Lockis Ransomware
Modern malware has become increasingly aggressive, stealthy, and financially motivated. Ransomware, in particular, poses a severe threat by locking users out of their own data and applying intense psychological pressure to force payment. Protecting devices against such threats is essential not only to safeguard personal files but also to prevent data leaks, financial losses, and the spread of infections across connected systems.
Table of Contents
Lockis Ransomware at a Glance
Lockis Ransomware is a file-encrypting malware strain linked to the GlobeImposter ransomware family, a group known for producing numerous variants with similar behavior but different identifiers. Security analysts uncovered Lockis during routine malware inspections and confirmed that its primary objective is to encrypt valuable data and extort victims for money. Once active on a system, Lockis quickly begins encrypting files and marking them with the '.lockis' extension, making it immediately clear that the data is no longer accessible.
In addition to encrypting files, the ransomware creates a ransom note named 'how_to_back_files.html', which serves as the attackers' main communication channel with the victim.
File Encryption and Technical Claims
Lockis systematically targets user files and appends its custom extension to each encrypted item, turning familiar documents, images, and archives into unusable data. The ransom note claims that strong cryptographic algorithms, specifically RSA and AES, were used during the encryption process. Whether or not these claims are fully accurate, the result is the same for victims: files cannot be opened without a corresponding decryption key.
To increase the victim's sense of urgency and helplessness, the attackers warn that renaming files, modifying them, or attempting recovery through third-party tools will permanently damage the data.
Ransom Note, Data Theft, and Extortion Strategy
Beyond encryption, Lockis relies heavily on double-extortion tactics. The ransom note alleges that sensitive personal data has been copied and stored on a private server controlled by the attackers. If the victim refuses to cooperate, the data is supposedly at risk of being sold or leaked.
Victims are instructed to initiate contact through a Tor-based website or via specific email addresses to receive payment instructions and the decryption utility. A strict deadline is emphasized: failure to make contact within 72 hours is said to result in an increased ransom amount. This countdown mechanism is designed to pressure victims into making rushed decisions without seeking professional advice.
Recovery Challenges and the Risks of Paying
In most Lockis ransomware cases, recovering encrypted files without a valid decryption key is not feasible unless the victim has clean, unaffected backups. Legitimate third-party decryption tools are rarely available, especially for active ransomware families. While the attackers promise file restoration after payment, there is no guarantee they will deliver a working decryption tool, or respond at all.
Paying the ransom is strongly discouraged by cybersecurity professionals. It not only funds further criminal activity but also exposes victims to the risk of permanent data loss and additional extortion attempts.
Why Immediate Removal Is Critical
Removing Lockis ransomware from all infected systems is a crucial step after detection. If the malware remains active, it may continue encrypting newly created or restored files and could potentially propagate to other devices on the same network. Delayed action often leads to expanded damage, especially in environments with shared folders or weak access controls.
Common Infection Methods Used by Lockis
Lockis typically gains access through deceptive distribution channels. Malicious advertising, compromised USB devices, peer-to-peer file-sharing platforms, pirated software, and third-party downloaders are frequently abused to deliver the ransomware payload. Unpatched software vulnerabilities also provide an easy entry point for attackers.
Social engineering plays a major role as well. Users are often tricked into opening harmful files that appear to be legitimate documents, installers, scripts, ISO images, or compressed archives. Phishing emails, fake technical support messages, and compromised websites further increase the likelihood of accidental execution.
Best Security Practices to Reduce Ransomware Risk
Defending against threats like Lockis ransomware requires consistent and proactive security habits. While no single measure offers complete protection, a layered approach significantly reduces the likelihood of infection and data loss.
- Keep operating systems, applications, and security tools fully updated to close known vulnerabilities.
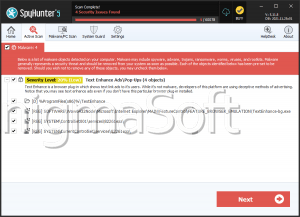
- Use reputable anti-malware solutions with real-time and behavior-based protection.
- Create regular backups of important data and store them offline or in secure cloud environments.
- Treat email attachments, links, and unexpected downloads with caution, even if they appear legitimate.
- Avoid pirated software, keygens, and unofficial download sources that commonly distribute malware.
- Restrict administrative privileges to limit the damage ransomware can cause if executed.
Closing Thoughts
Lockis Ransomware illustrates how modern ransomware combines strong encryption, data theft claims, and aggressive psychological tactics to pressure victims into compliance. While its impact can be devastating, informed users who practice good cybersecurity hygiene and maintain reliable backups are far less likely to suffer irreversible damage. Prevention, vigilance, and preparation remain the most effective defenses against ransomware attacks.