SparkCat Malware
A recently uncovered threat campaign, dubbed SparkCat, has infiltrated both Apple's App Store and Google Play using deceptive apps designed to collect cryptocurrency wallet recovery phrases. These applications, disguised as legitimate services, secretly extract mnemonic phrases from victims' devices, putting digital assets at risk.
Table of Contents
Exploiting OCR to Harvest Wallet Recovery Phrases
SparkCat leverages an advanced OpticalCharacter Recognition (OCR) model to scan users' photo libraries for images containing wallet recovery phrases. Once detected, these sensitive images are exfiltrated to a remote Command-and-Control (C2) server. The campaign is named after an embedded software development kit (SDK) that includes a Java component called Spark, which masquerades as an analytics module. It remains unclear whether this infiltration resulted from a supply chain attack or was deliberately introduced by developers.
Breaking into Apple’s App Store
While Android threats with OCR capabilities have surfaced before, SparkCat represents one of the first instances of such an attack making its way into Apple's App Store. On Google Play, the compromised applications were downloaded over 242,000 times before being removed from both platforms on February 7, 2025.
A Multi-Platform Operation
Evidence suggests that SparkCat has been active since March 2024. Its unsafe applications are distributed via both official and third-party app stores. The fraudulent applications impersonate AI tools, food delivery services, and Web3 platforms, with some even providing seemingly legitimate functionality to avoid suspicion.
How SparkCat Collects Data
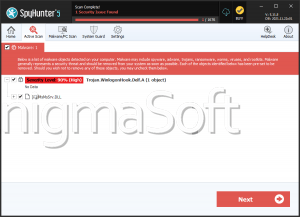
On Android devices, the malware decrypts and activates an OCR plug-in powered by Google's ML Kit library. It scans image galleries for text that matches predefined keywords from its C2 server. Any flagged images are then transmitted to the attackers.
The iOS variant of SparkCat uses the exact ML Kit-based OCR mechanism to identify and extract sensitive information. Uniquely, this version also employs a Rust-based communication framework for interacting with its C2 server—an uncommon tactic in mobile threats.
Who is Behind the Attack?
Analysis of the keywords used and the distribution patterns suggests that SparkCat primarily targets users in Europe and Asia. The evidence points to threat actors with fluency in Chinese, though their exact identity remains unknown.
A Stealthy Trojan in Disguise
What makes SparkCat particularly deceptive is its ability to operate without raising red flags. The permissions it requests appear either necessary for the application's advertised features or innocuous, allowing it to blend in without triggering suspicion. This stealthy approach makes it harder for users to recognize the threat before their cryptocurrency wallets are compromised.