RansomeToad Ransomware
The RansomeToad Ransomware is a file-locker Trojan without a family. The RansomeToad Ransomware can stop files from opening on your computer by encrypting them and creating Russia-centric ransom notes that resemble the WannaCry Ransomware pop-ups. Users should always have safe backups for a ransom-free recovery route, besides using appropriate security solutions for removing the RansomeToad Ransomware.
Want to Get Crying over Files Again
Although its campaign was sparser in longevity than those of real file-locker Trojan families, WannaCry Ransomware is a seminal Trojan that leaves ripples – at least, aesthetically – throughout the threat landscape. The RansomeToad Ransomware is the latest copycat that imitates the looks of that notorious Trojan and couples it with an effective data-blocking scheme. Unusually, its monetary demands are trivial, which suggests that it's still-in-development.
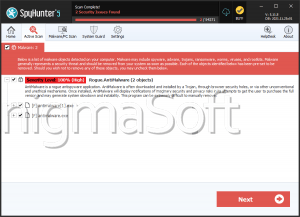
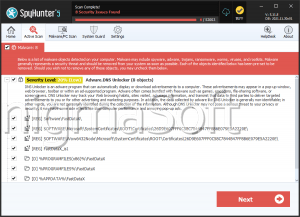
The RansomeToad Ransomware is one of a vast array of .NET Framework-dependent Trojans for Windows. It leverages encryption for blocking files, which doesn't impact system components, but will stop documents, images and similarly-personal or work media formats from opening. Like almost all threats that run this attack in the modern-day, the RansomeToad Ransomware also supplements it with a tag that it adds as another file extension (a la 'example.doc.rtcrypted').
When it comes to its pop-up alert (an HTA window), the RansomeToad Ransomware is somewhat mistakable for WannaCry Ransomware. It uses a similar red background and padlock icon and includes a built-in decryptor that the victim pays a ransom for accessing. The meager ransom amount – 65 Russian rubles, less than a dollar – highly suggests that the RansomeToad Ransomware is either a test run or a joke Trojan. Still, malware experts warn that its file-locking feature is no less functional than its more expensive counterparts.
Forcing a Trojan to Hop Along Elsewhere
Users have the same defenses against the RansomeToad Ransomware as the hundreds of almost identical Windows threats that use encryption as a means to extorting money. Backups are essential, which users never should save on a local or vulnerable location. Although malware experts can't confirm the RansomeToad Ransomware's wiping the Restore Points or other backups, most Trojans of its kind will take these precautions.
The RansomeToad Ransomware's samples circulate with the name of 'Povlsomware' currently. Web surfers may encounter infection attempts through compromised ad networks, tactics such as fake software updates, torrents, or e-mail attachments. Many criminals will also compromise a target by brute-forcing their credentials, which is arguably the admin's blame for an unwisely-chosen password ('admin1,' 'password1234,' etc.) entirely.
Along with the necessity of backups, malware experts recommend turning off sometimes-threatening features when possible. JavaScript, Flash, and Java may leave users' browsers vulnerable to attacks, as do macros in Word documents or Excel spreadsheets. Anti-malware tools may block drive-by-downloads and remove the RansomeToad Ransomware but can do nothing for any already-locked media.
The RansomeToad Ransomware might be an unexceptional example of ransoming Trojans at work, but even the lowest-effort Trojans are threatening to unprotected files and PCs. Users should take the RansomeToad Ransomware as seriously as the Trojans that expect tens of thousands of dollars in ransoms since there's no telling what it's price will be tomorrow.