Phorpiex
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
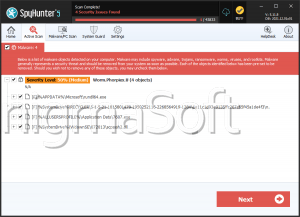
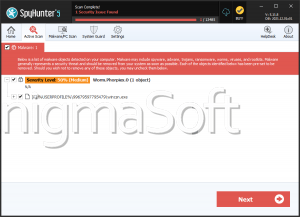
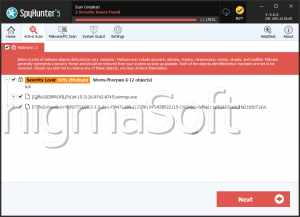
| Ranking: | 16,382 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 92 |
| First Seen: | April 11, 2012 |
| Last Seen: | June 27, 2023 |
| OS(es) Affected: | Windows |
Phorpiex is a group of worms that affects computers running the Windows operating system. These worms have been around for several years and present a severe threat to an infected computer. Keep your anti-malware solution always updated with the latest virus definitions in order to protect your computer from variants in the Phorpiex family. Phorpiex worms tend to spread using removable memory devices and Autorun exploits, a common tactic of many worms. Phorpiex variants are also designed to use the Windows Live Messenger and other instant messaging applications in order to spread from one computer to another. The main payload for most Phorpiex variants is creating a backdoor into the infected computer which then allows criminals to control the infected computer from a remote location.
This Week In Malware Ep16 Pt2: Phorpiex Botnet Spreading Ransomware via MalSpam Campaigns
Phorpiex was documented by cybersecurity researchers for the first time in February 2016, although this threat exists for much longer on the malware market. Often referred to as an "IRC worm," in 2016 Phorpiex spread over live chat in Windows Messenger and Skype, as well as through USB storage drives. In the following years, new versions of the malware started infecting machines through spam email campaigns and weakly protected RDPs, but the overall architecture and functions of the worm remained the same. Currently, Phorpiex, also known as Trik botnet (not to be confused with TrickBot banking Trojan, which is a different threat), is known for dropping a broad range of malicious payloads on target computers, including some of the most dreadful ransomware threats and cryptocurrency miners.
Worms like Phorpiex are designed to hide themselves, not alerting their victims of the presence of the infection. In this way, Phorpiex can operate in the background to allow criminals to take over the infected computer and use it from their own devices. It is possible to detect the presence of Phorpiex by being aware of common system changes associated with Phorpiex and other worms. For example, as with other worms that exploit the Autorun functionality in removable memory devices, it is possible to determine that a removable memory device carries the Phorpiex infection because it will suddenly contain hidden files and folder icons that are actually cleverly disguised shortcuts that lead to the Phorpiex's executable files. Some files associated with Phorpiex include executable files with names such as windsrcn.exe, winmgr.exe, winsam.exe and winsrvc.exe. The Phorpiex worm and its variants will also change the infected computer system's registry to ensure that this file runs automatically upon start-up, disguising the malicious registry edit as a 'Microsoft Windows Update'.
Phorpiex is a serious cyber-security threat as it can send tremendous volumes and pack an infection chain that is rarely observed by researchers and can only be compared to some of the biggest documented Emotet attacks. The worm has now been caught in over 1.4 million malicious email messages in 2019 alone, with the biggest part of this campaign launching since the beginning of April 2019.
Table of Contents
Phorpiex/Trik Botnet Has a Simple Structure
Some of the first described samples of Phorpiex revealed that this worm is not particularly sophisticated and could be reverse-engineered easily. In 2016, it had a simple technique to evade virtual machines, and that seemed to be its only anti-detection feature. The anti-VM code has been removed from most of the samples analyzed in 2018 and 2019, yet some samples retained it. Some samples modify the Windows registry in order to disable anti-virus and firewall protection, while affected registry values include: UpdatesOverride, AntiVirusOverride, AntiVirusDisableNotify, FirewallOverride, FirewallDisableNotify, and AutoUpdateDisableNotify. Phorpiex/Trik does not hide itself very well, and its malicious files can be easily recognized on the hard disk as they are not obfuscated.
Phorpiex/Trik botnet operators mainly instruct it to do three things:
- Download and run other malware threats on target computers
- Acquire unauthorized access through poorly protected protocols by checking popular login/password combinations on a list of servers
- Spread malicious executables by email
Phorpiex/Trik Botnet Is Known for Deploying GandCrab Ransomware
Since 2018, a new variant of Phorpiex/Trik botnet pops up and, according to researchers, the infamous GandCrab ransomware is at the heart of these recent campaigns. Now, the malware focuses on targeting corporate networks that operate server-side remote access applications without adequately protecting their protocols. Therefore, a typical victim would be a large organization that offers remote-work options to their employees.
To initiate an attack, Trik would scan the web for Remote Desktop Protocols (RDPs) and Virtual Network Computing (VPN) endpoints via port 5900. Then, it would launch brute-force attacks against random picks, testing a list of popular username and password combinations until it penetrates endpoints where such weak credentials have been implemented, and the protocols have not been adequately protected. Trik botnet would then use these compromised endpoints as a means to infect the entire corporate network with malware.
Phorpiex Worm Can Sneak Through Malicious Zip-File Attachments
Some of the recently analyzed samples also spread through phishing emails with attached zip files. Once an unsuspecting user launches the javascript file that is inside the zip, the Phorpiex worm loads, followed by GandCrab ransomware, Ursnif ISFB (Gozi) banking Trojan, and a cryptocurrency miner known as CryptoNight XMRig. The obfuscated javascript in the zip file launches the Windows script host (wscript.exe) to leverage powershell, and it downloads an executable named "good.exe" from a server located in the Russian Federation.
The good news for users is that Phorpiex/Trik spam emails are easy to recognize as they follow the same pattern each time. The addresses from which they are sent have the same structure: bogus names followed by two numbers@ four random numbers.com, for example, "Bonita Rogers
The most common source of a Phorpiex infection involves connecting an infected removable drive to your computer. To ensure that its files are open, Phorpiex sets the infected drive's folders to hidden and then creates fake folder icons with the same names. These folder icons are actually shortcuts to Phorpiex's executable file. The other most common way Phorpiex spreads is by convincing victims to click on links distributed in malicious instant messages that are sent automatically from infected computers. ESG security researchers have observed variants of malicious instant messages in multiple languages, all containing a variant of Phorpiex.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.