JustIce Ransomware
Malware threats are more advanced, deceptive, and damaging than ever. Among them, ransomware attacks have emerged as one of the most disruptive types of cybercrime. These threats can encrypt critical files, cripple operations, and demand large payments in exchange for data access. One such dangerous variant, known as JustIce Ransomware, showcases the evolving tactics used by cybercriminals to exploit unsuspecting users. Understanding how JustIce operates and how to defend against it is essential for individuals and organizations alike.
Table of Contents
A Ruthless Encryptor: How JustIce Ransomware Works
JustIce Ransomware functions like many modern ransomware strains, utilizing strong encryption to lock victims out of their own files. Once the system is compromised, the malware quickly renames files by appending '.JustIce' as a new extension. For example, a harmless image file named '1.png' would be renamed to '1.png.JustIce,' while '2.pdf' becomes '2.pdf.JustIce.' This sudden alteration renders all affected files inaccessible to the user.
To make matters worse, JustIce replaces the victim's desktop wallpaper and drops a ransom note named 'README.txt.' This note informs victims that their files have been encrypted and will remain inaccessible unless a ransom is paid in cryptocurrency. The attackers urge victims to contact them at 'dr.sinaway@gmail.com' to arrange the payment, warning that any attempt to modify or rename encrypted files could result in permanent data loss.
The Ransom Dilemma: To Pay or Not to Pay?
Ransomware attackers often try to manipulate emotions, fear, urgency, and desperation, forcing victims to consider paying. However, cybersecurity experts strongly advise against complying with ransom demands. There is no guarantee that the attackers will honor their promises, and in many cases, victims never receive a decryption key even after payment.
The best and most reliable way to recover encrypted files is by restoring them from a secure and up-to-date backup. Unfortunately, if no such backup exists, recovery becomes far more difficult or even impossible without a valid decryption tool.
The Hidden Danger: Persistence and Spread
Even after initial damage is done, JustIce Ransomware poses an ongoing risk. If not fully removed from the infected device, the malware may continue encrypting newly created files or even spread across local networks, affecting additional devices. For this reason, removing the ransomware completely using reputable anti-malware software is a critical step, even before considering data recovery.
How Infection Happens: The Many Faces of Malware Delivery
JustIce doesn't arrive out of nowhere. Cybercriminals use a broad range of deceptive strategies to distribute ransomware like this. Common infection methods include:
Malicious downloads: Fake software installers, pirated applications, cracks, and license key generators often serve as Trojan horses for ransomware.
Social engineering: Phishing emails containing deceptive attachments or links are widely used to trick users into activating malware.
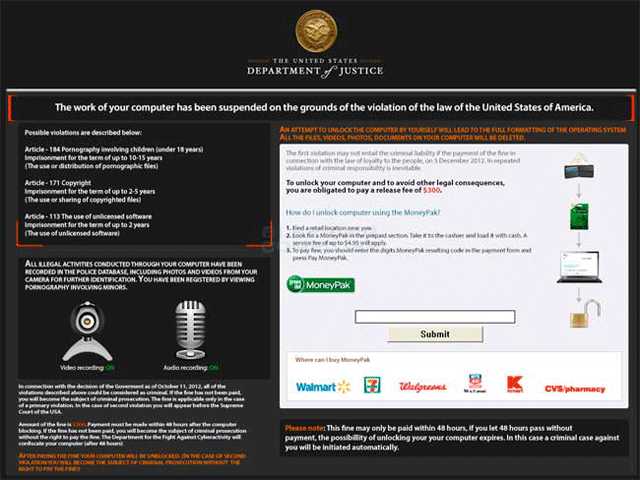
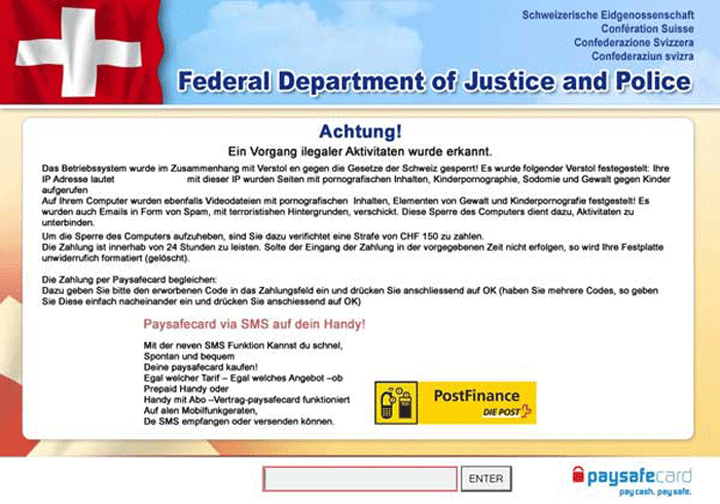
Fake tech support scams: Users may be misled into downloading malicious tools after encountering phony error messages or suspicious pop-ups.
Other methods include drive-by downloads from compromised or counterfeit websites, malicious advertisements (malvertising), peer-to-peer networks, and infected USB devices. Exploiting outdated or vulnerable software is also a favored tactic by threat actors.
Strengthening Defenses: Best Practices for Malware Prevention
Protecting your devices from threats like JustIce Ransomware requires a combination of vigilance, discipline, and reliable tools. Here are some critical steps every user should take:
- Use comprehensive security software from trusted vendors and ensure it stays up to date.
- Enable automatic updates for all software and operating systems to close vulnerabilities quickly.
- Back up your data regularly using both local (offline) and cloud-based solutions.
- Be skeptical of unsolicited messages and avoid clicking on unknown links or downloading unexpected attachments.
- Avoid pirated software and unofficial sources, which often serve as malware carriers.
In addition to these precautions, it is important to disable macros in documents by default, limit administrative privileges on user accounts, and isolate infected systems from the network to prevent lateral spread if an infection occurs.
Final Thoughts: Proactive Security is the Best Defense
JustIce Ransomware is a vivid reminder of how ruthless and sophisticated modern cyber threats can be. Its ability to encrypt data, demand payment, and persist within networks underscores the importance of a proactive and layered approach to cybersecurity. By maintaining updated defenses, practicing safe browsing and download habits, and backing up critical data, users can significantly reduce the risk of falling victim to devastating ransomware attacks.