Phenol Ransomware
The rapid rise of sophisticated ransomware highlights the critical importance of practicing strong cybersecurity hygiene. Malware families like Phenol Ransomware are designed not just to disrupt operations but also to extort victims through data theft and financial blackmail. Protecting devices, data, and networks from such threats requires vigilance and proactive security measures.
Table of Contents
Inside the Phenol Ransomware Attack
Phenol belongs to the notorious ransomware category, which encrypts files and demands ransom for their release. Once it infiltrates a system, the malware encrypts a wide range of files and alters their names by appending both the attacker's email and the '.phenol' extension. For instance, 1.jpg transforms into '1.jpg.[Hulk67888@outlook.com].phenol.'
Following encryption, victims discover a ransom note titled Encrypt.html. This message informs them that both encryption and data theft have occurred. Victims are ordered to reach out to the attackers within 24 hours and to pay a ransom of $5000 in Tether (USDT) within 72 hours. Failure to comply, the criminals claim, will result in stolen data being leaked publicly.
The ransom note also discourages victims from attempting manual recovery or halting malicious processes, threatening permanent data loss if such actions are attempted.
The Ransom Payment Trap
Cybercriminals behind ransomware frequently emphasize payment as the only recovery method. However, paying the ransom carries significant risks:
- There is no guarantee that attackers will provide a working decryption key.
- Payment directly supports and funds further criminal activity.
- Victims may be targeted again, as paying once signals willingness to comply.
Security experts therefore strongly advise against ransom payments. Instead, victims should focus on isolating infected systems, reporting the attack, and restoring files from clean backups whenever possible.
Infection Pathways and Distribution Methods
Phenol Ransomware, like many modern threats, relies on diverse distribution strategies. It commonly spreads via:
- Phishing campaigns and social engineering tactics, where malicious attachments or links masquerade as legitimate communications.
- Trojan loaders and backdoors that silently deliver payloads.
- Untrustworthy download sources, including free file-hosting services, torrents, and cracked software sites.
- Malicious scripts, fake software updates, and malvertising designed to trigger stealthy downloads.
Additionally, Phenol and similar malware can sometimes propagate across local networks or spread through removable devices such as USB drives, expanding the impact without user interaction.
Strengthening Your Defenses Against Malware
Preventing ransomware infections requires more than just antivirus software. Users and organizations must implement layered security practices to reduce risk exposure. Some of the most effective strategies include:
Regular Backups – Maintain multiple secure backups (offline and cloud-based) to ensure critical data can be restored without paying a ransom.
Patch and Update – Keep operating systems, software, and applications up to date to close vulnerabilities often exploited by attackers.
Email Awareness – Treat unexpected emails, attachments, and links with suspicion. Verify the sender before interacting with content.
Strong Access Controls – Use multi-factor authentication (MFA), unique passwords, and limit user privileges to reduce attack surfaces.
Network Segmentation – Divide networks into smaller zones to limit the lateral spread of malware.
Disable Macros and Scripts by Default – Prevent malicious code from executing automatically within documents.
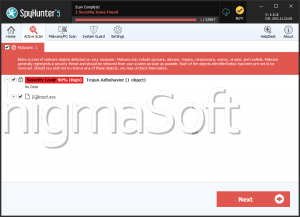
Endpoint Protection Tools – Deploy reputable security solutions capable of detecting and blocking ransomware behaviors.
Final Thoughts
Phenol Ransomware is a stark reminder of the destructive and financially motivated nature of today's cybercrime. While recovering encrypted files without backups is nearly impossible, prevention and preparation remain powerful defenses. By maintaining strong security practices, staying alert to social engineering, and safeguarding critical data through backups, individuals and organizations can significantly reduce their exposure to ransomware threats like Phenol.