Messages in Soundbox Email Scam
Cybersecurity experts have analyzed the 'Messages in Soundbox' emails and determined them to be deceptive messages intended to deceive recipients. The aim of these ill-minded actors is to compromise victims' computers by distributing malware. The emails include a harmful attachment that serves as a vehicle for malware dissemination. These messages are camouflaged to appear as notifications related to messages in Soundbox, a tactic employed to lure unsuspecting users into opening the attachments, ultimately leading to malware infection.
Falling for the Messages in Soundbox Email Scam may Have Severe Consequences
The emails purportedly originate from a 'Soundbox' service and claim that there are three undelivered messages awaiting the recipient in their Soundbox. According to the email, this issue is attributed to a mail server system error. Recipients are instructed to verify their email address to release these supposed Soundbox messages into their inbox.
Additionally, the emails warn that failure to release these messages will result in the deactivation of the recipient's account and permanent deletion of their email data. These fraudulent emails employ urgent language to coerce recipients into opening either an attached MS Excel document or a file downloaded via a provided link.
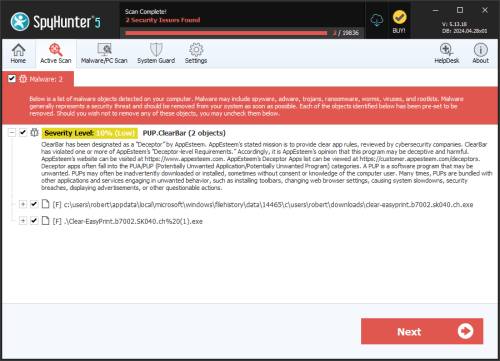
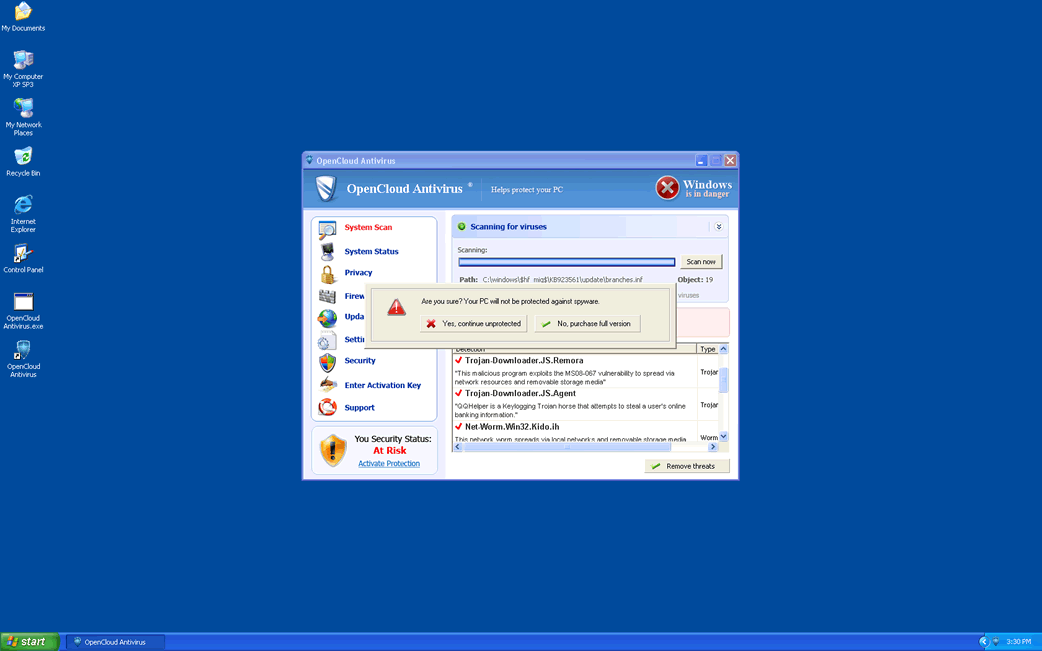
The attached file in these emails is confirmed to be fraudulent, although the specific type of malware it contains is currently unidentified. It could potentially be ransomware, which encrypts files on the victim's computer and demands a ransom for decryption. Alternatively, it might be another form of malware, such as a banking Trojan or keystroke logger, designed to collect sensitive information.
Furthermore, cybercriminals may exploit the distributed file to entice users into unwittingly installing a cryptocurrency miner on their systems. This malware type utilizes computer resources to mine cryptocurrency, leading to reduced system performance, increased electricity consumption, and other associated issues.
In any scenario, engaging with the file or link provided in these emails could have severe repercussions, including financial losses, compromise of personal information, identity theft, data encryption and other significant harms. Therefore, users are strongly advised against opening any links or files presented in emails of this nature. It's necessary to remain vigilant and exercise caution when interacting with unexpected or suspicious email communications.
Red Flags Indicating a Tactic or Fraudulent Email Message
Identifying red flags in email messages can help individuals recognize potential tactics or unsafe content. Here are typical indicators to watch out for:
- Unsolicited Emails: Be careful with emails from unknown senders, especially if they contain unexpected attachments or links.
- Urgency or Threats: Fraudulent emails often provoke a sense of urgency alarm to prompt immediate action. For example, threats of account closure or legal consequences if action is not taken quickly.
- Generic Salutations : Emails that start with standardlike 'Dear Customer' instead of addressing you by name may be suspicious.
- Unusual Sender Addresses: Check the sender's email address carefully. Fraudsters may use addresses that look similar to legitimate ones but have slight variations.
- Spelling and Grammar Errors: Legitimate organizations typically maintain professional communication standards. Poor spelling or grammar in emails could be a sign of a tactic.
- Demands for Private Details: Be wary of emails requesting private information such as passwords, credit card details or social security numbers. Legitimate organizations usually don't ask for this via email.
- Unsolicited Attachments or Links: Avoid opening attachments or accessing links in emails from unknown sources. These can lead to malware installation or phishing sites.
- Mismatched URLs: Move the mouse over links (without clicking) to see the actual URL destination. Fraudsters often use deceptive links that look legitimate but lead to unsafe websites.
- Unexpected Requests for Money: Be cautious of emails asking for money transfers or payments for unexpected services or products.
- Too Good to Be True Offers: Emails promising large sums of money, lottery winnings, or gifts are often phishing attempts or tactics.
- Impersonation of Known Brands: Watch for emails that impersonate well-known companies or institutions. Verify the sender's identity by contacting the organization directly using official contact details.
- Unusual Email Content: Be cautious of emails containing irrelevant content or topics unrelated to your usual interactions with the sender.
By staying vigilant and recognizing these red flags, individuals can better protect themselves against email-based tactics and harmful activities. When in doubt, verify the authenticity of the email by contacting the sender through official channels or by using trusted contact information.