Princess Locker Ransomware
PC security analysts have come across a ransomware Trojan that has attracted their attention because of the amount of its ransom, as well as several quirks in its attack. Although most ransomware Trojans are very similar to each other, once in a while a ransomware Trojan like the 'Princess Locker' Ransomware will appear with a clear distinguishing characteristic. In the case of the 'Princess Locker' Ransomware, this Trojan demands the amount of 3 Bitcoin after encrypting the victim's files. This enormous amount, approximately $1800 USD at the current exchange rate, is more than three times the average rate that most ransomware Trojans demand. Even worse, the 'Princess Locker' Ransomware will double the amount to 6 BitCoin if the ransom is not paid within a certain time frame.
Table of Contents
The Princess that Anyone Wants to See
The 'Princess Locker' Ransomware encrypts the victim's files, taking them hostage. This is an approach that the 'Princess Locker' Ransomware has in common with most ransomware Trojans. The files encrypted by the 'Princess Locker' Ransomware can be identified because it adds a random extension to the encrypted files, as well as a unique ID that identifies the victim's computer. This information is relayed to the 'Princess Locker' Ransomware's Command and Control server. The 'Princess Locker' Ransomware drops ransom notes in the form of text and HTML files on the victim's computer. These files are named !_HOW_TO_RESTORE_[extension].TXT and !_HOW_TO_RESTORE_[extension].html, both also containing a unique ID number. The contents of these files include links to the TOR payment websites where victims can receive more information and make the 'Princess Locker' Ransomware's enormous ransom payment. The 'Princess Locker' Ransomware seems to be related to Cerber, a previously known ransomware Trojan. The attack is very similar and the payment website is simply a copy of the Cerber payment website, with a new logo. Like on the Cerber website, the victim has the option to change the language, with 12 possible languages. The website is accessed with the victim's ID number. When victims access the'Princess Locker' Ransomware payment site, the following message is displayed:
Your files are encrypted!
It means that your files have been transformed on a structural level and became inaccessible. In order to be able to access them again, you have to transform them back to the original state. This can be done only with the help of special software - «Princess Decryptor» which can be purchased only on this website. Each copy of «Princess Decryptor» works individually for each pair ID + Extension. Therefore, you have to purchase your own one as any other user whose files have also been encrypted. We accept only Bitcoin.
Further Details About the 'Princess Locker' Ransomware and Its Payment Site
The 'Princess Locker' Ransomware uses a standard payment site that is similar (and probably recycled from Cerber) to most ransomware payment sites. The 'Princess Locker' Ransomware includes its language selection screen and the interface that allows victims to pay the 'Princess Locker' Ransomware ransom. The 'Princess Locker' Ransomware payment site allows victims to decrypt a single file. It is possible, due to the low-dissemination numbers associated with the 'Princess Locker' Ransomware, that this ransomware Trojan is still under development. It is likely that the 'Princess Locker' Ransomware payment site will later include an option to contact the con artists directly, such as a chat window or an email address.
Dealing with the 'Princess Locker' Ransomware
You may not be capable of decrypting the files that have been compromised by the 'Princess Locker' Ransomware currently. Because of this, the best way to deal with the 'Princess Locker' Ransomware is to prevent its attacks by being protected properly. The recommended way to become invulnerable to the 'Princess Locker' Ransomware is to ensure that all files are backed up properly. If computer users can recover their files by restoring it from a backup, then the con artists responsible for the 'Princess Locker' Ransomware no longer have leverage for their ransom demands.
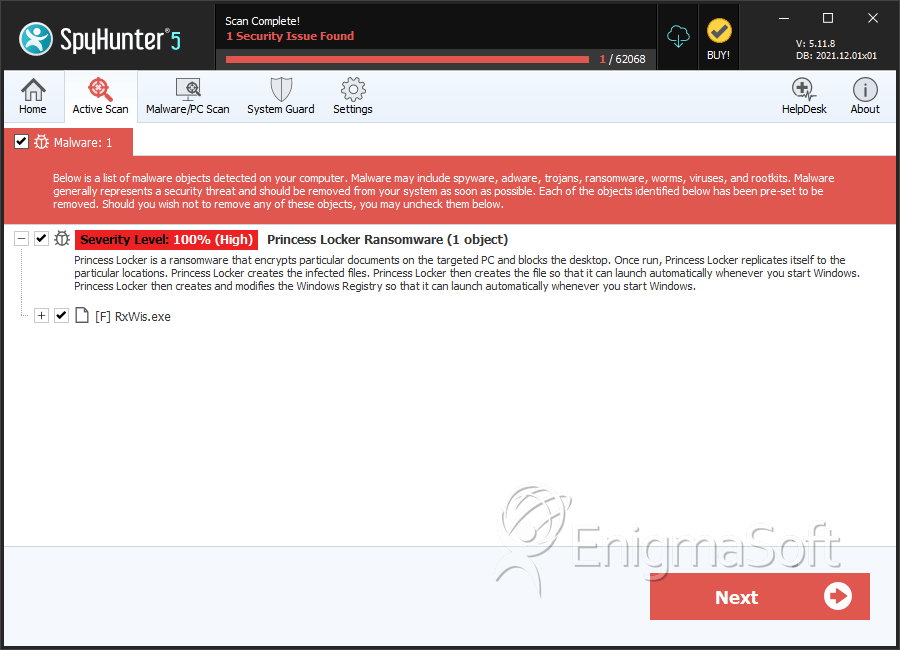
SpyHunter Detects & Remove Princess Locker Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | RxWis.exe | 14c32fd132942a0f3cc579adbd8a51ed | 0 |


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.