LockBeast Ransomware
Ransomware remains one of the most disruptive cyberthreats for organizations and home users alike. A single successful intrusion may lock business-critical data, halt operations, and trigger costly incident response and recovery efforts. Building layered defenses and response readiness before an outbreak is the difference between a contained event and a crisis.
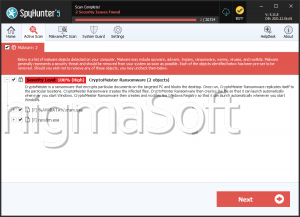
THREAT SUMMARY
Once LockBeast Ransomware is executed, it encrypts user data, modifies filenames to embed a victim identifier, and drops a ransom note titled 'README.TXT.' The operators couple encryption with data theft to pressure victims into paying, threatening to leak sensitive information if contact is not established within a set window.
ENCRYPTION AND FILE RENAMING WORKFLOW
During encryption, LockBeast appends both a victim-specific ID and the '.lockbeast' extension to targeted files. For example, '1.png' becomes '1.png.{ED08A034-A9A0-4195-3CC2-81B2521AD6B5}.lockbeast,' and '2.pdf' becomes '2.pdf.{ED08A034-A9A0-4195-3CC2-81B2521AD6B5}.lockbeast.' This pattern allows the attackers to track individual victims and confirm payment before providing any decryption capability. The encryption routine aims to cover a wide range of data types, including documents, databases, archives, media, and source code repositories.
RANSOM NOTE AND DOUBLE-EXTORTION TACTICS
The 'README.TXT' note asserts that all important files are unavailable and claims exfiltration of sensitive records, such as transaction histories, customer PII, payment card details, and account balances, to the attacker's infrastructure. The note provides contact details via privacy-focused messengers (Session and Tox), warns against renaming files or using third-party decryptors, and sets a seven-day deadline before purported data publication. This blends classic file-encryption extortion with public leak threats to increase pressure. Paying remains risky: there is no guarantee of working decryption, complete data recovery, or deletion of stolen information even if a ransom is sent.
INITIAL ACCESS AND DISTRIBUTION VECTORS
Observed and likely delivery methods align with common ransomware operations. Threat actors seed infections through malicious email attachments or links, trojanized or pirated software and keygens, social-engineering 'support' scams, and exploitation of unpatched vulnerabilities. Additional pathways include drive-by or malvertising redirects, third-party downloaders, compromised or look-alike websites, infected removable media, and peer-to-peer file sharing. Execution frequently begins when a user opens a booby-trapped executable, archive, Office, or PDF document, or script.
CONTAINMENT AND ERADICATION GUIDANCE
If LockBeast is suspected of having infected the system, act immediately. Isolate affected machines from the network (wired and wireless) to prevent further encryption and lateral spread. Disable shared drives and revoke suspicious access tokens or sessions. Preserve volatile artifacts and logs for forensics, then remove the malware using a trusted, fully updated security solution or a known-good incident response environment. Only restore from clean, offline backups after confirming the threat is eradicated; otherwise, reinfection may re-encrypt restored data.
RECOVERY AND BUSINESS IMPACT
Decryption without the attackers' tools is typically not feasible unless backups exist. Prioritize restoration of the most critical services from immutable or offline snapshots. Treat any exfiltration claim as credible until proven otherwise: assess what data may have been exposed, prepare notifications if required by law or contract, and monitor for abuse (e.g., fraud against customers).
DECISION POINTS ABOUT PAYING
While every incident has unique operational and legal considerations, paying ransom funds criminal activity and offers no guarantee of full data recovery or non-disclosure. Consider alternatives first: restoration from backups, partial data reconstruction, and customer protection measures.
BOTTOM LINE
LockBeast combines aggressive encryption with data-leak threats to coerce victims. Rapid isolation, disciplined eradication, and reliable offline backups are critical to recovery. Over the long term, organizations that invest in patching, least privilege, robust email and web controls, and realistic incident readiness dramatically reduce both the likelihood and impact of ransomware events.