Kronos
The Kronos malware was noticed for the first time in 2014 and remains active with new variants surfacing every year. The Kronos malware is categorized as a Banking Trojan that is programmed to steal your login credentials and potential verification codes for online banking portals. The Kronos Banking Trojan is based on the Zeus Banking Trojan and includes a few small modifications regarding the communication with the command servers. The Kronos Banking Trojan is used in massive email campaigns aimed at users based in Germany, Japan and Poland.
Computer security experts warn that the users in Germany are targeted with emails that are presented as coming from respected financial organizations. The phishing emails mention updates to the user's account and policy updates. The phishing emails contain Word documents with embedded macros. If you proceed to download and open the attached document, you ware shown a warning to enable macros. Deciding to trust the document would and enabling macros triggers the installation of the Kronos Banking Trojan on your device.
PC users based in Japan are targeted via a malvertising campaign, which involves several domains. Users that stumble upon the corrupted advertisements are redirected to malicious pages, which use JavaScript to loads the RIG Exploit Kit. If you have not patched your Internet-facing applications, the RIG Exploit Kit downloads and installs the Kronos malware on your PC.
The threat actors have been reported using tactics in Poland that are similar to those used in Germany. The attackers send spam emails to Polish-speaking users and pretend to deliver social media updates and credit card notifications. The emails include a Microsoft Word document that seeks to exploit the CVE-2017-11882 vulnerability (a.k.a. "Microsoft Office Memory Corruption Vulnerability") when the user opens the file. The CVE-2017-11882 vulnerability affects Microsoft Office 2007-2010-2013 and allows an attacker to run arbitrary code in the system memory. The attack results in installing the Kronos malware on the user's machine.
The Kronos Banking Trojan uses the same Web-injection techniques we have seen with the Zeus Banking Trojan. Kronos is designed to monitor the user's Web browser for specific banking portals and intercept the data loaded on your screen. The Kronos malware modifies online banking pages in real time to record the user's input. Kronos includes a module that records verification codes from your bank by creating a new form on your screen. Also, the latest version of Kronos uses the Tor anonymizing network to hide its 'Command and Control' servers.
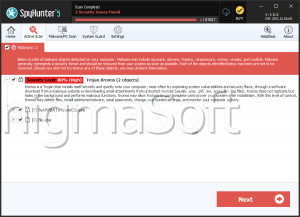
PC users are encouraged to track the funds on their bank account closely and alert their bank if there are unauthorized transactions as soon as possible. Performing weekly security scans of your computer should decrease the impact of potential Kronos attacks. Detection names for the Kronos Banking Trojan are listed below:
DLOADER.PWS.Trojan
Malicious_confidence_100% (W)
Malware.Obscure!1.9C59
PSW.Generic.FYB
TR/Crypt.ZPACK.vafyn
TROJ_KRONOS.A
TSPY_KRONBOT.A
Troj.Spy.W32.Zbot!c
TrojWare.Win32.Spy.Kronos.a
Trojan.Agent!72ozgZhFEtg
Trojan.Agent!cabQzLfMrK8
Trojan.Win32.Generic.122FA7AD
Trojan.Win32.Z.Konus.435554[h]
Trojan/Win32.Kronos.gen
Win-Trojan/Kronos.106496