PUP.Gamehack.BBH
Table of Contents
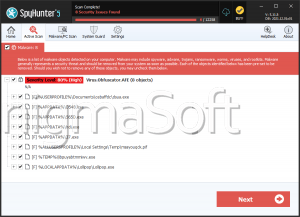
Analysis Report
General information
| Family Name: | PUP.Gamehack.BBH |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
1a6a3d9dd478a55df88729df3276dde2
SHA1:
72c2f030a87d5fd946ba1658b1b5c4b1da513dab
SHA256:
CCD38E070A0099F470C28B84513E88450437F8F4568BECBFD49725B923B5A82A
File Size:
358.40 KB, 358400 bytes
|
|
MD5:
a4a555f668695ebdab6ac626536e2653
SHA1:
e713c4252cd69a18a6af5b41702ccc011be92d69
SHA256:
089D8885CB3403A98C3E7D119C211BBD4021D01C53886C80A856AE98C4F91CB6
File Size:
257.54 KB, 257536 bytes
|
|
MD5:
1e5c7f27b90ba532eceb1a121241edb8
SHA1:
f980f2a026c33e23e7ad17e6dba4cb3d4e67306e
SHA256:
98C153B91E245A702EBC643FFB246E6E8DFB459D1ECE9433A523693B837F0F18
File Size:
400.38 KB, 400384 bytes
|
|
MD5:
3eb9fe3f1bbc4326a7fadd56fe303f3f
SHA1:
7481a24d6a4e3404c3a6c2695d4269b87de8ca20
SHA256:
D4451B6FE6A8D75804C7EECA966D8F7FEC20C9A65A0E3995543C25DC09689FEA
File Size:
255.49 KB, 255488 bytes
|
|
MD5:
66dc5616697a85ae9d35b9c5003046ee
SHA1:
cbeda24731374124f296e66213e512f713e9de31
SHA256:
008092F99A15BC83BD5C1ACCAEC9AC93F1BF07E059D3F49996A6AA348285237F
File Size:
2.08 MB, 2084352 bytes
|
Show More
|
MD5:
314c62dde09a14d1d0f553fa5a2bcabb
SHA1:
1ef76acb8c6a0089ae88cbc64efeea4ed8a30900
SHA256:
6CFB91F1EADD1D0B9E46A14E8FD1CD5B31DA8638244B85557144ED31AE1DA441
File Size:
283.65 KB, 283648 bytes
|
|
MD5:
3430e7377f94f5d333967c2aac45b154
SHA1:
201c27c2f5995202bf4ce4b39d91a14e94cbee1e
SHA256:
9D26AB909CC6816FFF4AB898270D645E81D0BF116E226B0C68C1D6C7CD3D2B38
File Size:
448.51 KB, 448512 bytes
|
|
MD5:
3fb90617f2078bb69666aca0cb63e0dd
SHA1:
2842ff0abd70639a3f3c0d186570a50e3452275c
SHA256:
84B361D4C0500B8EC44C7CA1CA9C8D311FF23BA56844AD1B568694F796D3AFCE
File Size:
414.21 KB, 414208 bytes
|
|
MD5:
7b73628136226584f732931ae8f098b8
SHA1:
c9132756d091c62061e441be96cc2915c8684f8c
SHA256:
0EEC15A64D675F435B3D7DE0A3F87FF25278E1B82D7BAC2BA1FE618B34F24C77
File Size:
257.02 KB, 257024 bytes
|
|
MD5:
31225ba70f69537c656a464ac64c9f50
SHA1:
30722d26510777af4ff37ff954560e5b911edede
SHA256:
A8ACDB0EE92DB8E91B07509485174DFC4E6A402AE1AA8E1C4C293EB73383638A
File Size:
1.54 MB, 1540608 bytes
|
|
MD5:
410bbe85053f26a49fcbd6b502ec55be
SHA1:
cc642535646ccc1b2346f429d871752e664e4281
SHA256:
289CC0453BDBA4AA678AF6D9265E7288EE7BF68481054DD62F225C49727D055B
File Size:
356.86 KB, 356864 bytes
|
|
MD5:
e8f1b119f45f64b3c7cb44c6e10cff9a
SHA1:
cfc1e7651958bae1bb1608ea0126cae45cc42509
SHA256:
7BFF2C1EF0D275A859BC9B3C0687F474217C29E9FDAE1BE88FDDEB5CD1543554
File Size:
284.67 KB, 284672 bytes
|
|
MD5:
c0aa44c718729e9d5430e65dc09593ca
SHA1:
70cc3c87bbfc909d4bd2a7463ad4cfb8d91232d8
SHA256:
76D9764B4634493656DBCE1DCD7922CA0DC4895946F1289D1CC8A8DF9BE55B62
File Size:
2.61 MB, 2613449 bytes
|
|
MD5:
15e83fa20a007426f2664568290968c8
SHA1:
a78158ec3449bc7fbc82140b9b287763b8ee9f52
SHA256:
937315682B82231BF9640BA261F4D783D2F44D067412CE9D9D1517B5D4A0C9FA
File Size:
276.99 KB, 276992 bytes
|
|
MD5:
7a32911932556eff2c5f1a10cff568e3
SHA1:
28f6c324b503fc953c9d92626024f1dcba40ec53
SHA256:
32B6C71A0785195DFBDBD0CC0D600A1A9CB4B450491531A9A1479416E6DA6C7C
File Size:
1.57 MB, 1571840 bytes
|
|
MD5:
56d0afd62f691f3968b535fc685206eb
SHA1:
c617ae670c22a7ae58237baa8a68f94eef82306b
SHA256:
646C3D10C22D0379EBAA12D481C6E6B88751B75D48ED1AACCD6FF74EBA6578F8
File Size:
550.91 KB, 550912 bytes
|
|
MD5:
59b7f185c7ec5416557ecbb2ddeabe77
SHA1:
e4d944bc84acb33791a3b012ff2077404cbd4993
SHA256:
138AB75BFE061DBF5C3A889CECDAB8C5D8F83AF5611D80325B264134A4DF041A
File Size:
287.74 KB, 287744 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is console application (IMAGE_SUBSYSTEM_WINDOWS_CUI)
- File is either console or GUI application
Show More
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name |
Show More
|
| Legal Copyright | MIT License |
| Original Filename |
Show More
|
| Product Name |
Show More
|
| Product Version |
|
| Update Url |
|
File Traits
- dll
- fptable
- HighEntropy
- VirtualQueryEx
- WriteProcessMemory
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 1,236 |
|---|---|
| Potentially Malicious Blocks: | 29 |
| Whitelisted Blocks: | 1,190 |
| Unknown Blocks: | 17 |
Visual Map
0
0
0
0
0
0
0
0
0
0
0
x
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
x
0
0
0
0
0
0
0
?
?
0
0
0
0
0
0
0
?
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
?
?
?
0
x
x
0
0
0
0
0
0
0
0
?
0
?
x
?
?
0
x
?
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
0
0
0
0
0
0
0
0
x
0
x
0
x
x
0
x
0
x
x
0
0
0
0
0
0
?
0
0
0
0
x
0
x
?
x
x
x
0
x
x
0
0
?
?
?
x
0
?
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
1
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
1
0
0
0
0
1
1
1
1
0
0
0
0
0
0
2
0
0
0
0
0
1
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
1
0
0
0
0
1
1
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
2
0
0
1
1
0
0
0
0
0
0
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Crack.K
- Gamehack.BBH
- Gamehack.HBB
- KillMBR.EE
- Qihoo.B
Show More
- Trojan.Agent.Gen.AAT
- Trojan.Agent.Gen.DE
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\downloads\__tmp_rar_sfx_access_check_2996515 | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\downloads\d3d8.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\downloads\d3d8.dll | Synchronize,Write Attributes |
| c:\users\user\downloads\scripts | Generic Write,Read Attributes |
| c:\users\user\downloads\scripts | Synchronize,Write Attributes |
| c:\users\user\downloads\scripts\global.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\downloads\scripts\global.ini | Synchronize,Write Attributes |
| c:\users\user\downloads\scripts\maxpayne2.widescreenfix.asi | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\downloads\scripts\maxpayne2.widescreenfix.asi | Synchronize,Write Attributes |
| c:\users\user\downloads\scripts\maxpayne2.widescreenfix.ini | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Show More
| c:\users\user\downloads\scripts\maxpayne2.widescreenfix.ini | Synchronize,Write Attributes |
| c:\windows\syswow64\rainbomizer\config.toml | Generic Write,Read Attributes |
| c:\windows\syswow64\rainbomizer\logs\28-03-2026.txt | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Shell Execute |
|
| Anti Debug |
|
| Process Manipulation Evasion |
|
| Keyboard Access |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\72c2f030a87d5fd946ba1658b1b5c4b1da513dab_0000358400.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\e713c4252cd69a18a6af5b41702ccc011be92d69_0000257536.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\f980f2a026c33e23e7ad17e6dba4cb3d4e67306e_0000400384.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\7481a24d6a4e3404c3a6c2695d4269b87de8ca20_0000255488.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\cbeda24731374124f296e66213e512f713e9de31_0002084352.,LiQMAxHB
|
Show More
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\1ef76acb8c6a0089ae88cbc64efeea4ed8a30900_0000283648.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\201c27c2f5995202bf4ce4b39d91a14e94cbee1e_0000448512.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2842ff0abd70639a3f3c0d186570a50e3452275c_0000414208.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\c9132756d091c62061e441be96cc2915c8684f8c_0000257024.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\30722d26510777af4ff37ff954560e5b911edede_0001540608.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\cc642535646ccc1b2346f429d871752e664e4281_0000356864.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\cfc1e7651958bae1bb1608ea0126cae45cc42509_0000284672.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\a78158ec3449bc7fbc82140b9b287763b8ee9f52_0000276992.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\28f6c324b503fc953c9d92626024f1dcba40ec53_0001571840.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\c617ae670c22a7ae58237baa8a68f94eef82306b_0000550912.,LiQMAxHB
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\e4d944bc84acb33791a3b012ff2077404cbd4993_0000287744.,LiQMAxHB
|