Jopanaxye Ransomware
Jopanaxye, a recently identified malware threat, has been uncovered through in-depth analysis. This threatening software employs a file encryption technique that encrypts files and appends specific information to their filenames. The appended data includes the victim's ID, the email address jopanaxye@tutanota.com and a '.jopanaxye' extension.
To illustrate, the renaming process performed by Jopanaxye involves transforming filenames, such as '1.doc' into '1.jpg.id[9ECFA74E-3511].[jopanaxye@tutanota.com].jopanaxye,' and '2.png' into '2.png.id[9ECFA74E-3511].[jopanaxye@tutanota.com].jopanaxye,' and so on. Additionally, Jopanaxye leaves behind two ransom notes named 'info.txt' and 'info.hta.'
It is noteworthy that Jopanaxye is a ransomware variant that belongs to a ransomware family known as the Phobos Ransomware family. The presence of this malware poses a significant threat to the security and integrity of files on affected systems, necessitating prompt and effective countermeasures.
Ransomware Like Jopanaxye could Have Severe Consequences for Victims
Within the ransom note, the attackers assert that they have successfully breached confidential information, encompassing details on employees, customers, partners, accounting records and internal documentation. The note explicitly delineates the potential repercussions of non-compliance, emphasizing the looming threat of selling pilfered data on the illicit black market.
In a bid to establish communication, the hackers provide contact details, including an email address, a Telegram username, and information for a specific messenger application. The primary objective outlined in the note is to coerce the victim into remitting payment for decryption programs, with the assurance that the compromised data will be deleted upon receiving the payment.
Moreover, the note warns against involving law enforcement, third-party negotiators, or utilizing any decryption software, insinuating that such interventions could exacerbate the situation. To incentivize prompt cooperation, the attackers propose a discount for victims who initiate contact within the first six hours and conclude the transaction within a 24-hour timeframe. This multifaceted approach underscores the urgency and severity of the situation, coercing the victim into compliance through a combination of threats, incentives, and warnings.
Implement Robust Security Measures on Your Devices
Implementing effectual security measures on your devices is essential in safeguarding your digital assets and personal information. While common security practices are well-known, here are some fairly unique and effective approaches to enhance your device security:
- Regular Backups: Confirm that you regularly back up your important data to an external and offline storage solution. In the event of a ransomware attack, having recent backups enables you to restore your files without succumbing to the ransom demands.
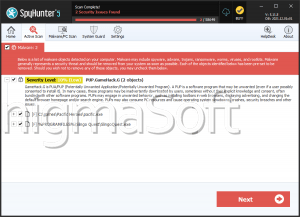
- Use Robust Anti-malware Software: Install reputable anti-malware software on your devices. Keep the software up-to-date and schedule standard scans to uncover and remove any potential threats, including ransomware.
- Email Security Practices: Exercise caution when interacting with links or opening email attachments, especially in emails from unknown or suspicious sources. Be wary of phishing attempts, as many ransomware attacks are initiated through deceptive emails.
- Software Updates: Your system and all software must br up to date with the latest security patches all the time. Regular updates can patch vulnerabilities that ransomware and other malware may exploit.
- Network Segmentation: Implement network segmentation to compartmentalize and segregate critical systems from the remaining network. This can prevent the lateral movement of ransomware within a network, limiting its impact.
- User Education and Awareness: Educate users about the dangers of ransomware and the importance of cybersecurity hygiene. Encourage them to be vigilant, report suspicious activities, and try not to download files or click on links from untrusted sources.
- Least Privilege Principle: Bond to the principle of least privilege by limiting user access rights. Users should only have the minimal amount of access requested to perform their job functions, reducing the potential impact of ransomware if an account is compromised.
By diligently implementing these security measures, users can reduce the probalitity of falling victim to ransomware attacks significantly and enhance the overall resilience of their digital environment.
The ransom note of the Jopanaxye threat is:
'!!! ATTENTION !!!
Your network is hacked and files are encrypted.
Including the encrypted data we also downloaded other confidential information: data of your employees, customers, partners, as well as accounting and other internal documentation of your company.
About Data
All data is stored until you will pay.
After payment we will provide you the programs for decryption and we will delete your data
We dont want did something bad to your company, it is just bussines (Our reputation is our money!)
If you refuse to negotiate with us (for any reason) all your data will be put up for sale.
What you will face if your data gets on the black market:
The personal information of your employees and customers may be used to obtain a loan or purchases in online stores.
You may be sued by clients of your company for leaking information that was confidential.
After other hackers obtain personal data about your employees, social engineering will be applied to your company and subsequent attacks will only intensify.
Bank details and passports can be used to create bank accounts and online wallets through which criminal money will be laundered.
You will forever lose the reputation.
You will be subject to huge fines from the government.
You can learn more about liability for data loss here: hxxps://en.wikipedia.org/wiki/General_Data_Protection_Regulationor here hxxps://gdpr-info.eu
Courts, fines and the inability to use important files will lead you to huge losses. The consequences of this will be irreversible for you.
Contacting the police will not save you from these consequences, and lost data, will only make your situation worse.
How to contact us
Write us to the mails: jopanaxye@tutanota.com
You can contact our online operator in telegram: @GROUNDINGCONDUCTOR (BE CAREFUL ABOUT FAKE)
Download the (Session) messenger https://getsession.org in messenger :ID"05bc5e20c9c6fbfd9a58bfa222cecd4bbf9b5cf4e1ecde84a0b8b3de23ce8e144e"
Write this ID in the title of your message -
IF YOU WILL CONTACT US IN FIRST 6 hours , and we close our deal in 24 hours , PRICE WILL BE ONLY 30%.
(time is money for both of us , if you will take care about our time , we will do same , we will care of price and decryption process will be done VERY FAST)
ALL DOWNLOADED DATA WILL BE DELETED after payment.
What no to do and recomendation
You can get out of this situation with minimal losses (Our reputation is our money!) !!! To do this you must strictly observe the following rules:
DO NOT Modify, DO NOT rename, DO NOT copy, DO NOT move any files. Such actions may DAMAGE them and decryption will be impossible.
DO NOT use any third party or public decryption software, it may also DAMAGE files.
DO NOT Shutdown or Reboot the system this may DAMAGE files.
DO NOT hire any third party negotiators (recovery/police, etc.) You need to contact us as soon as possible and start negotiations.
You can send us 1-2 small data not value files for test , we will decrypt it and send it to you back.
After payment we need no more that 2 hours to decrypt all of your data. We will be support you untill fully decryption going to be done! ! ! (Our reputation is our money!)'