HSBC - Invoice Details Scam
Staying alert while browsing the Internet is essential, as cybercriminals continue to refine schemes that imitate trusted organizations and exploit user trust. One of the latest threats circulating online is the HSBC – Invoice Details Scam, a phishing scheme that leverages fabricated financial notifications to steal sensitive information and potentially facilitate further attacks.
Table of Contents
False Financial Notices: How the Scam Unfolds
The scam begins with an email that appears to originate from HSBC's corporate finance department. The message claims to contain details of a paid invoice, complete with an invoice number, payment reference, timestamp, and other seemingly legitimate elements. By including large payment amounts and job-related context, the scammers aim to spark urgency and cause recipients to act without verifying authenticity.
The email urges the recipient to review the invoice or download an attached file. The provided links redirect users to a counterfeit login portal designed to imitate the appearance of their actual email provider. Whether someone uses Gmail, Outlook, or another service, the fraudulent page dynamically adapts its interface to blend in convincingly. Any entered credentials are instantly harvested.
What Attackers Gain from Hijacked Email Accounts
Compromised email accounts offer direct access to sensitive communication and can be used as a launch point for further malicious activity. Attackers often exploit them to:
- Send additional phishing campaigns or malware-laden messages to contacts and colleagues.
- Attempt access to other platforms, such as banking, gaming, or social media, using the same credentials.
Once criminals gain entry, victims may face account takeovers, identity theft, unauthorized transactions, and reputational harm.
Malware Risks Hidden Behind the Message
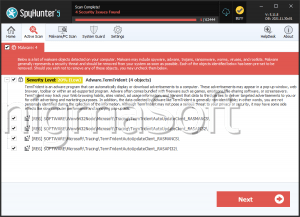
Although the primary goal is credential theft, scammers also use similar emails as vehicles for malware distribution. Attachments such as PDFs, Office documents, scripts, executables, or compressed archives may contain malicious code. If opened, or if features such as macros are enabled, infected files can compromise the device.
Alternatively, links embedded in the message may lead to unsafe websites that attempt automatic malware delivery or pressure the user into downloading harmful software. Infection typically occurs only when the recipient interacts with the malicious component, but the consequences can range from data loss to full system compromise.
Why Crypto-Related Scams Flourish
Many phishing operations, including those using banking themes, overlap with crypto-linked fraud due to the characteristics of the digital asset ecosystem. Several factors make the crypto sector especially appealing to cybercriminals. Its decentralized structure means there is no central authority capable of reversing fraudulent transactions. Once funds are transferred, they are typically gone for good.
In addition, many crypto platforms allow pseudonymous or anonymous accounts, enabling criminals to operate with limited traceability. The sector's rapid growth attracts newcomers who may not fully understand security practices, making them easier targets. The speed of transactions, global nature of exchanges, and the lack of unified regulation provide scammers with an environment where they can act quickly with relatively low risk. As a result, phishing campaigns increasingly link to fraudulent crypto' investments,' fake recovery tools, or wallet-draining pages that capitalize on these vulnerabilities.
Staying Protected Against Invoice-Based Phishing
The safest response to unexpected invoice notifications is to disregard them and verify legitimacy through known, official channels. Users should avoid opening attachments or clicking links in unsolicited messages, especially those claiming financial urgency. Multi-factor authentication, strong password practices, and security-aware browsing habits add crucial layers of defense.
The HSBC – Invoice Details Scam demonstrates how convincingly cybercriminals can mimic trusted institutions. Awareness and cautious handling of unsolicited messages remain key to preventing account compromise and financial loss.