Iconomize
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
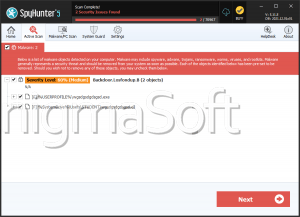
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 18,226 |
| Threat Level: | 80 % (High) |
| Infected Computers: | 26 |
| First Seen: | June 2, 2015 |
| Last Seen: | November 8, 2025 |
| OS(es) Affected: | Windows |
Iconomize is a Potentially Unwanted Program, often abbreviated as a 'PUP.' PUPs like Iconomize may be used to generate money at the expense of inexperienced computer users, who are more susceptible to low-quality Web browser toolbars, adware and other PUPs. Iconomize may be installed as a Web browser extension, toolbar or add-on. Iconomize is promoted as a useful program that can allow computer users to access special online deals and shopping opportunities. However, PUPs like Iconomize may be responsible for numerous irritating symptoms and problems on an affected computer.
Iconomize may be distributed by bundling Iconomize with other software and Iconomize may be linked to other PUPs that are installed simultaneously. Iconomize is installed in a way that allows Iconomize to start up automatically when Windows starts up and run in the background undetected, consuming the affected computer's resources. Iconomize may insert advertisements into websites viewed on the affected Web browser. Iconomize may be linked to irritating banner advertisements and obtrusive pop-up messages and advertisements. Pop-up windows associated with Iconomize may promote known tactics such as technical support hoaxes and fake Web browser and software updates. These may be used to distribute additional PUPs or even threatening content. Iconomize is was also designed to insert affiliate codes into links and cause numerous irritating symptoms such as Web browser redirects and unwanted search results.
Table of Contents
How Iconomize and Similar PUPs may Affect Your Computer
PUPs like Iconomize may drop numerous junk files on the affected computer, as well as including numerous shortcuts and links on the affected computer's desktop. Although PUPs like Iconomize may be installed as Web browser add-ons, they may have numerous effects on the overall computer, ranging from performance issues to irritating symptoms. Iconomize may try to expose computer users to known hoaxes and generate revenue by overloading the computer user with advertisements for all kinds of disreputable websites and online services. One additional issue related to Iconomize is that it may make unwanted changes to the affected Web browser's settings, including changing its homepage, default search engine and security settings (which may make it more susceptible to additional PUPs and other types of attacks).
Iconomize may be distributed by bundling Iconomize with legitimate software. In most cases, PUPs like Iconomize are promoted as 'optional' content. However, the installer is tweaked to increase the chances that computer users, especially those that are inexperienced, install Iconomize on their computer automatically. Computer users are opted into the installation Iconomize automatically. To opt out, they may have to take extra steps such as using custom installation or advanced installation options. The installer may contain convoluted or confusing instructions to make sure that computer users are never entirely sure if they are agreeing or opting out to the installation of this PUP. PUPs like Iconomize are not considered threatening, do not represent a serious risk, are not destructive nor put the PC user's privacy at a serious risk. PUPs like Iconomize, however, may lead to other, more threatening types of infections or problems on affected computers.
Removing Iconomize from a Computer
PUPs like Iconomize may not be removed in the same way one would remove any other Web browser extension. To remove Iconomize extra steps may be involved. Computer users may need to use the Windows Control Panel to remove this program, and then take extra steps to undo any unwanted changes that Iconomize may have made to the affected computer's or Web browser's settings automatically. The use of a reliable, up-to-date security program is recommended.
Analysis Report
General information
| Family Name: | Trojan.Injector.AC |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
f8b78c462771a6318cfd7a97f07a42fd
SHA1:
26a0ad22f293b7d52908405259aa4e52486324dc
SHA256:
035887D0368F699703C7D219AAC3B5AE9E9098D456D2B36E7D88B0FC5FD6AB90
File Size:
45.06 KB, 45056 bytes
|
|
MD5:
b8d1e4614e4ed55527af09215b215f66
SHA1:
101a907787d7e8cf3602e57f4dfcc06cd2766782
SHA256:
1996A0CD1D605C9BDB899BF5085CE3C458ED9627B1A7F0391181AA616B747C59
File Size:
548.86 KB, 548864 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments |
|
| Company Name |
|
| File Description | AVS executable (VB6) |
| File Version |
|
| Internal Name |
|
| Legal Copyright | www.aaa-multimedia.com 2002 |
| Legal Trademarks | Inneractive Aura Video Station |
| Original Filename |
|
| Product Name |
|
| Product Version |
|
File Traits
- vb6
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\~df12ed2fe74eb7cf75.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\~df4146de0d8217184a.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|