PUP.Pulse Browser
Table of Contents
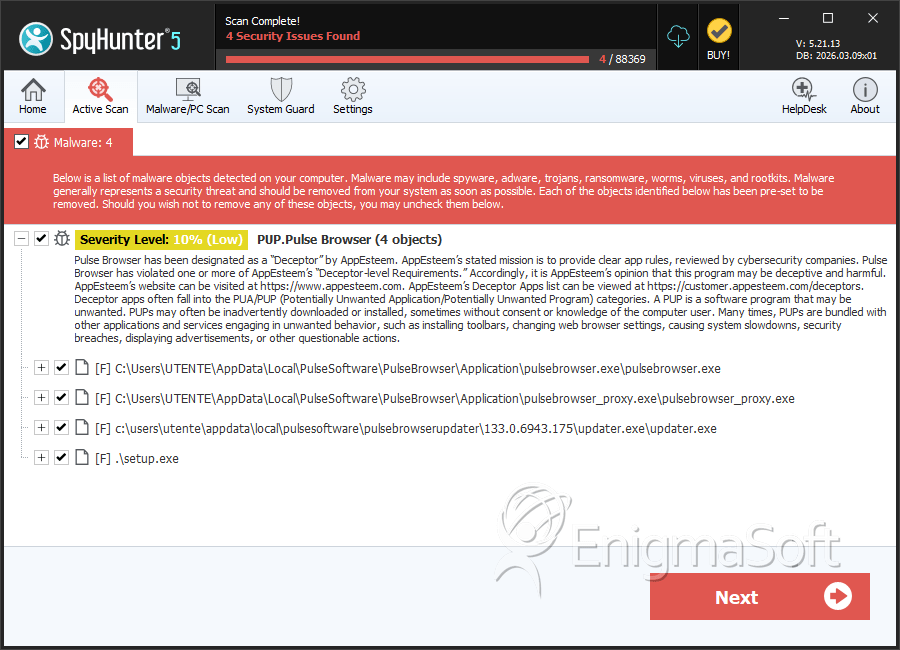
SpyHunter Detects & Remove PUP.Pulse Browser
Analysis Report
General information
| Family Name: | PUP.Pulse Browser |
|---|---|
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
8f4c68a6393beaeb45520e216d21a247
SHA1:
cbf5ae82c0e870cddd4c479d484451cfe899c659
SHA256:
4A9DC042B9EC5ED100A4C6B1FBD33781F09122789D12E477A678ADC7A4BDC121
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
e4e8ff12eb10f2ab49665709da662810
SHA1:
5699d8b4b31eb92d0294b0a1772dd2d57c405d05
SHA256:
033D33E007D717F5FC10C36FEDA292A4743432718374AB1327139EBFC55A0167
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
3b000dd9ae1362328e0a268d77ed2ee8
SHA1:
20ef103a670135c6e5530c1de505f700cd1a6a23
SHA256:
DC47A090E70A6537964EF5B9C9D9C4E7C316EB26D1C5B2E8B7EC24EC335496C9
File Size:
17.57 KB, 17568 bytes
|
|
MD5:
3e82697dd498168f25394fda4e017b35
SHA1:
c132d3b10637feec73a9c06531e3cc5863a1a8c6
SHA256:
30E43FA956C485E7095A923D3C7D60699BA121A590D28651D69870AB628F6525
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
f841f24c0d9baea8db3572eb89029e14
SHA1:
b739f55aa03e6fd33ddd7288d317fb224d64fcb6
SHA256:
5B5D5D4C6C4FBAF78C61395FD63F9C950ABDB9C7D9061E6BAAB64BB2820ED7A6
File Size:
6.53 MB, 6526112 bytes
|
Show More
|
MD5:
8df214c7234c78f598c01f70e037fd1a
SHA1:
357e4c2ebf40e6cea267d49cbb628d5a63b80336
SHA256:
441A4C4AA368B1227BA3519FFC5E5144A5DE4B385F7B01994DCBFF7D04422576
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
d059899252db27b6d5a4d50cfea3df9d
SHA1:
7707d2794d9afea6204827fb9892dc221f8911a8
SHA256:
53276B59AA34F33E7437D5A0B4EEA396F6F4125A4EB471DAE35E3B878E87E6F4
File Size:
17.57 KB, 17568 bytes
|
|
MD5:
471ec618ba629c2f677ff3cd29ca929e
SHA1:
cb734788eb26657f470714245db1c87ce685989a
SHA256:
05CE300D02C67B333EB4774E53A017058CCDB1D5A6CA406C085B3B30015B8537
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
37d6f90b8ca787533c9593dd43a23cc7
SHA1:
21741e31ba0399fc8648f554d400700c3813fe51
SHA256:
1A401F16EC210A29C8EBFB69FEEC2206753395C3D72F68BCA7E1BCEA50831D7F
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
b8d971ef59c05c3cc929ca5893835799
SHA1:
ff29284793a83d9373bd6cb9ac484537fd0ab177
SHA256:
4C0D73D34FF35C623DE7B6EC5BD734D38A28135C796A678622831D4EAAEB8656
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
d862a828448c6e9171f602f597507ccc
SHA1:
5114e54cbee01ea2f314ff2a13a27379e7214726
SHA256:
F8B03A23597976EC08A753E2244B3F47F067B18C8B72101DFA3CEDB943D483DA
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
6a7578dfb3e4e30dba6e8c1d53914157
SHA1:
ae5b14cc44529ddd870fa49eec54d2af4129ebd9
SHA256:
C0D322B5A84E27D5D75F8CDDADF225C9460ECF92116F04EBE06A14C693B33281
File Size:
7.53 MB, 7526960 bytes
|
|
MD5:
84bbbb0012f005c4275463e7bcb9f3ec
SHA1:
65e79c4ea3a5a4ef7ad4a19d5dbe0523b1679e5d
SHA256:
3B83AC47AD3941B1EF8BA004A82D5AD42217C2AA076347EDC8D9367EBB43CA92
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
f23eafcc0cbb0e1e2750af84082247f7
SHA1:
3875c75c0eb1097ee651af0eb06ae98a250a4a97
SHA256:
8E003E091AE7B1B9F7988CF85F419C9453A44443BE890B7B977CAF077F96002C
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
0f056e492a3dcbec685a572efe5ab257
SHA1:
b8bf666c105dd640e5e34cfa32fc8120501a8963
SHA256:
7C1CDF0C68B1089E29ABE9C1C76D43DD456476D4D8BBF4963B36D605A876AD0D
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
410cb7d7454e37a294a3abf978ccaf0f
SHA1:
3eb282d109b8147f18af4a8a16ac7c4bcec9e105
SHA256:
4FCB6AABF22E2F79427DB17B95564E91760B1F622760B54063258233CCD7D229
File Size:
17.57 KB, 17568 bytes
|
|
MD5:
71738fe64bb609b599514f9fcbbcfe50
SHA1:
eb8e26c556fae15cf656c21b7c72b4022127e2ff
SHA256:
FD34CD69FA89A660BBEDCBF150CC80EED80469C5E46081E93C5D041A1FFFEC6B
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
d36e9bacc5ee36dedaf1efe69a05463c
SHA1:
ca62856a7244b33747ad3b24601711648336a2f9
SHA256:
6112A5629A7DC2B3FC365350549CE45C0A0B7F50BBCF1E2779B5D28DC91FE069
File Size:
7.53 MB, 7526960 bytes
|
|
MD5:
5c02ffcec7183dbbc110ad4ee775261b
SHA1:
e6cf78ff53e71cdffd59b0e9e3ef634da89f54c1
SHA256:
A68226CDEE57CEA0DC1DEF6FFFC649ED134551F2761F1E8C5EA2B483483FA893
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
4d5c1daee646debf320ab1026bd6ef10
SHA1:
957806946123b442a27d7bea5170a43b47d47030
SHA256:
9A871B06AAC4A2635AB84F04FC6DD9933417AE8D1D3571FB4DF17DD283FED4FB
File Size:
17.57 KB, 17568 bytes
|
|
MD5:
7f02995e876ba0e23b11eb6ae9d5e006
SHA1:
f6a8236368014acd20921521e8e0242d11ae1cb9
SHA256:
50DF9E88DD9C1FCAB9B49246E40019B77368C325367DAA3764CA9489D97DB6A4
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
da2e48776af12461b8d7425a45b03dcc
SHA1:
d25b37550bf9461720642406ecd8acc2b1428bfc
SHA256:
34BDA7CE48AD1C65DC3704C37AB6E63561B52E9E4140A90D59546D039A071608
File Size:
17.57 KB, 17568 bytes
|
|
MD5:
1ac4b16d99a1301dae4480da221a5129
SHA1:
d21f7d9d7d9a4be5a18a9e4feb8b3fcf835f8a21
SHA256:
809F93D93AF1B0662A372DE503AA606118F24F56DD9217A567E37E91E6C3B329
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
1aedd7145ef4d2810b461727d5e638f1
SHA1:
2ebc97eff507cbbf9921d6b5bde884d6d3dc2f4f
SHA256:
9F79ECD3B5490D41D432EDC40F39FC2BB81A23792310B700D9282AF284D9AD20
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
8cf7202a7b8c7f8cee7875184c136892
SHA1:
26e1e85420795a18d4df524332f51645e88e0718
SHA256:
5D2C9272E374A35781D2580D4BDBE6C33F81B904A58D23D427A491F3A6BD322D
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
2f10ca7f3dad1ae35c4d14baf648516b
SHA1:
e441234cc429f9f539468dd646294103103dce49
SHA256:
6433BA6789DBA7B2FCBD44D4E222E2AA41BDEFB17D4860FF0CD0111429402288
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
59c17d561645fcb25ae0bf6751a81de6
SHA1:
d1fb1405855af19eeb1548ef3f11d0aa1ae77af3
SHA256:
D47F4F0F2CBD2BFA37EA6FDCED26F61DB22D7711B84F595D1F4AB2E98673ECCC
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
15e788880bc31f1ca4dda4b53557a983
SHA1:
b1e6acfcbd578da75a39780af7352c9a1349a5c5
SHA256:
A88F5076F26200C6B25C21F147C5B750D33921F7374C63AE6D981BBD7441C007
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
c99d75d1c7a7e2e819eb9b6e62baa9e7
SHA1:
627d1e6757494ec094b44d1aff5637a7e4e3d808
SHA256:
3A70BF16915CDB1A69CA63EA57055C98BA4B1D9196F43168CC4B27AB6E889B44
File Size:
7.53 MB, 7526960 bytes
|
|
MD5:
8b69f4fa1c0db2baa0bb04ab7ac715be
SHA1:
3a66dba184f73264f7fd037b10d5dd00e2a12845
SHA256:
BCE853A2266A819B93787C805112A4C6499C27307E46E7F97CC404AABB97C72B
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
26b661d1efc8fc5dc2516c62d388de3b
SHA1:
eaabeb00249f9bc0dd4c083ba2a279df51f2246d
SHA256:
DF5337E836F5B982492EEE56A136242FD64D4EB0D41DECE6FFCD5799EDC5274E
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
c73245f9bcf21e7d5e83e7c271599c7b
SHA1:
57ecbed4a52dce8553c0d708ef4bfed510c22d3b
SHA256:
4F82477EE2B688CEF07F8763418EDF60A3B027119977517CFF65ADC933B91E18
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
10c52f53bdc2b916917d4f6c05695791
SHA1:
2d8cec2fc15965b62fd3511b75901b9ed1830fdc
SHA256:
D44393340C2167CFB4099EB1A98A58A51802B227834D11399AD513A5CB8AAB22
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
a83c64a2ce818c55a39a22bf81300b3c
SHA1:
de8269a573c2154bbd194780822b9c69378086d2
SHA256:
6166CEAC7FB5C5A34E873CA0F6837677A41D5DA380DA4F27B60DB9C21BD3A4E9
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
d368e9e6705196504fec975da91558f0
SHA1:
97b4ee6761a2f67346ad7c506c165c6a8b1614e0
SHA256:
D144EE8CCC8E81067994D819DC73273B741BE765616ED7C36FB8A4265B0CADFD
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
91998c0fed074bd9c3900a7fdd076b60
SHA1:
f8deaababaa5464165d1bcb7a8b42e433ba5961d
SHA256:
763C6E37919DA9A08B6C9B95E3F0BEE1B15B56E25E7BE7371F2C075492400EE3
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
053dc8e38a0049d38351f755f0d9d3af
SHA1:
66e22419c95402cedb21a6b859a693fd867b3305
SHA256:
BFC4BCF87C249D5D5366DBE33AF545831470755F2FA4BFD92A07161DC2EADF29
File Size:
7.53 MB, 7526448 bytes
|
|
MD5:
3e0c5bd3a698f3cdc238f4a324fe67c3
SHA1:
fa5ce162d2e6b79bc510e35d481bb3be194994c9
SHA256:
0A7648EFD72DB34AE9A1DEA448867B7A2B9DDFC28191066FFF23472C6F6954F2
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
905ce5179af78bfcfe6e4d06a5b306b5
SHA1:
05ca37cdef06cd63069b7f2e2e21c9c6946ac9c6
SHA256:
F748A9DE3FB6F642B897A938107FAEFA92931391D844F181E89B1E9F7A34B23F
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
347fb965c263a9884ff52f4df2410586
SHA1:
15ef2d920e2bcde102e8bb5994bfc13db34758a5
SHA256:
ADCB4C94D5A6C58024C51028F3A52E1EDFE48823179851CA65131E232168855D
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
11007ade7eca456f1765efa90b3ad94d
SHA1:
582435e3cd440eb5791d81327274b7e4e59af950
SHA256:
7F2A31AFD7669E3A6AE7FFA2615B5CC5C8708F1F98D2BC81AE43F4B565A7A5E5
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
2d3330654a808911ee12aad8b3a26de7
SHA1:
ae71102cda834e01ab65c1ba7027a43205047f67
SHA256:
FC80BD87F7841E8066427136E8F425B9AC8D40D0D2045CB333FAFD5A06AC9E17
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
31de112a1054fbd2511264713a5fb6b6
SHA1:
fe6f26741904e74b636cdf8c2a6e69c8d196d81a
SHA256:
600F0F4D8EB470044242F99D358536B93A923758718EA5A91BB600056EAB546C
File Size:
6.10 MB, 6100080 bytes
|
|
MD5:
67d0f4694cdb991afa9298ea55a78df1
SHA1:
063dd70d1697a2c25bf2af9d52e3f14649707cae
SHA256:
5321CD975BC35A2612D83777344059974F9BCD4376DFA791692655F837D913DF
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
0383651dea00def8a85fca8fe3e320b8
SHA1:
a5a8ddf45e475f3439639cac3ce7a790425e5f44
SHA256:
45FA766BA9323DC8061CF290DC3B0B920A3482ED71265D0572862B8B433DBA5C
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
81eca578365f965782f63391ed318a84
SHA1:
197cd0084de718f4478eb575a2b4aed752350e86
SHA256:
686287F33FD235CEB1FFD45F8D5173F54DCC9CE6B864010051E9D0A5BCAD15CE
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
386967bdd6b33eee4bd1abd62eed9c0d
SHA1:
eb0ac2f8bfed6589d888be651b670169fb186295
SHA256:
4872FB892B8BD631A9843EDDC6186248361E2FD0D92AB1E72049D339F5341288
File Size:
7.53 MB, 7527472 bytes
|
|
MD5:
35cc0c12c4223c210a98993440f3e834
SHA1:
aa9793b00b6b0adb450c320d3a19e89f98e073a3
SHA256:
5BEDAC476CFDA10694E5285E1DA2CDBF70BEDD91141DD9376C67C7EACB829E6F
File Size:
7.53 MB, 7527472 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File has exports table
- File has TLS information
- File is 64-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| Company Short Name |
|
| File Description |
|
| File Version |
Show More
|
| Internal Name |
|
| Last Change |
|
| Legal Copyright |
|
| Official Build | 1 |
| Original Filename |
|
| Product Name |
|
| Product Short Name |
|
| Product Version |
Show More
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Alabama Technology USA, LLC | Sectigo Public Code Signing Root R46 | Root Not Trusted |
File Traits
- 2+ executable sections
- HighEntropy
- Installer Version
- ntdll
- x64
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 18,154 |
|---|---|
| Potentially Malicious Blocks: | 8 |
| Whitelisted Blocks: | 16,804 |
| Unknown Blocks: | 1,342 |
Visual Map
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
0
?
?
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
0
?
0
?
0
?
0
0
?
0
0
0
0
?
0
0
0
?
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
?
?
?
0
0
0
0
0
0
0
?
0
0
0
?
?
0
?
0
0
?
?
?
?
0
?
0
0
0
?
?
?
0
?
0
0
?
?
?
?
0
?
?
?
0
?
?
?
0
?
?
?
0
0
0
0
0
?
0
0
0
0
?
0
?
?
0
0
0
?
0
0
0
0
?
0
0
0
0
?
0
0
?
0
?
0
?
?
?
?
?
?
?
?
0
0
0
0
0
?
0
?
0
0
0
0
0
0
0
0
0
?
?
0
0
0
?
0
?
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
?
?
?
?
?
?
0
0
0
0
0
0
?
?
0
?
?
0
0
0
0
0
0
?
0
0
?
?
?
?
0
0
0
0
0
0
?
0
0
0
?
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
0
0
?
0
0
0
0
0
0
?
?
0
0
0
0
0
?
0
0
?
?
?
?
?
?
?
0
?
?
?
0
?
?
0
?
?
?
0
?
?
0
?
0
?
0
?
0
?
0
?
0
0
?
0
0
0
?
0
0
?
?
0
0
0
?
0
0
0
0
0
?
0
?
?
0
0
0
0
0
0
?
0
0
?
?
0
0
0
0
0
?
0
?
0
?
?
?
?
?
0
0
0
0
0
?
0
?
?
?
?
?
?
?
?
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
0
?
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
?
0
0
0
0
0
?
0
0
0
?
0
0
0
0
0
0
0
0
0
0
?
0
0
?
?
0
0
?
?
0
?
0
0
?
?
?
0
0
0
0
0
0
?
0
?
?
0
0
0
?
0
0
0
0
?
0
?
0
0
?
0
0
?
0
?
0
?
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
?
?
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
?
0
?
?
0
?
0
0
0
0
0
0
0
?
0
0
0
0
?
0
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
?
0
0
0
0
?
0
?
0
0
?
?
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
?
0
?
0
0
0
0
?
0
0
0
?
0
0
0
?
?
0
0
?
0
0
0
?
?
0
0
?
0
0
0
0
0
0
?
0
?
?
?
?
?
?
0
0
?
?
?
0
0
0
?
0
0
0
0
0
0
0
?
0
0
0
0
0
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
?
?
0
0
0
0
0
0
?
0
0
?
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
?
?
?
0
0
0
0
0
?
?
?
?
0
0
?
0
0
?
0
0
?
?
?
?
0
?
?
?
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
?
?
0
0
0
0
?
0
0
?
0
0
?
0
0
?
0
0
0
?
0
?
?
0
0
0
0
0
?
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
?
?
?
?
?
0
0
0
0
?
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
?
0
0
0
?
0
0
0
0
0
?
?
?
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
?
0
?
?
0
0
0
0
0
0
0
0
0
?
?
?
?
0
0
0
?
0
0
0
0
0
0
0
?
?
0
0
0
0
?
?
?
0
0
0
0
0
0
0
0
0
0
?
0
0
?
?
0
?
?
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
0
?
0
?
?
0
0
0
0
0
?
?
?
?
0
0
0
?
?
0
0
0
0
?
0
0
?
0
0
?
?
0
0
0
?
0
0
?
?
?
?
0
0
0
0
?
0
?
0
?
?
0
0
?
?
?
0
?
?
?
?
?
0
?
?
?
0
?
?
?
?
?
?
0
?
?
?
?
0
0
0
0
0
?
?
?
?
0
0
0
0
0
0
?
?
0
?
0
?
?
0
0
?
?
0
?
0
?
0
?
0
0
?
0
0
?
?
0
0
0
?
?
0
0
0
0
0
0
?
?
?
?
?
0
0
0
?
0
0
?
0
0
?
?
?
?
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
?
?
0
0
0
0
0
?
0
?
0
0
0
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
?
?
?
?
0
?
?
?
0
?
?
0
0
0
0
0
?
?
?
0
?
0
0
0
?
0
0
?
?
?
?
0
0
0
?
?
0
?
?
0
0
0
?
0
0
?
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
?
0
0
0
0
0
0
?
?
?
?
0
?
0
0
0
0
?
?
?
?
0
0
?
?
?
?
0
?
0
?
0
?
?
0
?
0
?
0
0
?
?
0
?
0
?
0
0
0
?
?
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
0
?
0
?
0
0
0
0
0
0
0
0
0
0
0
0
...
Data truncated
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| \device\namedpipe\crashpad_5012_zahehbsmgjfvhoac | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| \device\namedpipe\crashpad_5012_zahehbsmgjfvhoac | Generic Read,Write Data,Write Attributes,Write extended,Append data,LEFT 524288 |
| c:\users\user\appdata\local\pulsesoftware\pulsebrowserupdater\133.0.6943.176\crashpad\metadata | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| User Data Access |
|
| Process Terminate |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
c:\users\user\downloads\b739f55aa03e6fd33ddd7288d317fb224d64fcb6_0006526112 c:\users\user\downloads\b739f55aa03e6fd33ddd7288d317fb224d64fcb6_0006526112 --crash-handler --database=C:\Users\Rfmsxqrg\AppData\Local\PulseSoftware\PulseBrowserUpdater\133.0.6943.176\Crashpad --url=https://pulsebrowser.com/ --annotation=prod=PulseBrowserUpdater --annotation=ver=133.0.6943.176 --initial-client-data=0x298,0x274,0x2a0,0x29c,0x2a4,0x7ff6ca62454c,0x7ff6ca624558,0x7ff6ca624568
|
