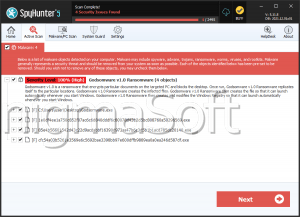
Godsomware Ransomware
PC security researchers first observed the Godsomware Ransomware, a ransomware Trojan, on October 6, 2018. Threats like the Godsomware Ransomware can be installed on a targeted computer in many different ways. The most common ways in which the victims of the Godsomware Ransomware have become infected by this threat is after opening an unsolicited email attachment, delivered through spam email or via cracked copies of pirated software and PC games. These are common ways of delivering threats, and computer users are urged to take care when dealing with this content type. The initial wave of the Godsomware Ransomware attacks does not include encryption capabilities and is more of a lock screen than an encryption ransomware Trojan. However, it is not difficult to add encryption capabilities to these threats, and it is common for lock screen Trojans to include this capability eventually as criminals continue developing them.
Table of Contents
How the Godsomware Ransomware Attacks a Computer
The Godsomware Ransomware seems to behave like a prank program rather than a serious threat. Threats like these were noticed in the early 2000s, often distributed via emails. They would take the form of email attachments that display images, texts, and audio on the victim's computer while disabling input devices such as the keyboard or the infected computer's mouse. The Godsomware Ransomware differs from most encryption ransomware Trojans in the fact that these typically target specific file types, using a strong encryption method to prevent the victim from accessing the files' contents. Rather than doing this, the Godsomware Ransomware simply prevents the victim from using the affected computer as normal.
Symptoms of Attacks Like the Godsomware Ransomware
Computer users have reported that the Godsomware Ransomware will fill the affected computer with GIF animations and display numerous windows with unwanted pictures on the infected PC. Victims of the Godsomware Ransomware will continue to have access to the Windows Task Manager, and their mouses will remain operational. The Godsomware Ransomware displays a ransom note that seems to be similar to the one exhibited by the WannaCry Ransomware, a high-profile encryption ransomware Trojan. Some versions of the Godsomware Ransomware also will display a fake ransom note that claims that it is necessary to pay 100 USD using Bitcoin, claiming that the victim's files were encrypted. However, these messages should be ignored; the Godsomware Ransomware in its current form is not capable of encrypting data.
Dealing with Threats Like the Godsomware Ransomware
If your machine has been infected with the Godsomware Ransomware, the best protection is to have a security program capable of dealing with threats like the Godsomware Ransomware. It is also crucial to have other security components such as a reliable firewall and anti-spam filter. Threats like the Godsomware Ransomware are often distributed through corrupted file downloads and spam email attachments so that learning to deal with this content is essential. Fortunately, it is possible to remove the Godsomware Ransomware lock screen through the use of the password 29b579fb811f05c3c334a2bd2646a27a, which will disable the Godsomware Ransomware lock screen immediately. However, even after this is done, the computer user should take steps to ensure that all components linked to the Godsomware Ransomware are removed completely and thoroughly. Threats like the Godsomware Ransomware are rarely installed by themselves, and it is likely that other threats may have found their way onto the targeted computer. After stopping the Godsomware Ransomware lock screen, computer users need to take steps to remove all traces of other threats by running a full, thorough scan of their hard drives with a security application. It is also necessary to check any application and operating system settings and restore them to their defaults if these have been changed in any way by the Godsomware Ransomware.