Kron Ransomware
Protecting digital devices from malware is critical in today's threat landscape, where ransomware attacks continue to evolve in sophistication and impact. A single successful infection may lead to extensive data loss, operational disruption, and financial damage. The ransomware strain known as Kron Ransomware exemplifies how quickly attackers can lock down systems and pressure victims into paying for data recovery.
Table of Contents
Overview of the Kron Ransomware Threat
Kron has been identified by security researchers as a fully fledged ransomware operation. Once it is executed on a compromised system, the malware scans for user data and encrypts a wide range of files, including documents, images, databases, and other valuable content. Encrypted files are renamed by appending the '.Kron' extension, clearly signaling that the data has been locked and is no longer accessible through normal means.
Alongside the encryption routine, Kron drops a ransom note named 'R3ADM3.txt.' This file informs victims that their data has been secured using strong cryptographic methods and claims that only the attackers possess the unique decryption key required to restore access.
Ransom Note Tactics and Psychological Pressure
The ransom note is designed to instill urgency and fear. It instructs victims to contact the attackers via a specified email address to receive payment instructions and obtain the decryption key. The message emphasizes that any attempt to alter encrypted files, rename them, or use third-party recovery tools may result in permanent data loss.
To further pressure victims, the attackers impose a strict deadline, warning that failure to pay within seven days will allegedly lead to the destruction of the decryption key. Such claims are commonly used to rush decision-making and reduce the likelihood that victims will seek professional assistance.
Why Paying the Ransom Is a Risky Decision
Although the attackers promise file restoration in exchange for payment, there is no certainty that the decryption key will actually be provided. In many ransomware incidents, victims either receive faulty tools or are ignored entirely after sending the money. Even when decryption is possible, payment supports criminal activity and encourages further attacks.
In some cases, data recovery may still be achievable through clean, unaffected backups. This highlights the importance of maintaining reliable backup strategies that are isolated from the main system and not accessible to malware during an infection.
Infection Vectors and Distribution Methods
Kron Ransomware may reach victims through a variety of channels commonly abused by cybercriminals. These include peer-to-peer file sharing networks, malicious advertisements, deceptive websites, compromised installers, and infected removable media. Users are frequently deceived into launching the malware themselves by opening malicious attachments, running infected executables, or enabling harmful scripts embedded in documents.
The threat is also often associated with pirated software, cracking utilities, and key generators. In other cases, attackers exploit unpatched software vulnerabilities, abuse technical support scams, or rely on phishing emails that contain dangerous links or attachments.
System Cleanup and Containment
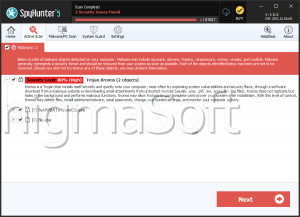
Removing Kron Ransomware from an infected device is a crucial step in limiting further damage. Once eradicated, the malware can no longer encrypt additional files or attempt to propagate across connected systems. However, removal alone does not restore encrypted data, making prevention and preparedness essential components of defense.
Strengthening Defense Against Ransomware
To reduce the risk of ransomware infections like Kron, users should adopt strong security practices and maintain a proactive approach to system protection:
- Keep operating systems, applications, and security software fully updated to close known vulnerabilities and reduce exploit opportunities.
- Use reputable anti-malware solutions with real-time protection and avoid downloading software from untrusted or unofficial sources.
Beyond these measures, users should remain cautious with email attachments and links, disable macros by default, and maintain offline or cloud-based backups that are regularly tested. Combined, these practices significantly improve resilience against ransomware attacks and help minimize the potential impact of future incidents.