Ransomware i dalje je jedna od najozbiljnijih digitalnih prijetnji s kojima se suočavaju pojedinci i organizacije. Moderne varijante dizajnirane su ne samo za šifriranje datoteka već i za krađu osjetljivih informacija, prisiljavajući žrtve da plate velike svote novca. Održavanje opreza, održavanje snažne kibernetičke higijene i implementacija višeslojne obrane ključni su u današnjem okruženju prijetnji koje se stalno mijenjaju. Jedan od najopasnijih nedavnih dostignuća u ovom području je LockBit 5.0 Ransomware.
LockBit 5.0: Uglađena i moćna varijanta
LockBit 5.0 je najnovija evolucija obitelji ransomwarea LockBit, koja se izravno temelji na kodnoj bazi LockBit 4.0, a uvodi poboljšanja koja otežavaju otkrivanje i ublažavanje rizika. Nakon pokretanja, šifrira datoteke u cijelom sustavu i svakom nazivu datoteke dodaje jedinstvenu, nasumičnu ekstenziju od 16 znakova. Na primjer, datoteka pod nazivom '1.png' postaje '1.png.db9785905a3cad2c'. Uz šifriranje, u pogođenim direktorijima ostavlja poruku o otkupnini pod nazivom 'ReadMeForDecrypt.txt'.
U poruci s zahtjevom za otkupninu žrtve se obavještavaju da su njihove datoteke i podaci kompromitirani. Zahtijeva se plaćanje u kriptovaluti, obično putem komunikacije putem Tora, i upozorava se da će ukradene informacije procuriti ako se plaćanje ne izvrši. Žrtve se potiču da ne kontaktiraju vlasti, a napadači pokušavaju usaditi strah i osjećaj hitnosti.
Sofisticirane sposobnosti i taktike
LockBit 5.0 uključuje tehnička poboljšanja koja pokazuju zrelost programera ransomwarea:
Prilagodba za partnere : Windows verzija ransomwarea nudi čišće i fleksibilnije sučelje, omogućujući partnerima odabir metoda i ciljeva šifriranja.
Tehnike anti-analize : Onemogućuje određene značajke praćenja sustava Windows kako bi se ometalo istraživanje zlonamjernog softvera.
Ciljanje na više platformi : Osim Windowsa, LockBit 5.0 uključuje opasne varijante za Linux i VMware ESXi sposobne za šifriranje cijelih virtualiziranih okruženja.
Selektivno izbjegavanje : Izbjegava sustave smještene u Rusiji ili srodnim regijama provođenjem provjera geolokacije.
Iako je predstavljen kao veliko izdanje, LockBit 5.0 ponovno koristi značajne dijelove koda LockBita 4.0, poput algoritama za hashiranje i dinamičkog API razrješenja, što ga čini više postupnom, ali opasnom nadogradnjom.
Vektori distribucije: Kako se LockBit 5.0 širi
Operateri LockBita oslanjaju se na različite metode zaraze kako bi maksimizirali doseg. Ransomware se obično širi putem:
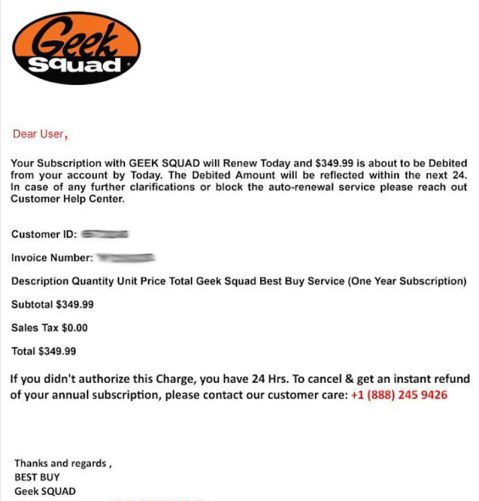
Zlonamjerni privitci e-pošte ili poveznice koje se predstavljaju kao legitimni dokumenti. Lažne ili kompromitirane web stranice, uključujući lažne portale za tehničku podršku. Iskorištavanje nezakrpljenih softverskih ranjivosti. Zlonamjerne reklamne kampanje, piratski softver i ilegalni generatori ključeva. Peer-to-peer mreže, programi za preuzimanje trećih strana i neprovjerene trgovine aplikacija. Ovaj višestruki pristup omogućuje napadačima da ciljaju i pojedince i poslovne sustave, povećavajući vjerojatnost široko rasprostranjene štete.
Jačanje vaše obrane od ransomwarea
Obrana od sofisticiranog ransomwarea poput LockBit 5.0 zahtijeva proaktivne i slojevite sigurnosne mjere. Korisnici i organizacije trebali bi usvojiti kombinaciju tehničkih zaštitnih mjera i praksi sigurnog pregledavanja. Neke od najučinkovitijih strategija uključuju:
Redovito ažurirajte sustave : Pravovremeno instalirajte zakrpe za operativni sustav i softver kako biste uklonili ranjivosti koje se mogu iskoristiti.
Koristite snažnu zaštitu krajnjih točaka : Implementirajte pouzdana antivirusna rješenja i rješenja za detekciju krajnjih točaka sposobna identificirati napredne prijetnje.
Prakticirajte sigurno korištenje e-pošte i weba : Budite oprezni s neželjenim privitcima, poveznicama i preuzimanjima iz neprovjerenih izvora.
Održavajte izvanmrežne sigurnosne kopije : Pohranite kritične datoteke na sigurne, izvanmrežne lokacije kako biste osigurali oporavak bez plaćanja otkupnine.
Primijeni pristup s najmanjim privilegijama : Ograniči korisnička dopuštenja i segmentiraj mreže kako bi se spriječile potencijalne epidemije ransomwarea.
Omogućite višefaktorsku autentifikaciju (MFA) : Zaštitite račune od kompromitiranja putem ukradenih vjerodajnica.
Redovito educirajte korisnike : Obuka osoblja i pojedinaca za prepoznavanje pokušaja krađe identiteta (phishinga) i socijalnog inženjeringa je ključna.
Završne misli
LockBit 5.0 naglašava kako ransomware skupine kontinuirano usavršavaju svoje alate za maksimalan učinak. Njegova sposobnost šifriranja cijelih okruženja, izbjegavanja analize i vršenja psihološkog pritiska na žrtve čini ga posebno destruktivnom prijetnjom. Najpouzdanija obrana je prevencija, kombinirajući ažuriranu tehnologiju, otporne strategije sigurnosnog kopiranja i svijest korisnika. Implementacijom ovih slojevitih sigurnosnih mjera, korisnici i organizacije značajno smanjuju svoje šanse da postanu žrtve razornih ransomware napada.
System Messages
The following system messages may be associated with LockBit 5.0 ransomware:
~~~ You have been attacked by LockBit 5.0 - the fastest, most stable and immortal ransomware since 2019 ~~~~
>>>>> You must pay us.
Tor Browser link where the stolen infortmation will be published:
-
>>>>> What is the guarantee that we won't scam you?
We are the oldest extortion gang on the planet and nothing is more important to us than our reputation. We are not a politically motivated group and want nothing but financial rewards for our work. If we defraud even one client, other clients will not pay us. In 5 years, not a single client has been left dissatisfied after making a deal with us. If you pay the ransom, we will fulfill all the terms we agreed upon during the negotiation process. Treat this situation simply as a paid training session for your system administrators, because it was the misconfiguration of your corporate network that allowed us to attack you. Our pentesting services should be paid for the same way you pay your system administrators' salaries. You can get more information about us on wikipedia hxxps://en.wikipedia.org/wiki/LockBit
>>>>> Warning! Do not delete or modify encrypted files, it will lead to irreversible problems with decryption of files!
>>>>> Don't go to the police or the FBI for help and don't tell anyone that we attacked you. They will forbid you from paying the ransom and will not help you in any way, you will be left with encrypted files and your business will die.
>>>>> When buying bitcoin, do not tell anyone the true purpose of the purchase. Some brokers, especially in the US, do not allow you to buy bitcoin to pay ransom. Communicate any other reason for the purchase, such as: personal investment in cryptocurrency, bitcoin as a gift, paying to buy assets for your business using bitcoin, cryptocurrency payment for consulting services, cryptocurrency payment for any other services, cryptocurrency donations, cryptocurrency donations for Donald Trump to win the election, buying bitcoin to participate in ICO and buy other cryptocurrencies, buying cryptocurrencies to leave an inheritance for your children, or any other purpose for buying cryptocurrency. Also you can use adequate cryptocurrency brokers who do not ask questions for what you buy cryptocurrency.
>>>>> After buying cryptocurrency from a broker, store the cryptocurrency on a cold wallet, such as https://electrum.org/ or any other cold cryptocurrency wallet, more details on https://bitcoin.org By paying the ransom from your personal cold cryptocurrency wallet, you will avoid any problems from regulators, police and brokers.
>>>>> Don't be afraid of any legal consequences, you were very scared, that's why you followed all our instructions, it's not your fault if you are very scared. Not a single company that paid us has had issues. Any excuses are just for insurance company to not pay on their obligation.
>>>>> You need to contact us via TOR sites with your personal ID
Download and install Tor Browser https://www.torproject.org/
Write to the chat room and wait for an answer, we'll guarantee a response from us. If you need a unique ID for correspondence with us that no one will know about, ask it in the chat, we will generate a secret chat for you and give you ID via private one-time memos service, no one can find out this ID but you. Sometimes you will have to wait some time for our reply, this is because we have a lot of work and we attack hundreds of companies around the world.
Tor Browser link for chat with us:
-
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
>>>>> Your personal identifier to communicate with us ID: - <<<<<
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
>>>>> Advertising:
Want a lamborghini, a ferrari and lots of titty girls? Sign up and start your pentester billionaire journey in 5 minutes with us.
-
After registration, you will receive the most flawless and reliable tools for encrypting almost all operating systems on the planet and a platform for negotiating with attacked companies.
Version: ChuongDong v1.01 | x64
Technical Analysis of LockBit 5.0
The LockBit 5.0 Windows version was found to have a better user interface with clean formatting for affiliates compared to previous versions.
It describes various options and settings for executing the ransomware, including basic options like specifying directories to encrypt or bypass, operation modes such as invisible mode and verbose mode, notes settings, encryption settings, filtering options and examples of usage.
"The detailed commands and parameters illustrate the flexibility and customization available to the attacker," the researchers commented.
Upon execution, the ransomware generates its signature ransom note and directs victims to a dedicated leak site. The infrastructure maintains LockBit's established victim interaction model, featuring a streamlined "Chat with Support" section for ransom negotiations.
Notably, the variant adds randomized 16-character file extensions to files following encryption, further complicating recovery. LockBit 5.0 also omits traditional markers at file endings, making analysis harder.
The malware deploys other anti-forensic techniques. This includes patching the EtwEventWrite API by overwriting it with a 0xC3 (return) instruction, disabling Windows Event Tracing capabilities.
As with previous LockBit versions, the new iteration uses geolocation checks, terminating execution when detecting Russian language settings or Russian geolocation.
The features observed in the Windows version were similar to those in the Linux and ESXi variants analyzed.
The ESXi variant specifically targets VMware virtualization infrastructure, which the researchers said represents a "critical escalation" in LockBit's capabilities.
This is because ESXi servers typically host multiple virtual machines, allowing attackers to encrypt entire virtualized environments with a single payload execution.
|