Neon Ransomware
Cybersecurity researchers have recently discovered a new ransomware threat called NeonL. Similar to other malware of its kind, Neon operates by encrypting files on the victim's computer once it infiltrates the system. The ransomware alters the original filenames by appending the '.neon' extension to them. For instance, a file named '1.pdf' would be transformed into '1.pdf.neon,' while '2.doc' would become '2.doc.neon,' and so on. Additionally, Neon generates a ransom note in the form of a text file named '_readme.txt' on the compromised device.
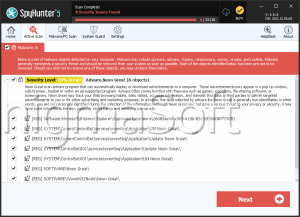
It is worth noting that Neon Ransomware belongs to the STOP/Djvu family of ransomware, which suggests the possibility of other threatening software being present on the affected devices. In fact, operators known for distributing STOP/Djvu variants have also been observed deploying information stealers like RedLine and Vidar on compromised systems.
The Neon Ransomware Extorts Its Victims for Money
Upon examining the ransom note left by the criminals, it becomes evident that individuals who wish to regain control over their encrypted files are compelled to make payment for a decryption program and a unique key. The note specifies that victims have a limited timeframe to avail themselves of a discounted rate of $490 by contacting the attackers via email within 72 hours. However, failure to comply within this period would result in the full payment amount of $980.
The ransom note provides two email addresses as means of communication with the attackers: 'support@freshmail.top' and 'datarestorehelp@airmail.cc.' Victims are strongly advised to utilize these email addresses to establish contact with the perpetrators and make necessary arrangements for the payment and subsequent decryption process.
It is crucial to acknowledge that attempting to restore the encrypted files without the decryption tools provided by the attackers is an uncommon occurrence. Therefore, it is not recommended to succumb to the ransom demands, as there is no guarantee that the attackers will indeed furnish the decryption tools even after the ransom has been paid.
Establish Sufficient Defensive Measures to Protect Your Devices and Data from Ransomware Threats
To safeguard their data from ransomware threats, users can implement a comprehensive set of security measures. These measures involve adopting a proactive approach to enhance their overall cybersecurity posture. Firstly, it is crucial to maintain up-to-date antivirus and anti-malware software on all devices. Regularly updating these security solutions ensures protection against known ransomware variants and other threatening software.
In addition, exercising caution when browsing the internet and avoiding suspicious websites or clicking on unknown links and attachments can help prevent the inadvertent downloading of ransomware. It is essential to be vigilant about phishing emails and refrain from opening attachments or providing sensitive information in response to unsolicited requests.
Regularly backing up significant data to offline or Cloud storage is a crucial step in mitigating the impact of a ransomware attack. By creating backups, users can restore their files without having to pay a ransom. However, the backups must be stored securely and separate from the primary network to prevent their compromise during an attack.
Implementing strong and unique passwords for all accounts, along with enabling two-factor authentication whenever possible, adds an extra coating of security to prevent unauthorized access to sensitive data. Regularly updating and patching operating systems and applications also is essential to address vulnerabilities that attackers may exploit.
Educating oneself about the latest ransomware trends, techniques, and prevention strategies is key to staying informed and implementing effective security measures. Users should stay abreast of security best practices and consider seeking professional advice when it comes to securing their digital environments.
By adopting a multi-layered security approach, staying informed, and being proactive, users can significantly reduce the risk of falling victim to ransomware attacks and protect their valuable data from being encrypted and held hostage.
The ransom note Neon Ransomware leaves to its victims is:
'ATTENTION!
Don't worry, you can return all your files!
All your files like pictures, databases, documents and other important
are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-3q8YguI9qh
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that's price for you is $490.
Please note that you'll never restore your data without payment.
Check your e-mail "Spam" or "Junk" folder if you don't get answer more than 6 hours.To get this software you need write on our e-mail:
support@freshmail.topReserve e-mail address to contact us:
datarestorehelp@airmail.ccYour personal ID:'