PsiXBot
The PsiXBot malware is a Trojan that surfaced in mid-2017 and received significant improvements in late-2018. The PsiXBot Trojan is a modular program written in the .NET programming language and distributed via the Spelevo Exploit Kit and the SmokeLoader Trojan actively. The PsiXBot Trojan is spread using a dropper that hides the true nature of the enclosed resources. That is why the samples of PsiXBot usually lack obfuscation. You should note that the PsiXBot malware is spread among users via fake invoices uploaded to legitimate file hosting platforms like Dropbox. Also, there are cases where already compromised machines were used to spread the threat to machines on the same local network.
PsiXBot is the name of a kit of malware tools that started out as a Trojan and grew in functionality over time. The first detections of the threat identified as PsiXBot were in 2017 but the malware is seeing more widespread use in 2019, as its capabilities grow.
The original incarnation of PsiXBot was a simple Trojan. However, in recent attacks that use PsiX, it has proven to be a lot more than that. In early 2019, security experts detected a campaign that used SmokeLoader - another piece of malware used to ferry extra malware to the systems it infects - to distribute PsiX, now a multi-module malware based on .NET code. The new version was able to not only steal credentials and data from the infected machines, but also download and execute files on them. A short while later, the Spelevo exploit kit was found distributing the same version of PsiX, which further piqued the interest of security researchers.
The main differences between the old and the new versions of PsiX are the addition of a large number of new commands enabled by new modules as well as AES encryption of strings. In most instances, PsiX is distributed using a dropper. Once executed, the first thing PsiX does is making sure it is the only running instance of itself. Then, the malware checks if the victim has its system language set to Russian. If that is the case, PsiX will terminate itself, which is a very decent hint for the origins of the malware.
The payload is deployed under %AppData%\Local\Microsoft\[filename].exe. Once installed, PsiX contacts its command and control (C&C) server that are represented by an array of .bit domains with humorous names such as "mygranny.bit". To successfully communicate with those, PsiX uses hardcoded DNS servers that vary per sample.
The bot scrapes a large number of system details including logged user name, present antivirus software, OS version, user permission level, installed hardware, hard drive space on the system disk and present .NET framework version. The exchange is encrypted with a hardcoded key contained in the malware sample itself.
Once this is done, PsiX sleeps for a minute and a half before requesting new commands from the server. The bot is able to dynamically call the C&C server and request the downloading of additional modules that provide extra layers of capabilities. Judging by the names of the available commands, the malware is able to execute code on the victim's system, log keystrokes, steal Outlook credentials and passwords.
You should be very attentive when you receive an email from what seems to be the GPay (pay.google.com) team claiming that your card was charged for using site services from Google. Since many users across the globe have an account at Google.com, the cybercriminals have decent chances to lure users into downloading the fake invoice and enabling the enclosed macro script. The embedded script downloads an encrypted shell and extracts its content into your system memory directly. Interestingly, one of the first checks performed by PsiXBot is to see if it is running on a machine with a default ru-RU (Russian) keyboard layout. If PsiXBot detects a Russian computer, it terminates and removes its files immediately. On the other hand, PsiXBot runs as intended on machines with different keyboard configurations initially. The PsiXBot Trojan reports the following system parameters to its 'Command and Control' servers:
- Active username and access privileges.
- Unique bot ID.
- Installed AV product.
- CPU model.
- GPU model.
- Available RAM.
- HDD/SSD serial number.
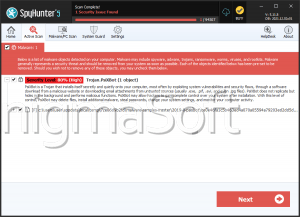
As mentioned above, the PsiXBot Trojan has a modular structure that allows its author to expand the PsiXBot functionality as needed with relative ease. The PsiXBot Trojan is centered around data exfiltration, but it can use a component called "BTCModule." The name is self-explanatory, and PsiXBot can be made to change the wallet addresses copied to the system clipboard whenever the user attempts to finish a digital coin transaction. That way the transaction form would include the wallet controlled by the PsiXBot team, not the intended recipient address. The PsiXBot covers data exfiltration needs by using a "BrowserModule" for exporting saved credentials in popular Web browsers; a "KeyLoggerModule" for recording the user's keyboard input; a "ComplexModule" (based on QuasarRAT)used to transmit files between the infected host and the control server; and a "SchedulerModule" designed to boot PsiXBot with Windows. Removing the PsiXBot Trojan manually is a challenge you might want to skip. Instead, you should use the services of a reputable anti-malware suite.
Detection names for PsiXBot used by AV companies are listed below:
A Variant Of MSIL/Agent.BFG
Malware (ai Score=98)
Riskware ( 0040eff71 )
TR/Dldr.Small.gnjzm
TROJ_GEN.R002C0DCS19
Trojan.Agent!UW7MmEwhgoQ
Trojan.Generic.D5E3CB6
Trojan.GenericKD.6175926
Trojan.Win32.Generic.4!c
Trojan.Win32.Mlw.euvrsl
W32/Generic!tr
Win32.Trojan.Generic.Pjnf
The main distribution and infection vectors used in spreading PsiXBot are two - spam campaigns with malicious attachments, as well as using paid services offered on the dark web that offer networks of previously infected systems that are rented out by cyber criminals. One example of such rented services is SmokeLoader, which distributes PsiX using the following link: hxxp://favoritfile.in/7-8.exe.
Intercepted spam emails distributing PsiX use a zip file containing JavaScript code that downloads the payload from another address: hxxp://img.martatovaglieri.it/index?83836