Karagany
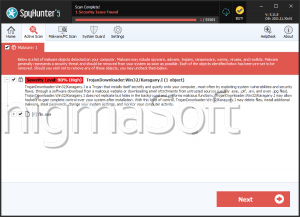
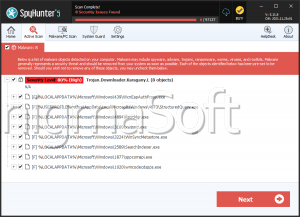
Karagany is a large family of malware loaders, also known as Trojan downloaders. These kinds of malware infections are designed to infect computers with other, more dangerous malware. Although Karagany is a severe threat, the Karagany infection is not the aim of the attack. Rather, Karagany is used to install a bookit or rogue anti-virus program on the infected computer. ESG security researchers have observed that Karagany has been associated with the Sirefef bootkit and with the FakeRean family of rogue security software. Basically, Karagany enters a computer after the victim visits a malicious website containing attack scripts designed to exploit known vulnerabilities. Computer users are baited into visiting these kinds of websites in a number of ways, often involving promises of nude pictures, shocking news stories, or hard to resist special offers on malicious advertisements.
Karagany is designed to be part of a multi-component attack on the target computer. By adding links to the attack chain, criminals can make it more difficult for PC security researchers to study these attacks, block components involved in the malware attacks, and track down the attackers. Karagany uses obfuscated code in order to prevent detection and examination. As soon as Karagany downloads and installs the malware Karagany is designed to install, Karagany deletes itself from the targeted computer, making it hard for PC security researchers to study variants in this malware family. It is important to note that a Karagany attack will seldom cause symptoms in the victim's computer. This means that Karagany can be used to install malware designed to stay hidden, such as spy Trojans and banking Trojans.
How Karagany Trojans Carry Out Their Attacks
The Karagany attack is not particularly difficult to understand. It enters the victim's computer with the help of a social engineering approach or an attack script used by an exploit kit. Once Karagany has infiltrated the victim's computer, Karagany established an HTTP connection using port 80 to a remote server. There are hundreds of malicious URLs that have been associated with Karagany attacks. Once the connection has been established, Karagany downloads and executed malicious files that will typically install a Sirefef variant or rogue security software on the victim's computer. Finally, the Karagany Trojan deletes itself and all traces of the infection from the victim's computer.


Submit Comment
Please DO NOT use this comment system for support or billing questions. For SpyHunter technical support requests, please contact our technical support team directly by opening a customer support ticket via your SpyHunter. For billing issues, please refer to our "Billing Questions or Problems?" page. For general inquiries (complaints, legal, press, marketing, copyright), visit our "Inquiries and Feedback" page.