MRAT
MRAT is a malware threat that first caught the attention of the infosec community back in 2014. At the time, MRAT was being deployed in an attack targeting protestors in Hong Kong. The purpose of this threatening tool is to carry out reconnaissance and data-harvesting activities on the compromised devices. It boasts an impressive toolkit of spyware functionalities. MRAT can delete applications and files on the infected device, download additional applications, collect browsing data, access text messages, contacts, call logs, harvest email account credentials, search external storages for files with a specific MD5 hash, execute arbitrary commands, record audio, and exfiltrate all gathered information to its Command-and-Control server. MRAT also is equipped with anti-detection techniques and it performs checks for specific anti-malware solutions.
The threat was used as a late-stage payload in a recent attack against Android users. The cybercriminals managed to sneak multiple weaponized applications to the official Google Play store thanks to a previously unknown malware dropper named Clast82. Each of the applications was built by taking a legitimate open-source Android application and injecting it with the Clast82 code. The nine identified applications carrying the malware are:
- BeatPlayer,
- Cake VPN,
- eVPN (two different versions),
- Music Player,
- Pacific VPN,
- QR/Barcode Scanner MAX,
- QRecorder,
- Tooltipnattorlibrary.
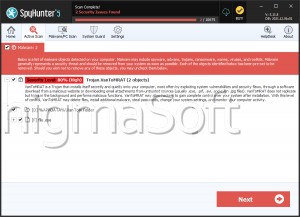
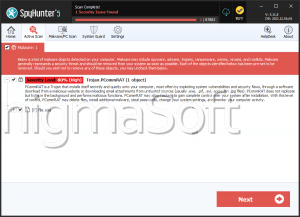
After Google was made aware of the breach, all of the threatening applications were taken down from the Play store. Users who have downloaded and installed any of them previously are still at risk. Use a professional anti-malware solution to scan your Android device and clean it from any potential malware threats.