HotPage Malware
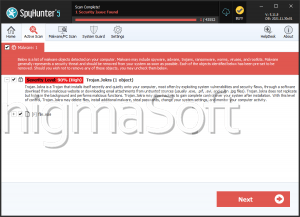
Cybersecurity researchers have uncovered an adware module that claims to block advertisements and fraudulent websites. However, it secretly installs a kernel driver component, allowing hackers to execute arbitrary code with elevated permissions on Windows systems. This malware, named HotPage, is identified by its installer file, 'HotPage.exe.'
Table of Contents
How Does the HotPage Malware Operate?
The installer sets up a driver that can inject code into remote processes, along with two libraries that intercept and manipulate browser network traffic. This malware is capable of modifying or replacing the content of Web pages, redirecting users to different pages, or opening new tabs based on specific conditions.
In addition to using its traffic interception and filtering features to display game-related advertisements, the malware is designed to collect and transmit system information to a remote server linked to Hubei Dunwang Network Technology Co., Ltd, a Chinese company.
The driver's main function is to inject these libraries into browser applications, altering their execution flow to change the accessed URL or ensure that the homepage of new browser sessions is redirected to a URL specified in its configuration.
Attackers could Gain Highest-Level Privileges on Infected Devices
The lack of access control lists (ACLs) for the driver allows an attacker with a non-privileged account to exploit it for elevated privileges, enabling them to execute code as the NT AUTHORITY\System account.
This kernel component inadvertently exposes the highest privilege level in Windows, the System account, to potential threats. Due to inadequate access restrictions, any process can interact with this component and use its code injection capability to target unprotected processes.
While the exact distribution method of the installer is unclear, there is evidence suggesting that it has been marketed as a security solution for internet cafés, claiming to enhance the browsing experience by blocking avertisements.
HotPage Malware Exploits Signed Certificate
The embedded driver of this malware is particularly notable because it is signed by Microsoft. The Chinese company behind it is believed to have met Microsoft's driver code signing requirements and obtained an Extended Verification (EV) certificate. However, the driver was removed from the Windows Server Catalog as of May 1, 2024.
Windows requires kernel-mode drivers to be digitally signed as a critical security measure to guard against fraudulent drivers that could undermine security controls and disrupt system processes.
Despite this, cybersecurity experts have discovered that native Chinese-speaking threat actors are exploiting a loophole in Microsoft Windows policy to forge signatures on kernel-mode drivers. The analysis of HotPage, which appears to be a relatively generic piece of malware, demonstrates that adware developers continue to go to great lengths to achieve their objectives.