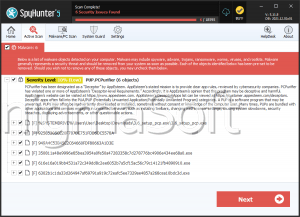
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 12,917 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 96 |
| First Seen: | January 9, 2024 |
| Last Seen: | May 30, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Agent.AIAH |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
a50c1289d7bddc5d3de574e3896b8346
SHA1:
0ac77960f4aa6a2d5ec679891ba1023273046539
SHA256:
E3B556D3C9116720B819958ECCC0CF67D276C0E7C27CD90609DC4A4CB47F1797
File Size:
5.53 MB, 5526032 bytes
|
|
MD5:
7b2d3bfd4e11f927789069bae9016453
SHA1:
a23d9c09eec076449acd1c4bd9bc033f7e0d1c9a
SHA256:
2763E4B6EBEFDBBDD97523023E4355B42DF258783884637B90851721C4ADED81
File Size:
5.36 MB, 5362704 bytes
|
|
MD5:
4d4cb9899fe62a62bc7cac1afa8972a0
SHA1:
35e5ea3490dbff9ae04a273013715b279b16dff5
SHA256:
2A3D342CDA7B5813125E290C04E97F6DC23DFC26FB45B7CA11B7BE803B927732
File Size:
5.36 MB, 5364752 bytes
|
|
MD5:
2855cc9092570eef948676211b00cfab
SHA1:
2f77133077dafd5ac0e7677a8e97b36f69b92d41
SHA256:
0D56C3FBB49F1823FB33533C0C805FFCD4E88211F937561EED03A5B4DA4C9D70
File Size:
5.53 MB, 5525520 bytes
|
|
MD5:
59767d88ddeca9abecd5937249f68517
SHA1:
1e69a1dc28d553ad06b06e9cadf5b246d742c3f6
SHA256:
079CE73BBC83E81BA50A14B4E2405F020F3D275EE8D7A6EBE23993C1F2224AE6
File Size:
5.37 MB, 5366800 bytes
|
Show More
|
MD5:
6c4a6bbb1098b8d65194577086aff7fa
SHA1:
25baf37163fa0035500fde954d3a16e377d08cc0
SHA256:
92D69B540D17A0C4B4EC56CA568749798153E9DB7FD6050C3416844DFD16C3F2
File Size:
5.52 MB, 5523984 bytes
|
|
MD5:
bc56be674021af4f979f00bf86d7668e
SHA1:
338ee148505b0df0b266d2995201c6df13dbf8ad
SHA256:
38D10CBE20C9187BF9A452FAA441EECCCB81BCD6CEF79922B7BBCE607BF3A82A
File Size:
5.36 MB, 5363216 bytes
|
|
MD5:
8f51ee13ba4c9167a068b79039a661a5
SHA1:
a6c43139916d01e92c6a7c7105abdb14693970f2
SHA256:
4714BF12777E042087EE6D6A09369C0BAF2B70A98833497818589D94E1AA0649
File Size:
5.37 MB, 5366288 bytes
|
|
MD5:
692419d4ecfc446c458c90842313d22b
SHA1:
f7ab4946d423e31cf0bbee2cd4667de012eba029
SHA256:
E20F682E5A728BC4AAC110C0CD7EB545FB11B5FE57C809C54CF905FD22D38713
File Size:
5.52 MB, 5523472 bytes
|
|
MD5:
28e015900a007aaf811e9dda872e7586
SHA1:
51bb3821d1a80a429385af35f7cdb0d161d93dd6
SHA256:
DB4A9C58B71A7A394248AF05B1521609F9287919B029D8F9DA85242FC0C3D9FC
File Size:
5.36 MB, 5363216 bytes
|
|
MD5:
639a163df39b2c6ce48de0e9298246c5
SHA1:
71c575c27b2c92270ba52116882cdc9575b16d5f
SHA256:
03BB18C8D1213D95A51FC261FF82AD0FAE723C5AA7160ECB4205E27BE90D263E
File Size:
5.36 MB, 5364752 bytes
|
|
MD5:
030cfa35ed261d7189597650f108c638
SHA1:
07a35042149474c18694b7e8b62f1ea18729198c
SHA256:
B3178C7E534414143A5744F036C2A3D4E4C325C6F49EE81C736EE8A876D8CC95
File Size:
5.37 MB, 5365264 bytes
|
|
MD5:
b22a4b5ee3c306e2967d283e31f13a67
SHA1:
2581c1ba0297054bb268104f07052ac71197557e
SHA256:
88A0380BE7B8ECCEA3B9A5A2744295CB92E952976DEE35C2173E1EFC00C24898
File Size:
5.37 MB, 5365264 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | The Qt Company Ltd. |
| File Description | C++ Application Development Framework |
| File Version | 5.14.2.0 |
| Legal Copyright | Copyright (C) 2020 The Qt Company Ltd. |
| Original Filename | Qt5Core.dll |
| Product Name | Qt5 |
| Product Version | 5.14.2.0 |
File Traits
- dll
- HighEntropy
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 12,459 |
|---|---|
| Potentially Malicious Blocks: | 707 |
| Whitelisted Blocks: | 11,733 |
| Unknown Blocks: | 19 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Agent.AIAH
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Shell Execute |
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\0ac77960f4aa6a2d5ec679891ba1023273046539_0005526032.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\a23d9c09eec076449acd1c4bd9bc033f7e0d1c9a_0005362704.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\35e5ea3490dbff9ae04a273013715b279b16dff5_0005364752.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2f77133077dafd5ac0e7677a8e97b36f69b92d41_0005525520.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\1e69a1dc28d553ad06b06e9cadf5b246d742c3f6_0005366800.,LiQMAxHB
|
Show More
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\25baf37163fa0035500fde954d3a16e377d08cc0_0005523984.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\338ee148505b0df0b266d2995201c6df13dbf8ad_0005363216.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\a6c43139916d01e92c6a7c7105abdb14693970f2_0005366288.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\f7ab4946d423e31cf0bbee2cd4667de012eba029_0005523472.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\51bb3821d1a80a429385af35f7cdb0d161d93dd6_0005363216.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\71c575c27b2c92270ba52116882cdc9575b16d5f_0005364752.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\07a35042149474c18694b7e8b62f1ea18729198c_0005365264.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2581c1ba0297054bb268104f07052ac71197557e_0005365264.,LiQMAxHB
|