Norman
There are many different strains of crypto-miners out there in the wild world of the Internet. Different crypto-miners target different crypto-currencies, but it appears that the most popular one among them is the Monero crypto-currency. Recently, malware experts have been able to spot a brand-new crypto-miner lurking on the Web by luring it with a honeypot. Most crypto-currency miners are similar to one another fairly, but today's case is a little different.
Attacks in Three Stages
This new crypto-miner was named Norman as it appears that there are quite a few of its files carrying this name. The Norman crypto-miner is a master of disguise and is capable of avoiding detection very efficiently. This impressive crypto-mining tool carries out its attack in three steps. These stages can be somewhat flexible depending on the environment in which the Norman miner is operating. To avoid raising suspicion, the Norman crypto-miner is capable of following the activity of the victim and would halt action if the user performs certain tasks. The three stages of the attack are as follows
- Executing the Norman miner - The executable files used by the miner are packed to look like a legitimate Windows installer. This might mean that the authors are either using social engineering tricks to get the users to install the harmful software unknowingly, or they rely on manual deployment. The installers are programmed to drop the files under a certain order.
- Injecting the Norman miner – The Norman crypto-miner will use different directories in which to drop its payload depending on the OS of the host some of which can be the 'notepad.exe,' 'explorer.exe,' 'svchost.exe' and 'wuapp.exe.'
- Mining cryptocurrency – The miner relies on a modified variant of XMRig, an open-source miner and mines Monero crypto-currency. In case the user launches the Task Manager, it will cease activity to avoid being detected by the victim. Once this service is closed, the Norman miner will continue its operation.
Computers Infected by Norman also Were Backdoored with a PHP Shell
Computers infected by the Norman miner also seemed to have a backdoor shell deployed on them - the threat actor is likely to be responsible for both, and the purpose of the PHP-based shell is to allow them to execute additional tasks on the compromised computer. This means that the operators of the Norman miner may be intending to infect the hosts with additional malware, or they have taken advantage of a vulnerability to load the Norman crypto-miner on the compromised system.
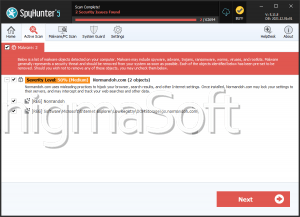
It is crucial to have a legitimate anti-malware application on your system that will protect you from nasty pests like the Norman miner.