PUBG Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 3 |
| First Seen: | April 17, 2018 |
| Last Seen: | January 18, 2019 |
| OS(es) Affected: | Windows |
The PUBG Ransomware is an encryption ransomware Trojan that also includes a lock screen component. The PUBG Ransomware seems to be used to carry out a prank, although the PUBG Ransomware attack is executed by an effective encryption ransomware Trojan that can make the victim's data unusable. The PUBG Ransomware was first observed in the second week of April 2018, being used to carry out attacks against victims in the wild. The most common way of delivering the PUBG Ransomware to victims is through the use of corrupted social media messages or spam email attachments.
Table of Contents
How the PUBG Ransomware Attacks a Computer
The PUBG Ransomware seems to be related or inspired by the 'Player Unknown's Battlegrounds,' a game that is published by Bluehole Studio Inc. The PUBG Ransomware carries out a typical ransomware attack by encrypting the user-generated files with a strong encryption algorithm and changing the affected files' names by adding the file extension '.PUBG' to the end of the targeted files' names. The PUBG Ransomware uses the AES encryption in its attack, making the files encrypted by the PUBG Ransomware unrecoverable. The PUBG Ransomware can work without an Internet connection and, overall, can carry out an effective encryption ransomware attack by making the victim's files inaccessible and then demanding a ransom payment, which is the method used by most encryption ransomware Trojans active today. The following are some of the file types that are commonly targeted in ransomware attacks such as the PUBG Ransomware:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
The PUBG Ransomware also will remove the Shadow Volume copies of the targeted files and System Restore points, preventing computer users from accessing their files through alternative means.
The PUBG Ransomware's Lock Screen and Its Odd 'Ransom' Demand
The PUBG Ransomware will display a lock screen and a program window containing the following message:
'Your files is encrypted by the PUBG Ransomware!
but don't worry! it is not hard to unlock it
I don't want money!
Just play PUBG 1Hours!
or Restore code is [RANDOM CHARACTERS]
STATUS: [DETECTS IF THE GAME IS RUNNING]'
The PUBG Ransomware will start the decryption procedure after the victim loads the game on the affected computer. The lock screen also includes the decryption key, which can be entered into a text box with the name 'RESTORE CODE.' It seems that the PUBG Ransomware's creators intent is not to demand ransom payments or carry out random attacks but to force computer users to play this computer game.
Why Threats Like the PUBG Ransomware are not Harmless
Although on the surface it may seem that the PUBG Ransomware is nothing more than a harmless prank, you should take these threats very seriously. The PUBG Ransomware still has the capability of making the victim's files inaccessible, and the AES encryption is quite strong; the files encrypted using this encryption are not recoverable without the decryption key. Threats like the PUBG Ransomware are threatening because they can be easily adapted to more harmful means. For example, it would not take much for a con artist to adapt the PUBG Ransomware so that it demands a large ransom payment instead of asking the victim to play a computer game.
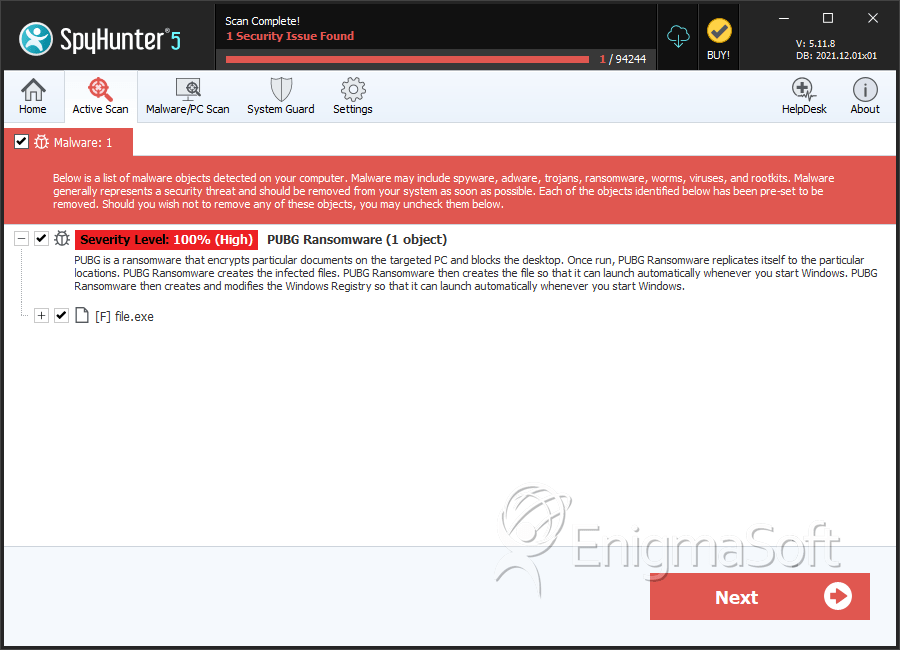
SpyHunter Detects & Remove PUBG Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 0997ba7292ddbac1c7e7ade6766ed53c | 0 |

