Moba Ransomware
Moba Ransomware Image
PC experts have spotted a new data-encrypting Trojan preying on unsuspecting users online. The name of this newly uncovered file-locker is Moba Ransomware. This new Trojan belongs to the notorious STOP Ransomware family. This is one of the most active ransomware families worldwide.
Propagation and Encryption
When the Moba Ransomware compromises your computer, it will scan your data and begin encrypting your files. This file-locker is likely targeting a wide variety of filetypes such as .doc, .docx, .pdf, .txt, .png, .jpg, .jpeg, .svg, .png, .gif, .mp3, .midi, .mid, .wav, .webm, .mp4, .mov, .xls, .xlsx, .srt, .db, .rar, .zip and others. When the Moba Ransomware encrypts a file, it makes sure to alter its filename. This data-lockers appends a ‘.moba’ extension to the locked files names. This means that a file called ‘blue-blur.png’ will be renamed to ‘blue-blur.png.moba.’ This ransomware threat may be propagated via spam emails, bogus social media profiles, torrent trackers, malvertising, fake software updates, and other commonly utilized distribution techniques.
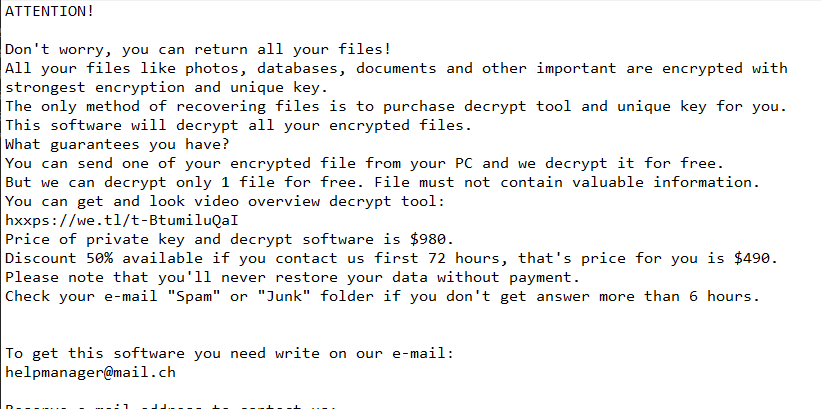
The Ransom Note
Next, the Moba Ransomware drops a ransom note named '_readme.txt' on the victim's desktop. In the ransom message, the Moba Ransomware creators state that they demand to be paid $490 as a ransom fee. Users who do not process the payment within three days will have to pay double the price - $980. The victim is required to contact the attackers via email – ‘helpmanager@mail.ch' and ‘restoremanager@firemail.cc.' The attackers are willing to decrypt one or two files for free as long as they do not contain important data.
You should avoid communicating with cybercriminals. There is no valid point in paying them because there is no guarantee that the decryption key you need will be sent to you. Make sure you remove the Moba Ransomware from your PC via a legitimate, up-to-date anti-malware solution.

