CryptoMeister Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 11 |
| First Seen: | May 5, 2017 |
| Last Seen: | October 24, 2025 |
| OS(es) Affected: | Windows |
The CryptoMeister Ransomware is a ransomware Trojan that seems to be targeted to French speakers. The CryptoMeister Ransomware carries out a typical ransomware attack, encrypting the victims' files and then asking for a ransom to come up with the decryption key needed to recover the affected files. Threats like the CryptoMeister Ransomware take the victims' files hostage and then demand the payment of a ransom. PC security experts strongly counsel affected users to refrain from paying the CryptoMeister Ransomware ransom, because there is no assurance that the people responsible for this threat will keep their word and deliver the decryption key. Furthermore, paying the CryptoMeister Ransomware ransom allows con artists to continue developing and releasing threats like the CryptoMeister Ransomware.
Table of Contents
The CryptoMeister Ransomware – A Meister of Extortion
The CryptoMeister Ransomware can be delivered in a variety of ways. The most probable way in which the CryptoMeister Ransomware is being delivered to the victims' computers is by using corrupted email attachments that download and install the CryptoMeister Ransomware onto the victim's machine. Once the CryptoMeister Ransomware enters a computer, it will use a combination of the AES and RSA encryptions to force the victim's files to be inaccessible. The CryptoMeister Ransomware will target user generated files, which may include PDFs, text files, audio and video files, images, and files generated by software such as Microsoft Office, Libre Office, Adobe Photoshop, etc. The CryptoMeister Ransomware demands the payment of 0.1 BitCoin, approximate $150 USD at the current exchange rate.
How the CryptoMeister Ransomware may Extort Its Victims
After encrypting the victim's files, the CryptoMeister Ransomware will deliver its ransom note. Below is the original text in French, as well as an English translation of the CryptoMeister Ransomware's ransom demands:
'Vérrouillé
Votre ordinateur à été verrouillé
Tous vos fichiers ont été cryptés. Pour récupérer l'accès à votre PC, vous devez envoyer 0.1 bitcoin à l'adresse ci-dessous
loading
Etape 1 : Allez sur xxxxs://wvw.coinbase.com/siqnup
Etape 2: Créez un compte et suivez les instructions
Etape 3 : Allez dans la section "Acheter des bitcoins" puis achetez bitcoin
Etape 4: Allez dans la partie "Envoyer", entrez l'adresse indiquée ci dessus et le montant (0.1 bitcoin)
Etape 5: Cliquez sur le bouton ci-dessous des que dest fait, vos fichiers seront décryptés et le virus disparaitra
'Vérifier'
Si vous tentez de contourner le verrouillage, tous les fichiers seront publiés sur internet ainsi que vos identifiants pour tous les sites.'
'Locked
Your computer has been locked
All your files are encrypted. To gain access to your PC, you need to send to 0,1 Bitcoin address below
loading
Step 1: Go to the xxxxs: //wvw.coinbase.com/siqnup
Step 2: Create an account and follow the instructions
Step 3: Go to the section "Buy Bitcoins", and then buy Bitcoin
Step 4: Go to the section "Send", enter the email address above and the sum of (0,1 Bitcoin)
Step 5: click the button below to verify that the payment, your files will be decrypted and the virus disappear
'Test'
If you try to bypass the lock, all the files will be published on the Internet, as well as your login for all sites.'
It is not advised to follow the instructions in the CryptoMeister Ransomware's ransom note, especially since there is nothing that can guarantee that the people responsible for the CryptoMeister Ransomware will keep their promise and provide the decryption key.
Preventing the CryptoMeister Ransomware Attacks
Unfortunately, the files encrypted by the CryptoMeister Ransomware are not recoverable with current technology. Because of this, take preventive measures to ensure that your data is safe from attacks like the CryptoMeister Ransomware, which are becoming common increasingly. The best protection against threats like the CryptoMeister Ransomware is to have file backups. This allows computer users to recover their data from the backup copy without needing to pay the ransom, which removes any leverage the con artists gain over the victim during the attack. Besides having file backups, PC security researchers advise computer users to have a strong anti-malware program that is fully up-to-date.
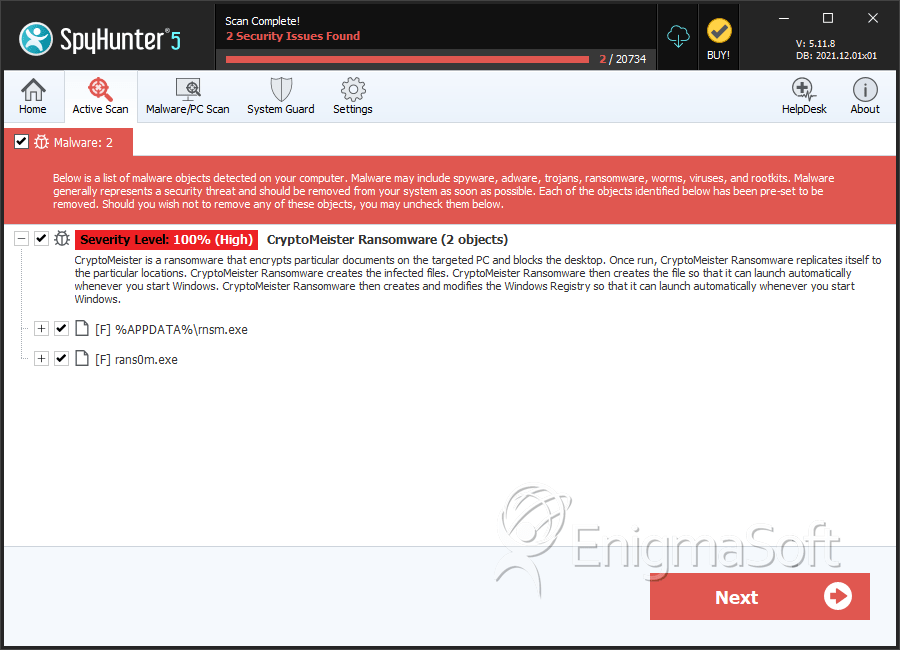
SpyHunter Detects & Remove CryptoMeister Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | rnsm.exe | 85217894ac89103e2ea0d9cf4657c2af | 5 |
| 2. | rans0m.exe | 629feff5503090f01e737c0567811814 | 1 |
