IcedID
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
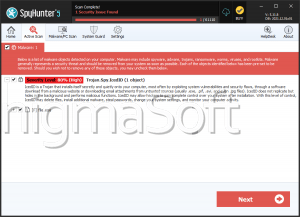
| Threat Level: | 80 % (High) |
| Infected Computers: | 2 |
| First Seen: | January 19, 2023 |
| Last Seen: | February 16, 2023 |
| OS(es) Affected: | Windows |
The IcedID malware may be listed by AV vendors as Trojan.Spy.IcedID in their databases. The IcedID software is a standalone banking Trojan that was identified in the wild in September 2017. Initially, IcedID was used to target banking systems in the USA, and it appeared to be on par with the Zeus Banking Trojan in terms of capabilities. The IcedID Trojan features a modular structure and can be expanded easily to support vertical and horizontal network movement. The IcedID Banking Trojan is distributed via another cyber-threat, which most companies refer to as Emotet. The Emotet Trojan Downloader is attached to spam emails and may take the form of macro-enabled DOCX files, a password-protected RAR archive, and executable masked as PDF files. The Emotet Trojan is designed to hijack DLLs on the user's PC and inject harmful code into 'explorer.exe,' thus, download & install threats like the IcedID malware.
The IcedID achieves boot persistence by writing a RunKey to the Registry, and it installs a proxy client on the infected machine. Hence, the network transmissions are routed to a server under the control of the IcedID team. Also, the IcedID threat can move to other end-point devices on the same computer network. IcedID can even run on terminal servers and infect printers, scanners and shared network devices. Some security experts suspect that one of the primary functions of the IcedID Trojan is to infiltrate the email clients of office employees and monitor their activities. However, the IcedID Trojan does not include advanced anti-detection technologies like identifying and terminating debugging tools, as well as identifying virtual machine environments. The IcedID is programmed to redirect users to phishing pages when it detects that a specific URL is loaded in the default Web browser. Also, the IcedID malware uses Web injects to show fields that request extra transaction authorization elements.
Cybersecurity companies reported significant improvements to IcedID in February 2019, which suggested that a large portion of its Web traffic included collected banking credentials. The February 2019 variant of IcedID included encrypted configuration files and protected its Web injects by changing the behavior of the user's Web browser. The authors of the IcedID Trojan made sure to protect their Web injects by configuring infected browsers to load external scripts from their servers. The malware verifies grabbed credit card numbers from MasterCard/AMEX/Visa using a custom algorithm as a way to minimize junk data being uploaded to the 'Command and Control' server. Not only that, but IcedID records the victim's IP address; payment card type; bot ID and last transaction event.
Manually detecting the IcedID without a reputable anti-malware suite is unlikely. The Trojan at hand may remain in stealth mode for a long period, and your banking site may not detect questionable activity since your account is operated from your device without your knowledge. It is recommended to track your financial assets daily and report unauthorized operations to your bank directly (phone and email). You can eliminate the IcedID banking Trojan using a credible security tool. Alert names for IcedID can be found below:
A Variant Of Win32/Kryptik.GLIU
HEUR/AGEN.1000927
Malware@#19hmv37kr4mnm
TSPY_EMOTET.XJB
Trojan ( 0051a2f81 )
Trojan-Banker.Win32.IcedID.x
Trojan.Johnnie.D1113F
Trojan.PWS.Banker1.23850
Trojan.Win32.S.Agent.373760.BY
Trojan/Win32.NoHead
Trojan/Win32.NoHead.C2167528
W32/Kryptik.FYGE!tr
W32/Trojan.UUFO-30944
Win.Trojan.Icedid-6379715-0