Mystic Ransomware
The Mystic Ransomware is an encryption ransomware Trojan that was first observed on September 14, 2017. The Mystic Ransomware is designed to encrypt the victim's files to demand a ransom payment in exchange for the decryption key. This is a typical attack method used by these threats. The Mystic Ransomware will use the AES encryption to make the victim's files inaccessible, taking them hostage. The Mystic Ransomware will change the victim's desktop image to display a ransom note, asking for a large payment to get the decryption key and software after encrypting the victim's files. The Mystic Ransomware uses an encryption method very strong so that the files encrypted by the Mystic Ransomware cannot be restored without access to the decryption key or software. Because of this, taking precautions against the Mystic Ransomware and the numerous other encryption ransomware Trojans that are active today, you can prevent countless problems.
The not so Mystic Actions of the Mystic Ransomware Trojan
The Mystic Ransomware may be delivered through corrupted spam email attachments, which is its most favored distribution method. The con artists also may deliver the Mystic Ransomware by taking advantage of vulnerabilities in the victim's software. Malware researchers consider the Mystic Ransomware a severe threat to the victims' data and computers. The Mystic Ransomware will target various file types in its attack, typically looking for the user-generated files, which may include movies, music, eBooks, and other commonly used file types. The Mystic Ransomware, unlike other ransomware Trojans, does not rename or alter the files' extensions during encryption. An example of the file types that may be targeted by attacks like the Mystic Ransomware is:
.3gp, .7z, .apk, .avi, .bmp, .cdr, .cer, .chm, .conf, .css, .csv, .dat, .db, .dbf, .djvu, .dbx, .docm, ,doc, .epub, .docx .fb2, .flv, .gif, .gz, .iso .ibooks, .jpeg, .jpg, .key, .mdb .md2, .mdf, .mht, .mobi .mhtm, .mkv, .mov, .mp3, .mp4, .mpg, .mpeg, .pict, .pdf, .pps, .pkg, .png, .ppt .pptx, .ppsx, .psd, .rar, .rtf, .scr, .swf, .sav, .tiff, .tif, .tbl, .torrent, .txt, .vsd, .wmv, .xls, .xlsx, .xps, .xml, .ckp, .zip, .java, .py, .asm, .c, .cpp, .cs, .js, .php, .dacpac, .rbw, .rb, .mrg, .dcx, .db3, .sql, .sqlite3, .sqlite, .sqlitedb, .psd, .psp, .pdb, .dxf, .dwg, .drw, .casb, .ccp, .cal, .cmx, .cr2.
The Mystic Ransomware delivers a ransom note in its attack. The Mystic Ransomware ransom note is contained in a text file named 'ransom.txt' that is dropped on the infected computer's desktop. The full text of the Mystic Ransomware's ransom note reads:
'Your computer has been hacked and your files have been locked.
You have 5 days left to recover your files so quickly follow recovery process below.
Recovery Process in 3 easy steps (Automated System. No human intervention. Works 24/365):
1) Buy 1.01 BitCoin Approx 280$. (Easiest buying option is www(.)localbitcoins.com) and goto the following website:
[TOR-based site]
2) Send payment of 1.01 Bitcoin to the address in the website given above.
3) In approx 15 minutes after making the payment to the bitcoin address, Go back to the above website. If payment is successful then you will receive unlock instructions.
Don't delete or modify this ransom file till recovery of files as no recovery is possible without this file. This file is on your desktop for future use.
List of files which have been locked are given below.
— MYSTIC'
Dealing with the Mystic Ransomware
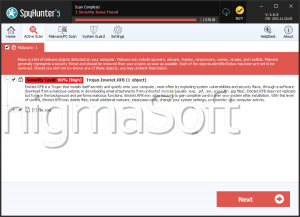
It is clear that the Mystic Ransomware is somewhat outdated since 1 BTC hasn't been worth 280 USD for nearly two years. The exchange rate for 1 BTC is over 3000 USD currently! This may give some clue to the origins of the Mystic Ransomware's code since it is common for on artists to recycle code and text strings from one ransomware threat to another. Computer users should refrain from paying the Mystic Ransomware ransom and instead take precautions to ensure that all data is properly backed up in case of an attack.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.