Rektware Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | September 17, 2018 |
| Last Seen: | July 23, 2019 |
| OS(es) Affected: | Windows |
The Rektware Ransomware is an encryption ransomware Trojan. There is very little to differentiate the Rektware Ransomware from the countless other variants of this hoax that exist currently. The Rektware Ransomware, like most other encryption ransomware Trojans, is designed to take the victim's data hostage, making it inaccessible. Then, a ransom payment needs to be done in exchange for the decryption key needed to restore the affected files. It is crucial that you to take precautions against threats like the Rektware Ransomware, such as being aware of the common ways in which the Rektware Ransomware is distributed and ensuring that your data is backed up and protected.
Table of Contents
How the Rektware Ransomware is Delivered
Threats like the Rektware Ransomware can be delivered to the victims in many ways. Some examples of these include the use of corrupted spam email attachments, as well as attack websites. The Rektware Ransomware is often delivered on peer-to-peer sharing websites and other potentially unsafe online locations. Because of this, learning how to handle email attachments safely and to avoiding shady websites and online content you can prevent numerous parasite invasions.
How the Rektware Ransomware Carries Out Its Attack
The Rektware Ransomware, like most encryption ransomware Trojans, is designed to take the victim's files hostage. The Rektware Ransomware uses a strong encryption algorithm to make the victim's files inaccessible, typically targeting the user-generated files. Next, there are examples of the files that threats like the Rektware Ransomware may target in these attacks:
.jpg, .jpeg, .raw, .tif, .gif, .png, .bmp, .3dm, .max, .accdb, .db, .dbf, .mdb, .pdb, .sql, .dwg, .dxf, .cpp, .cs, .h, .php, .asp, .rb, .java, .jar, .class, .py, .js, .aaf, .aep, .aepx, .plb, .prel, .prproj, .aet, .ppj, .psd, .indd, .indl, .indt, .indb, .inx, .idml, .pmd, .xqx, .xqx, .ai, .eps, .ps, .svg, .swf, .fla, .as3, .as, .txt, .doc, .dot, .docx, .docm, .dotx, .dotm, .docb, .rtf, .wpd, .wps, .msg, .pdf, .xls, .xlt, .xlm, .xlsx, .xlsm, .xltx, .xltm, .xlsb, .xla, .xlam, .xll, .xlw, .ppt, .pot, .pps, .pptx, .pptm, .potx, .potm, .ppam, .ppsx, .ppsm, .sldx, .sldm, .wav, .mp3, .aif, .iff, .m3u, .m4u, .mid, .mpa, .wma, .ra, .avi, .mov, .mp4, .3gp, .mpeg, .3g2, .asf, .asx, .flv, .mpg, .wmv, .vob, .m3u8, .dat, .csv, .efx, .sdf, .vcf, .xml, .ses, .qbw, .qbb, .qbm, .qbi, .qbr , .cnt, .des, .v30, .qbo, .ini, .lgb, .qwc, .qbp, .aif, .qba, .tlg, .qbx, .qby , .1pa, .qpd, .txt, .set, .iif, .nd, .rtp, .tlg, .wav, .qsm, .qss, .qst, .fx0, .fx1, .mx0, .fpx, .fxr, .fim, .ptb, .ai, .pfb, .cgn, .vsd, .cdr, .cmx, .cpt, .csl, .cur, .des, .dsf, .ds4, , .drw, .eps, .ps, .prn, .gif, .pcd, .pct, .pcx, .plt, .rif, .svg, .swf, .tga, .tiff, .psp, .ttf, .wpd, .wpg, .wi, .raw, .wmf, .txt, .cal, .cpx, .shw, .clk, .cdx, .cdt, .fpx, .fmv, .img, .gem, .xcf, .pic, .mac, .met, .pp4, .pp5, .ppf, .nap, .pat, .ps, .prn, .sct, .vsd, .wk3, .wk4, .xpm, .zip, .rar.
Once the victims have their files encrypted, they will become inaccessible. At this point, there's not too much that can be done to mitigate the damage. However, computer users can take precautionary methods to not be the victim of another threat, since the encryption used in these attacks is generally impossible to crack with current technology.
Dealing with a Rektware Ransomware Attack
Threats like the Rektware Ransomware work by demanding ransom payments after the victim's files have been encrypted. They typically ask for a ransom to be paid using cryptocurrency. Computer users should not pay these kinds of ransoms, which allow criminals to continue creating and distributing threats like the Rektware Ransomware. The best protection against the Rektware Ransomware is to have file backups stored in a safe location, such as the cloud or on an external memory device. Having file backups ensures that computer users can restore their data without having to negotiate with criminals. Apart from file backups, it is recommended that computer users have strong security software that can intercept or remove the Rektware Ransomware completely from a target computer before the victim's files are compromised.
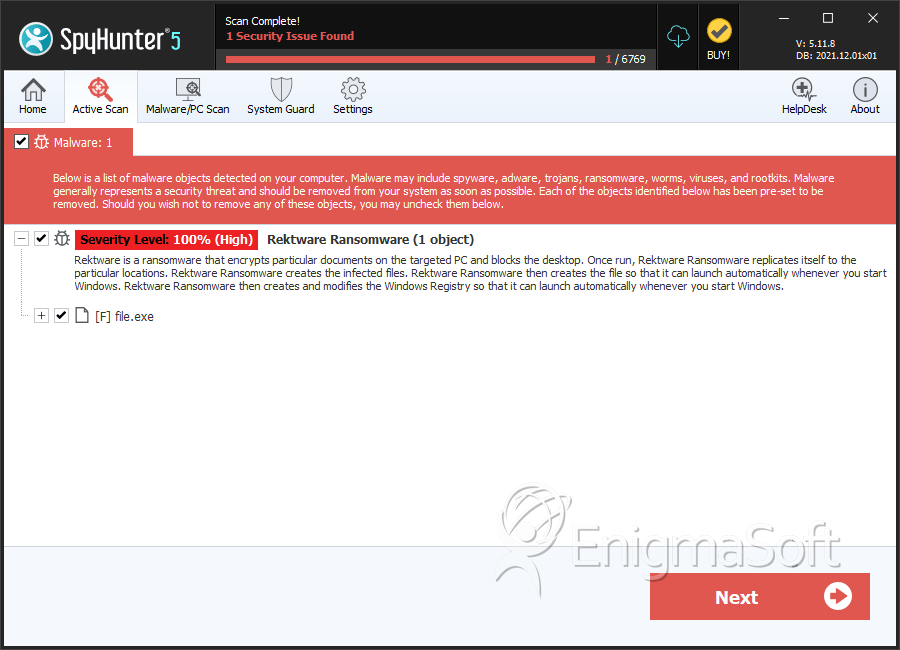
SpyHunter Detects & Remove Rektware Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 1d4fff59eaa40773284e76d9371dd701 | 1 |

