Matrix (Proton) Ransomware
Ransomware remains one of the most disruptive threats facing everyday users and organizations alike. A single misstep, opening a booby-trapped attachment or installing a tainted tool, may result in encrypted files, stolen data, operational downtime, and extortion demands. Building strong, layered defenses before an incident occurs is the most reliable way to protect your devices and your data.
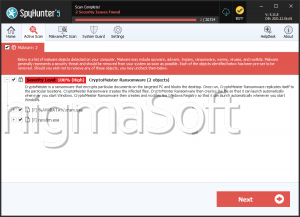
Threat Overview: Meet 'Matrix' from the Proton Lineage
Matrix is a ransomware strain associated with the Proton family and has been analyzed by security researchers for its aggressive file-locking and extortion tactics. After breaching a system, Matrix encrypts user data and systematically renames each item using a random string, then appends the '.matrix' extension. For example, '1.jpg' might become '8LdggFR8PH.matrix,' while '2.pdf' could be renamed to 'pDFcd9bTfH.matrix.' This combination of strong cryptography and filename randomization makes manual recovery infeasible.
Ransom Demand and On-Screen Pressure
Once encryption completes, Matrix alters the desktop wallpaper to amplify urgency and plants a ransom note named 'HowToRecover.txt.' The note claims the victim's files have been both encrypted and exfiltrated, and directs the victim to reach out via a TOR portal or email address at 'shadowmatrix@onionmail.org'. It also attempts to dissuade victims from using recovery services or third-party tools, warning of permanent data loss—language designed to isolate the victim and steer them toward payment.
What You Can—and Cannot—Recover
Files locked by Matrix are not realistically recoverable without the attackers' private keys. Free restoration is only possible if a legitimate third-party decryptor exists for this exact variant or if clean, recent backups are available. Paying the ransom is strongly discouraged: there is no enforceable guarantee the criminals will provide working decryption, will stop extorting you, or will delete stolen data. The most reliable path to restoration is isolating the affected system, eradicating the malware, and restoring from trusted backups.
Persistence and Lateral Risk
Leaving Matrix active on a system invites repeat encryption events, further tampering, and potential spread across the local network or to connected storage. Immediate containment, disconnecting the device from networks and external drives, reduces the chance of additional data loss or cross-device impact.
How Matrix Reaches Victims
Matrix leverages the same broad attack surface that fuels most ransomware incidents. Malicious email attachments and links are common entry points, as are cracked or pirated software packages, key generators, and other 'free' tools seeded with malware. Exploited software vulnerabilities, fake tech-support lures, and drive-by downloads via compromised or rogue websites are also routine. Threat actors additionally abuse malicious ads, untrusted third-party downloaders, P2P networks, and infected removable media. In practice, the final payload is often delivered through executables, archives (ZIP/RAR), PDF or Office documents with embedded macros or scripts, and various script files.
Closing Thoughts
Matrix (Proton) Ransomware blends strong encryption, file renaming, visual intimidation, and data-theft claims to coerce payment. The right combination of user vigilance, technical controls, rigorous patching, and resilient backups turns this from a catastrophe into a recoverable event. Treat every unexpected attachment, download, or 'free' tool as a potential trap, and make tested backups and timely patching non-negotiable parts of your security routine.