Izsiljevalska programska oprema ostaja ena najresnejših digitalnih groženj, s katerimi se soočajo tako posamezniki kot organizacije. Sodobne različice niso zasnovane le za šifriranje datotek, temveč tudi za krajo občutljivih informacij, s čimer žrtve silijo v plačilo velikih vsot denarja. V današnjem spreminjajočem se okolju groženj so ključnega pomena budnost, vzdrževanje močne kibernetske higiene in izvajanje večplastne obrambe. Eden najnevarnejših nedavnih dosežkov na tem področju je izsiljevalska programska oprema LockBit 5.0.
LockBit 5.0: Polirana in zmogljiva različica
LockBit 5.0 je najnovejša različica družine izsiljevalskih programskih orožij LockBit, ki gradi neposredno na kodni osnovi LockBit 4.0, hkrati pa uvaja izboljšave, ki otežujejo zaznavanje in ublažitev posledic. Ko se izvede, šifrira datoteke v sistemu in vsakemu imenu datoteke doda edinstveno, naključno 16-mestno končnico. Na primer, datoteka z imenom »1.png« postane »1.png.db9785905a3cad2c«. Poleg šifriranja v prizadete mape spusti zahtevo za odkupnino z naslovom »ReadMeForDecrypt.txt«.
Zahteva za odkupnino obvesti žrtve, da so bile njihove datoteke in podatki ogroženi. Zahteva plačilo v kriptovaluti, običajno prek komunikacije prek Tora, in opozarja, da bodo ukradeni podatki razkriti, če plačilo ne bo izvedeno. Žrtve pozivajo, naj ne kontaktirajo oblasti, napadalci pa poskušajo vcepiti strah in občutek nujnosti.
Sofisticirane zmogljivosti in taktike
LockBit 5.0 vključuje tehnične izboljšave, ki dokazujejo zrelost razvijalcev izsiljevalske programske opreme:
Prilagoditev za partnerje : Različica izsiljevalske programske opreme za Windows ponuja čistejši in prilagodljivejši vmesnik, ki partnerjem omogoča izbiro metod in ciljev šifriranja.
Tehnike proti analizi : Onemogoči nekatere funkcije sledenja sistema Windows, da ovira raziskovanje zlonamerne programske opreme.
Ciljanje na več platform : Poleg sistema Windows LockBit 5.0 vključuje tudi nevarne različice za Linux in VMware ESXi, ki lahko šifrirajo celotna virtualizirana okolja.
Selektivno izogibanje : Sistemom, ki se nahajajo v Rusiji ali sorodnih regijah, se izogne z izvajanjem preverjanj geolokacije.
Čeprav je predstavljen kot velika izdaja, LockBit 5.0 ponovno uporablja pomembne dele kode LockBit 4.0, kot so algoritmi za zgoščevanje in dinamično ločljivost API-ja, zaradi česar gre bolj za postopno, a nevarno nadgradnjo.
Vektorji distribucije: Kako se LockBit 5.0 širi
Operaterji LockBita se za maksimiranje dosega zanašajo na različne metode okužbe. Izsiljevalska programska oprema se običajno širi prek:
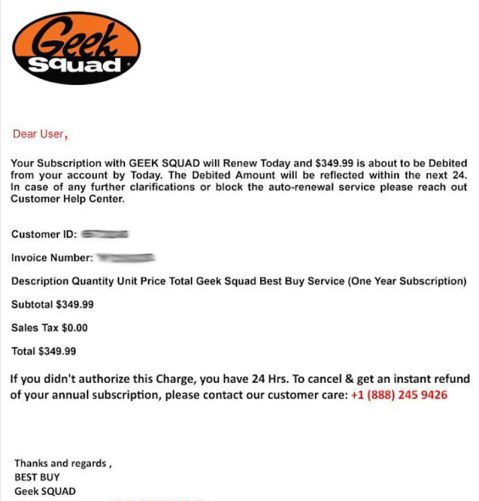
- Zlonamerne priloge e-pošte ali povezave, ki se izdajajo za legitimne dokumente.
- Goljufiva ali ogrožena spletna mesta, vključno z lažnimi portali za tehnično podporo.
- Izkoriščanje nepopravljenih ranljivosti programske opreme.
- Zlonamerne oglaševalske kampanje, piratska programska oprema in nezakoniti generatorji ključev.
- Omrežja enakovrednih uporabnikov, programi za prenos datotek tretjih oseb in nepreverjene trgovine z aplikacijami.
Ta večplastni pristop napadalcem omogoča, da ciljajo tako na posameznike kot na poslovne sisteme, kar povečuje verjetnost obsežne škode.
Okrepite svojo obrambo pred izsiljevalsko programsko opremo
Zaščita pred sofisticirano izsiljevalsko programsko opremo, kot je LockBit 5.0, zahteva proaktivne in večplastne varnostne ukrepe. Uporabniki in organizacije bi morali sprejeti kombinacijo tehničnih zaščitnih ukrepov in praks varnega brskanja. Nekatere najučinkovitejše strategije vključujejo:
Poskrbite za posodabljanje sistemov : Pravočasno namestite popravke za operacijski sistem in programsko opremo, da odpravite ranljivosti, ki jih je mogoče izkoristiti.
Uporabite močno zaščito končnih točk : Uvedite ugledne protivirusne rešitve in rešitve za zaznavanje končnih točk, ki lahko prepoznajo napredne grožnje.
Uporabljajte varno e-pošto in splet : Bodite previdni pri neželenih prilogah, povezavah in prenosih iz nepreverjenih virov.
Vzdržujte varnostne kopije brez povezave : Shranite ključne datoteke na varnih lokacijah brez povezave, da zagotovite obnovitev brez plačila odkupnine.
Uporabi dostop z najmanjšimi privilegiji : Omeji uporabniška dovoljenja in segmentiraj omrežja, da omejiš morebitne izbruhe izsiljevalske programske opreme.
Omogočite večfaktorsko preverjanje pristnosti (MFA) : Zaščitite račune pred ogrožanjem zaradi ukradenih poverilnic.
Redno izobražujte uporabnike : Usposabljanje osebja in posameznikov za prepoznavanje poskusov lažnega predstavljanja in socialnega inženiringa je bistvenega pomena.
Zaključne misli
LockBit 5.0 poudarja, kako skupine, ki se ukvarjajo z izsiljevalsko programsko opremo, nenehno izpopolnjujejo svoja orodja za kar največji učinek. Njegova sposobnost šifriranja celotnih okolij, izogibanja analizi in izvajanja psihološkega pritiska na žrtve ga naredi še posebej uničujočo grožnjo. Najbolj zanesljiva obramba je preventiva, ki združuje posodobljeno tehnologijo, odporne strategije varnostnega kopiranja in ozaveščenost uporabnikov. Z uvedbo teh večplastnih varnostnih ukrepov uporabniki in organizacije znatno zmanjšajo možnosti, da postanejo žrtve uničujočih napadov izsiljevalske programske opreme.
System Messages
The following system messages may be associated with Izsiljevalska programska oprema LockBit 5.0:
~~~ You have been attacked by LockBit 5.0 - the fastest, most stable and immortal ransomware since 2019 ~~~~
>>>>> You must pay us.
Tor Browser link where the stolen infortmation will be published:
-
>>>>> What is the guarantee that we won't scam you?
We are the oldest extortion gang on the planet and nothing is more important to us than our reputation. We are not a politically motivated group and want nothing but financial rewards for our work. If we defraud even one client, other clients will not pay us. In 5 years, not a single client has been left dissatisfied after making a deal with us. If you pay the ransom, we will fulfill all the terms we agreed upon during the negotiation process. Treat this situation simply as a paid training session for your system administrators, because it was the misconfiguration of your corporate network that allowed us to attack you. Our pentesting services should be paid for the same way you pay your system administrators' salaries. You can get more information about us on wikipedia hxxps://en.wikipedia.org/wiki/LockBit
>>>>> Warning! Do not delete or modify encrypted files, it will lead to irreversible problems with decryption of files!
>>>>> Don't go to the police or the FBI for help and don't tell anyone that we attacked you. They will forbid you from paying the ransom and will not help you in any way, you will be left with encrypted files and your business will die.
>>>>> When buying bitcoin, do not tell anyone the true purpose of the purchase. Some brokers, especially in the US, do not allow you to buy bitcoin to pay ransom. Communicate any other reason for the purchase, such as: personal investment in cryptocurrency, bitcoin as a gift, paying to buy assets for your business using bitcoin, cryptocurrency payment for consulting services, cryptocurrency payment for any other services, cryptocurrency donations, cryptocurrency donations for Donald Trump to win the election, buying bitcoin to participate in ICO and buy other cryptocurrencies, buying cryptocurrencies to leave an inheritance for your children, or any other purpose for buying cryptocurrency. Also you can use adequate cryptocurrency brokers who do not ask questions for what you buy cryptocurrency.
>>>>> After buying cryptocurrency from a broker, store the cryptocurrency on a cold wallet, such as https://electrum.org/ or any other cold cryptocurrency wallet, more details on https://bitcoin.org By paying the ransom from your personal cold cryptocurrency wallet, you will avoid any problems from regulators, police and brokers.
>>>>> Don't be afraid of any legal consequences, you were very scared, that's why you followed all our instructions, it's not your fault if you are very scared. Not a single company that paid us has had issues. Any excuses are just for insurance company to not pay on their obligation.
>>>>> You need to contact us via TOR sites with your personal ID
Download and install Tor Browser https://www.torproject.org/
Write to the chat room and wait for an answer, we'll guarantee a response from us. If you need a unique ID for correspondence with us that no one will know about, ask it in the chat, we will generate a secret chat for you and give you ID via private one-time memos service, no one can find out this ID but you. Sometimes you will have to wait some time for our reply, this is because we have a lot of work and we attack hundreds of companies around the world.
Tor Browser link for chat with us:
-
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
>>>>> Your personal identifier to communicate with us ID: - <<<<<
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
>>>>> Advertising:
Want a lamborghini, a ferrari and lots of titty girls? Sign up and start your pentester billionaire journey in 5 minutes with us.
-
After registration, you will receive the most flawless and reliable tools for encrypting almost all operating systems on the planet and a platform for negotiating with attacked companies.
Version: ChuongDong v1.01 | x64
Technical Analysis of LockBit 5.0
The LockBit 5.0 Windows version was found to have a better user interface with clean formatting for affiliates compared to previous versions.
It describes various options and settings for executing the ransomware, including basic options like specifying directories to encrypt or bypass, operation modes such as invisible mode and verbose mode, notes settings, encryption settings, filtering options and examples of usage.
"The detailed commands and parameters illustrate the flexibility and customization available to the attacker," the researchers commented.
Upon execution, the ransomware generates its signature ransom note and directs victims to a dedicated leak site. The infrastructure maintains LockBit's established victim interaction model, featuring a streamlined "Chat with Support" section for ransom negotiations.
Notably, the variant adds randomized 16-character file extensions to files following encryption, further complicating recovery. LockBit 5.0 also omits traditional markers at file endings, making analysis harder.
The malware deploys other anti-forensic techniques. This includes patching the EtwEventWrite API by overwriting it with a 0xC3 (return) instruction, disabling Windows Event Tracing capabilities.
As with previous LockBit versions, the new iteration uses geolocation checks, terminating execution when detecting Russian language settings or Russian geolocation.
The features observed in the Windows version were similar to those in the Linux and ESXi variants analyzed.
The ESXi variant specifically targets VMware virtualization infrastructure, which the researchers said represents a "critical escalation" in LockBit's capabilities.
This is because ESXi servers typically host multiple virtual machines, allowing attackers to encrypt entire virtualized environments with a single payload execution.
|