StrutterGear Ransomware
The StrutterGear Ransomware is a ransomware Trojan that seems to be a variant of the Jigsaw Ransomware, a family of ransomware that has been active for quite a while and that used in its themes elements from the Saw movies and their iconic Jigsaw character. The StrutterGear Ransomware was first observed on June 2017 on online anti-virus platforms, which may be used by con artists to test their ransomware variants to see whether they can evade detection by established ransomware Trojans. There are several variants of the StrutterGear Ransomware, all released in 2017 and targeting computers running the Windows operating system. The StrutterGear Ransomware may be released publicly, but for now, it exists in a test version that seems to be incomplete.
Table of Contents
The StrutterGear Ransomware Belongs to the Jigsaw Family of Ransomware Trojans
The StrutterGear Ransomware and other Jigsaw variants can be delivered through corrupted email attachments, commonly in the form of corrupted files using scripts and macros to download and install the StrutterGear Ransomware onto the victim's computer. These files will be delivered in spam email campaigns that use social engineering elements to trick the victims into believing that a legitimate company such as a social network platform or an online retailer like Amazon sent the file. The StrutterGear Ransomware can be detected by many anti-virus programs as a Jigsaw variant, and may show up under the following detection names after an anti-virus scan:
Generic.MSIL.Ransomware.Jigsaw.41B02FF6
HEUR:Trojan.Win32.Generic
MSIL/Filecoder.JIGSAW!tr
Ransom:MSIL/JigsawLocker.A
Ransom_JIGSAW.SM
TR/AD.JigsawLocker.kevoq
Trojan ( 700000121 )
W32/FrauDrop.AKQFM!tr
Win32/Trojan.Ransom.220
variant of MSIL/Filecoder.Jigsaw.B
How the StrutterGear Ransomware may Infect a Computer
One aspect of the StrutterGear Ransomware that's different from other variants in the Jigsaw family is that the StrutterGear Ransomware will not add an extension to the files that it encrypts in its attacks. Other Jigsaw variants will use custom extensions to mark the files that have been compromised. The StrutterGear Ransomware will encrypt victims' files effectively, making them inaccessible and preventing victims from accessing their data. The StrutterGear Ransomware takes the victim's data hostage until a ransom is paid. The StrutterGear Ransomware will target the user-generated files while leaving the Windows operating system files alone. The StrutterGear Ransomware displays its ransom note in a program window that looks like the Command Line terminal. The StrutterGear Ransomware's ransom message notifies the victim that it is necessary to pay a ransom of at least $300 USD, depending on the StrutterGear Ransomware variant. However, PC security researchers strongly advise computer users to refrain from paying the StrutterGear Ransomware ransom. There is no assurance that these people will comply and restore the affected files and, in fact, paying the ransom can lead to additional infection or demands more money. Furthermore, paying the StrutterGear Ransomware ransom allows the people responsible for the StrutterGear Ransomware to continue creating and developing ransomware variants like the StrutterGear Ransomware and claiming new victims in the attacks.
Protecting Your Data from the StrutterGear Ransomware and Similar Threat
The best protection against the StrutterGear Ransomware and similar ransomware Trojans is to have backup copies of your files. Having backups on an external memory device or the cloud will protect you from this attack. This is because having the capacity to restore your files from the backup without having to pay the ransom undoes the attack completely, removing all leverage the con artists have over the victim. In fact, if enough computer users have file backups, attacks like the StrutterGear Ransomware will no longer be effective and will die off eventually. Apart from having file backups, computer users should take other steps to protect their computers against threats like the StrutterGear Ransomware. There are several important steps computer users can take, principally the use of a reliable security program, which can intercept the StrutterGear Ransomware infection and stop it from carrying out its attack before the victim's files become compromised. Since the StrutterGear Ransomware may be delivered using corrupted spam email attachments, having a strong anti-spam filter also is an essential protection against threats like the StrutterGear Ransomware.
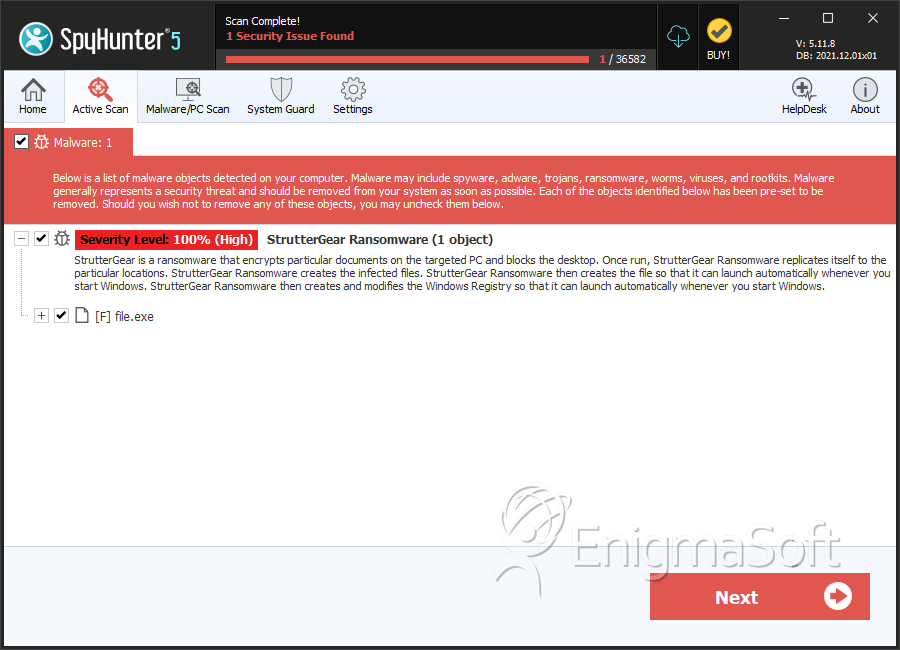
SpyHunter Detects & Remove StrutterGear Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 9309fe0eb6ff58a49475e60e8a1a2787 | 0 |
| 2. | file.exe | a12e1bd4501d62ccf82729833afff6af | 0 |

