Ghokswa Browser
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 197 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 510,116 |
| First Seen: | November 18, 2015 |
| Last Seen: | June 2, 2026 |
| OS(es) Affected: | Windows |
Computer users with Google Chrome as their default Web browser have reported that they have received messages from a different Web browser, noting that instead of Chrome, the Ghokswa Browser was set as their default Web browser. These pop-ups, associated with a published named 'BYSENDA TECHNOLOGIES LIMITED' prompt computer users to install 'BROWSERSERVER.EXE' on their computers. This Web browser, known as the Ghokswa Browser, looks and acts like Google Chrome, but presents different behaviors. The Ghokswa Browser is used to collect the Google login credentials of computer users, monitor their online activities, and expose them to unwanted advertising content. The Ghokswa Browser may change the affected computer's shortcuts, both on the Desktop and the Start Menu. Computer users clicking on these shortcuts expecting to launch Google Chrome will, instead, launch the Ghokswa Browser, often without realizing it because of the resemblance between the Ghokswa Browser and Google Chrome. If the Ghokswa Browser is installed on your computer, remove the Ghokswa Browser at once, perform a full scan of your computer with a reliable security application, and take steps to ensure that your online credentials have not been compromised.
Table of Contents
The Ghokswa Browser has no Connection with Google Chrome
As part of the Ghokswa Browser, this fake version of the Google Chrome Web browser is used to trick inexperienced computer users into thinking that they are using Google Chrome. When computer users are prompted to log into their Google account, they may be giving their login information to the people responsible for the Ghokswa Browser. After the Ghokswa Browser is removed, it is impossible to check and make sure that all shortcuts (including those on the Task Bar, Start Menu and Desktop) direct to Google Chrome rather than to the Ghokswa Browser. Although other versions of this hoax were easy to spot using Task Manager, the executable file and memory process associated with the Ghokswa Browser is still Chrome.exe. However, if one tracks the file down, it is actually in the Ghokswa Browser folder rather than in the usual location for the Google Chrome Web browser. The Ghokswa Browser may be linked to other unwanted software, including a bogus 'unzipper' for managing ZIP or RAR files on Windows.
How the Ghokswa Browser Tactic Works
The main strategy of the Ghokswa Browser is to impersonate the Google Chrome Web browser. There are several ways this may be exploited: if computer users believe that they are using a reputable Web browser like Google Chrome, they may disclose information such as online banking credentials and Google login information. The tactic also may work the other way and the people responsible for the Ghokswa Browser also may use this Web browser to deliver unwanted advertisements or redirections without the need of a PUP or adware because, in this case, the entire Web browser is compromised. Google Chrome will still be on the affected computer; it is not deleted as part of the Ghokswa Browser installation process. However, without alerting the computer user, the affected computer's default Web browser will be changed to the Ghokswa Browser. All relevant shortcuts will be replaced so that they launch the Ghokswa Browser instead of Google Chrome.
Dealing with the Ghokswa Browser
If the Ghokswa Browser has been installed on your computer, the Ghokswa Browser should be uninstalled. It may be necessary to uninstall the Ghokswa Browser manually, as well as delete all files associated with the Ghokswa Browser. Computer users should confirm that all shortcuts effectively lead to Google Chrome again. It may also be necessary to use the Registry Editor to delete all registry key related to this bogus Web browser. PC security researchers recommend performing a full scan of your computer with the help of a reliable security application that is fully up-to-date to ensure that no threat has been installed, either as a result of the Ghokswa Browser or as part of its delivery to your computer.
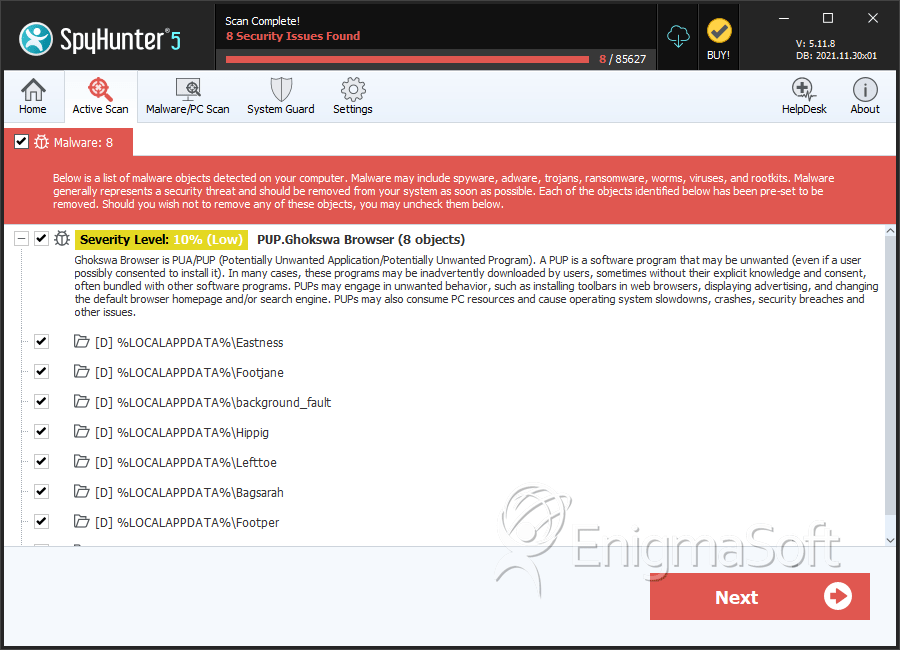
SpyHunter Detects & Remove Ghokswa Browser
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | uploader.dll | 063d0760944aa9feff5a63599183ca1e | 1,544 |
| 2. | provider.dll | 444c6621caed712fafa7fa0afc8c5be7 | 522 |
| 3. | chk.dll | 9260fcee39be90620e1f202590c40f97 | 171 |
| 4. | Firefox.exe | 34d63ff24f0c71b643d229253db1cb2d | 143 |
| 5. | appv.dll | 79d096f16e7538c2df69f61403b06da8 | 104 |
| 6. | dbg.dll | 51fdc4d5a3f458e10123cbadbf77f4bf | 103 |
| 7. | trzBAD6.tmp | 4c1c3aaafacc78ee820ca5e98ecf43e4 | 96 |
| 8. | FirefoxUpdate.exe | afd0c49288860c4e8c61484c24f0fdac | 72 |
| 9. | 9bcb3fab78e80d68be28892ea7ad46c3.msp.dll | 77cd97afc91d1e31bd8e2023fab25b90 | 55 |
| 10. | chkver.dll | f31cccc81416f9cbcf6b78fec1d0a3e9 | 50 |
| 11. | 4e29234340aaf3a96ec480c1aad8d179.cab:ad | 51fe179e199b04bb3e82558fd5a9183b | 33 |
| 12. | ppcrlconfig617.dll | 12699c22a6cd88a31b9cb670c29ceb2b | 23 |
| 13. | MobileIntellisense.dll | c101020efe777f6badce99a8f152ec77 | 19 |
| 14. | helper.dll | 733ccd349c8d6a86ff6bd0a65a82b901 | 18 |
| 15. | Integrator.dll | a4030f19a6672564adb9f6e90222f7c9 | 18 |
| 16. | SyncTool.dll | 872840e19332703410f557fd374c44b8 | 18 |
| 17. | appidsvr.dll | 66edd44eb8353805b4ed081f4aab0e2e | 17 |
| 18. | Appinfo.dll | 7f07d0a50a65f6d24297f5c4428ffaef | 14 |
| 19. | iisexp.dll | f3922eb8251356a2e2913718f5c69925 | 6 |
| 20. | PackageLocker.dll | 73e165be0fe990382bae26b8c71a4a04 | 4 |
| 21. | msdeploy.resources.dll | ae88db5467abeb4d91c511c5e468c25d | 4 |
| 22. | Descriptor.dll | 4b36b6e7d0699dd1e3fc0142a63b04d0 | 2 |
| 23. | 30daf459e79c5d26366654b1b482e87.cab:dp | 11552c35ea61525d8ba2102eeec1ae38 | 2 |
| 24. | 9bcb3fab78e80d68be28892ea7ad46c3.msp:dp | 8181dc651a89923800a109c9629d957f | 1 |
| 25. | 1.1.4322__2.3.0.2.dll | a2201686f1f6eca16e7331feea4c7a29 | 1 |
| 26. | SDKFilesVer.dll | 2311c387be305e70dc6103bb623c3f4d | 1 |
Registry Details
Directories
Ghokswa Browser may create the following directory or directories:
| %ALLUSERSPROFILE%\Application Data\Inbob |
| %ALLUSERSPROFILE%\Bagbin |
| %ALLUSERSPROFILE%\Banglamp |
| %ALLUSERSPROFILE%\Birdeye |
| %ALLUSERSPROFILE%\Birdmay |
| %ALLUSERSPROFILE%\Bookfat |
| %ALLUSERSPROFILE%\Bossseed |
| %ALLUSERSPROFILE%\Eastmy |
| %ALLUSERSPROFILE%\Eastness |
| %ALLUSERSPROFILE%\Fishlose |
| %ALLUSERSPROFILE%\Footblue |
| %ALLUSERSPROFILE%\Gotoe |
| %ALLUSERSPROFILE%\Hotdear |
| %ALLUSERSPROFILE%\Hotmay |
| %ALLUSERSPROFILE%\Inbob |
| %ALLUSERSPROFILE%\Jamben |
| %ALLUSERSPROFILE%\Jamjob |
| %ALLUSERSPROFILE%\Junetoe |
| %ALLUSERSPROFILE%\Newjob |
| %ALLUSERSPROFILE%\Onfat |
| %ALLUSERSPROFILE%\Setmike |
| %ALLUSERSPROFILE%\Weness |
| %ALLUSERSPROFILE%\Zootony |
| %ALLUSERSPROFILE%\ceQeekg |
| %ALLUSERSPROFILE%\redjane |
| %ALLUSERSPROFILE%\seteat |
| %APPDATA%\go00001 |
| %LOCALAPPDATA%\Allold |
| %LOCALAPPDATA%\Alltoe |
| %LOCALAPPDATA%\Antanna |
| %LOCALAPPDATA%\Antper |
| %LOCALAPPDATA%\Applefat |
| %LOCALAPPDATA%\Applemy |
| %LOCALAPPDATA%\Bagbin |
| %LOCALAPPDATA%\Baghair |
| %LOCALAPPDATA%\Baglook |
| %LOCALAPPDATA%\Bagsarah |
| %LOCALAPPDATA%\Ballcine |
| %LOCALAPPDATA%\Ballduck |
| %LOCALAPPDATA%\Bangcar |
| %LOCALAPPDATA%\Banglamp |
| %LOCALAPPDATA%\Bangone |
| %LOCALAPPDATA%\Bangtony |
| %LOCALAPPDATA%\Bedhat |
| %LOCALAPPDATA%\Bedkiss |
| %LOCALAPPDATA%\Bemike |
| %LOCALAPPDATA%\Bepat |
| %LOCALAPPDATA%\Bigflat |
| %LOCALAPPDATA%\Bigold |
| %LOCALAPPDATA%\Birdeye |
| %LOCALAPPDATA%\Birdkiss |
| %LOCALAPPDATA%\Birdmay |
| %LOCALAPPDATA%\Birdsarah |
| %LOCALAPPDATA%\Bookfat |
| %LOCALAPPDATA%\Bossface |
| %LOCALAPPDATA%\Bossseed |
| %LOCALAPPDATA%\Bossship |
| %LOCALAPPDATA%\Boxbob |
| %LOCALAPPDATA%\Boxfat |
| %LOCALAPPDATA%\Cansuck |
| %LOCALAPPDATA%\Coldmay |
| %LOCALAPPDATA%\Coldold |
| %LOCALAPPDATA%\Coldone |
| %LOCALAPPDATA%\Cupblue |
| %LOCALAPPDATA%\Cupface |
| %LOCALAPPDATA%\Cuppat |
| %LOCALAPPDATA%\Daydoor |
| %LOCALAPPDATA%\Docine |
| %LOCALAPPDATA%\Doeye |
| %LOCALAPPDATA%\Dohat |
| %LOCALAPPDATA%\Doold |
| %LOCALAPPDATA%\Eastmy |
| %LOCALAPPDATA%\Eastness |
| %LOCALAPPDATA%\Eggness |
| %LOCALAPPDATA%\Evercine |
| %LOCALAPPDATA%\Everness |
| %LOCALAPPDATA%\Fishjane |
| %LOCALAPPDATA%\Fishlamp |
| %LOCALAPPDATA%\Fishlose |
| %LOCALAPPDATA%\Footblue |
| %LOCALAPPDATA%\Footeat |
| %LOCALAPPDATA%\Footjane |
| %LOCALAPPDATA%\Footlook |
| %LOCALAPPDATA%\Footper |
| %LOCALAPPDATA%\Gofat |
| %LOCALAPPDATA%\Goldass |
| %LOCALAPPDATA%\Gotoe |
| %LOCALAPPDATA%\Gunone |
| %LOCALAPPDATA%\Gunship |
| %LOCALAPPDATA%\Hipbear |
| %LOCALAPPDATA%\Hipeat |
| %LOCALAPPDATA%\Hipfat |
| %LOCALAPPDATA%\Hipmy |
| %LOCALAPPDATA%\Hippig |
| %LOCALAPPDATA%\Hisarah |
| %LOCALAPPDATA%\Hotdear |
| %LOCALAPPDATA%\Hothair |
| %LOCALAPPDATA%\Hotjob |
| %LOCALAPPDATA%\Hotleaf |
| %LOCALAPPDATA%\Hotmay |
| %LOCALAPPDATA%\Inbob |
| %LOCALAPPDATA%\Infun |
| %LOCALAPPDATA%\Inper |
| %LOCALAPPDATA%\Jamben |
| %LOCALAPPDATA%\Jamjob |
| %LOCALAPPDATA%\Jamlarry |
| %LOCALAPPDATA%\Jamsarah |
| %LOCALAPPDATA%\Jarhair |
| %LOCALAPPDATA%\Jarness |
| %LOCALAPPDATA%\Junedoor |
| %LOCALAPPDATA%\Junetoe |
| %LOCALAPPDATA%\Lefttoe |
| %LOCALAPPDATA%\Legness |
| %LOCALAPPDATA%\Legpat |
| %LOCALAPPDATA%\Mapbob |
| %LOCALAPPDATA%\Mapcar |
| %LOCALAPPDATA%\Moncar |
| %LOCALAPPDATA%\Monold |
| %LOCALAPPDATA%\Newjob |
| %LOCALAPPDATA%\Nobean |
| %LOCALAPPDATA%\Nolarry |
| %LOCALAPPDATA%\Nosekiss |
| %LOCALAPPDATA%\Nosemay |
| %LOCALAPPDATA%\Onfat |
| %LOCALAPPDATA%\Ontoe |
| %LOCALAPPDATA%\Outbob |
| %LOCALAPPDATA%\Outfire |
| %LOCALAPPDATA%\Outlose |
| %LOCALAPPDATA%\Pearhas |
| %LOCALAPPDATA%\Seablue |
| %LOCALAPPDATA%\Seaness |
| %LOCALAPPDATA%\Setleaf |
| %LOCALAPPDATA%\Setmike |
| %LOCALAPPDATA%\Shutness |
| %LOCALAPPDATA%\Stancine |
| %LOCALAPPDATA%\Standoor |
| %LOCALAPPDATA%\Standuck |
| %LOCALAPPDATA%\Stanper |
| %LOCALAPPDATA%\Tooleat |
| %LOCALAPPDATA%\Toolhair |
| %LOCALAPPDATA%\Toolrain |
| %LOCALAPPDATA%\Tooltony |
| %LOCALAPPDATA%\Wefat |
| %LOCALAPPDATA%\Weness |
| %LOCALAPPDATA%\Yeahfire |
| %LOCALAPPDATA%\Yeahseed |
| %LOCALAPPDATA%\Yeahship |
| %LOCALAPPDATA%\Yesdear |
| %LOCALAPPDATA%\Yeshat |
| %LOCALAPPDATA%\Yestony |
| %LOCALAPPDATA%\Zooarm |
| %LOCALAPPDATA%\Zooface |
| %LOCALAPPDATA%\Zootony |
| %LOCALAPPDATA%\background_fault |
| %LOCALAPPDATA%\birdjob |
| %LOCALAPPDATA%\ceQeekg |
| %LOCALAPPDATA%\fishhas |
| %LOCALAPPDATA%\hotcine |
| %LOCALAPPDATA%\legass |
| %LOCALAPPDATA%\redjane |
| %LOCALAPPDATA%\seteat |
| %LOCALAPPDATA%\vreXjvX |
| %PROGRAMFILES%\Alltoe |
| %PROGRAMFILES%\Antanna |
| %PROGRAMFILES%\Antper |
| %PROGRAMFILES%\Applefat |
| %PROGRAMFILES%\Applemy |
| %PROGRAMFILES%\Bagbin |
| %PROGRAMFILES%\Baghair |
| %PROGRAMFILES%\Baglook |
| %PROGRAMFILES%\Bagsarah |
| %PROGRAMFILES%\Ballcine |
| %PROGRAMFILES%\Ballduck |
| %PROGRAMFILES%\Bangcar |
| %PROGRAMFILES%\Banglamp |
| %PROGRAMFILES%\Bangtony |
| %PROGRAMFILES%\Bedhat |
| %PROGRAMFILES%\Bedkiss |
| %PROGRAMFILES%\Bemike |
| %PROGRAMFILES%\Bepat |
| %PROGRAMFILES%\Bigflat |
| %PROGRAMFILES%\Bigold |
| %PROGRAMFILES%\Birdeye |
| %PROGRAMFILES%\Birdmay |
| %PROGRAMFILES%\Bookfat |
| %PROGRAMFILES%\Bossface |
| %PROGRAMFILES%\Bossseed |
| %PROGRAMFILES%\Bossship |
| %PROGRAMFILES%\Boxbob |
| %PROGRAMFILES%\Boxfat |
| %PROGRAMFILES%\Cansuck |
| %PROGRAMFILES%\Coldmay |
| %PROGRAMFILES%\Coldold |
| %PROGRAMFILES%\Coldone |
| %PROGRAMFILES%\Cupface |
| %PROGRAMFILES%\Cuppat |
| %PROGRAMFILES%\Doeye |
| %PROGRAMFILES%\Dohat |
| %PROGRAMFILES%\Eastmy |
| %PROGRAMFILES%\Eastness |
| %PROGRAMFILES%\Eggness |
| %PROGRAMFILES%\Evercine |
| %PROGRAMFILES%\Everness |
| %PROGRAMFILES%\Fishjane |
| %PROGRAMFILES%\Fishlose |
| %PROGRAMFILES%\Footblue |
| %PROGRAMFILES%\Footeat |
| %PROGRAMFILES%\Footjane |
| %PROGRAMFILES%\Footlook |
| %PROGRAMFILES%\Footper |
| %PROGRAMFILES%\Gofat |
| %PROGRAMFILES%\Goldass |
| %PROGRAMFILES%\Gotoe |
| %PROGRAMFILES%\Gunone |
| %PROGRAMFILES%\Hipeat |
| %PROGRAMFILES%\Hipmy |
| %PROGRAMFILES%\Hippig |
| %PROGRAMFILES%\Hotdear |
| %PROGRAMFILES%\Hothair |
| %PROGRAMFILES%\Hotjob |
| %PROGRAMFILES%\Hotleaf |
| %PROGRAMFILES%\Hotmay |
| %PROGRAMFILES%\Inbob |
| %PROGRAMFILES%\Infun |
| %PROGRAMFILES%\Inper |
| %PROGRAMFILES%\Jamben |
| %PROGRAMFILES%\Jamjob |
| %PROGRAMFILES%\Jamlarry |
| %PROGRAMFILES%\Jarhair |
| %PROGRAMFILES%\Jarness |
| %PROGRAMFILES%\Junetoe |
| %PROGRAMFILES%\Legness |
| %PROGRAMFILES%\Lerfopervather Host |
| %PROGRAMFILES%\MIO\loader |
| %PROGRAMFILES%\Mapbob |
| %PROGRAMFILES%\Moncar |
| %PROGRAMFILES%\Newjob |
| %PROGRAMFILES%\Nolarry |
| %PROGRAMFILES%\Nosekiss |
| %PROGRAMFILES%\Onfat |
| %PROGRAMFILES%\Ontoe |
| %PROGRAMFILES%\Outbob |
| %PROGRAMFILES%\Pearhas |
| %PROGRAMFILES%\Setleaf |
| %PROGRAMFILES%\Setmike |
| %PROGRAMFILES%\Shutness |
| %PROGRAMFILES%\Stancine |
| %PROGRAMFILES%\Standoor |
| %PROGRAMFILES%\Standuck |
| %PROGRAMFILES%\Stanper |
| %PROGRAMFILES%\Tooleat |
| %PROGRAMFILES%\Toolhair |
| %PROGRAMFILES%\Tooltony |
| %PROGRAMFILES%\Weness |
| %PROGRAMFILES%\Yeahfire |
| %PROGRAMFILES%\Yeahseed |
| %PROGRAMFILES%\Yeahship |
| %PROGRAMFILES%\Yeshat |
| %PROGRAMFILES%\Zooarm |
| %PROGRAMFILES%\Zootony |
| %PROGRAMFILES%\birdjob |
| %PROGRAMFILES%\fishhas |
| %PROGRAMFILES%\hotcine |
| %PROGRAMFILES%\legass |
| %PROGRAMFILES%\redjane |
| %PROGRAMFILES%\seteat |
| %PROGRAMFILES(x86)%\Alltoe |
| %PROGRAMFILES(x86)%\Antanna |
| %PROGRAMFILES(x86)%\Antper |
| %PROGRAMFILES(x86)%\Applefat |
| %PROGRAMFILES(x86)%\Applemy |
| %PROGRAMFILES(x86)%\Bagbin |
| %PROGRAMFILES(x86)%\Baghair |
| %PROGRAMFILES(x86)%\Baglook |
| %PROGRAMFILES(x86)%\Bagsarah |
| %PROGRAMFILES(x86)%\Ballcine |
| %PROGRAMFILES(x86)%\Ballduck |
| %PROGRAMFILES(x86)%\Bangcar |
| %PROGRAMFILES(x86)%\Banglamp |
| %PROGRAMFILES(x86)%\Bangtony |
| %PROGRAMFILES(x86)%\Bedhat |
| %PROGRAMFILES(x86)%\Bedkiss |
| %PROGRAMFILES(x86)%\Bemike |
| %PROGRAMFILES(x86)%\Bepat |
| %PROGRAMFILES(x86)%\Bigflat |
| %PROGRAMFILES(x86)%\Bigold |
| %PROGRAMFILES(x86)%\Birdeye |
| %PROGRAMFILES(x86)%\Birdmay |
| %PROGRAMFILES(x86)%\Bookfat |
| %PROGRAMFILES(x86)%\Bossface |
| %PROGRAMFILES(x86)%\Bossseed |
| %PROGRAMFILES(x86)%\Bossship |
| %PROGRAMFILES(x86)%\Boxbob |
| %PROGRAMFILES(x86)%\Boxfat |
| %PROGRAMFILES(x86)%\Cansuck |
| %PROGRAMFILES(x86)%\Coldmay |
| %PROGRAMFILES(x86)%\Coldold |
| %PROGRAMFILES(x86)%\Coldone |
| %PROGRAMFILES(x86)%\Cupface |
| %PROGRAMFILES(x86)%\Cuppat |
| %PROGRAMFILES(x86)%\Daydoor |
| %PROGRAMFILES(x86)%\Doeye |
| %PROGRAMFILES(x86)%\Dohat |
| %PROGRAMFILES(x86)%\Eastmy |
| %PROGRAMFILES(x86)%\Eastness |
| %PROGRAMFILES(x86)%\Eggness |
| %PROGRAMFILES(x86)%\Evercine |
| %PROGRAMFILES(x86)%\Everness |
| %PROGRAMFILES(x86)%\Fishjane |
| %PROGRAMFILES(x86)%\Fishlose |
| %PROGRAMFILES(x86)%\Footblue |
| %PROGRAMFILES(x86)%\Footeat |
| %PROGRAMFILES(x86)%\Footjane |
| %PROGRAMFILES(x86)%\Footlook |
| %PROGRAMFILES(x86)%\Footper |
| %PROGRAMFILES(x86)%\Gofat |
| %PROGRAMFILES(x86)%\Goldass |
| %PROGRAMFILES(x86)%\Gotoe |
| %PROGRAMFILES(x86)%\Gunone |
| %PROGRAMFILES(x86)%\Hipeat |
| %PROGRAMFILES(x86)%\Hipmy |
| %PROGRAMFILES(x86)%\Hippig |
| %PROGRAMFILES(x86)%\Hotdear |
| %PROGRAMFILES(x86)%\Hothair |
| %PROGRAMFILES(x86)%\Hotjob |
| %PROGRAMFILES(x86)%\Hotleaf |
| %PROGRAMFILES(x86)%\Hotmay |
| %PROGRAMFILES(x86)%\Inbob |
| %PROGRAMFILES(x86)%\Infun |
| %PROGRAMFILES(x86)%\Inper |
| %PROGRAMFILES(x86)%\Jamben |
| %PROGRAMFILES(x86)%\Jamjob |
| %PROGRAMFILES(x86)%\Jamlarry |
| %PROGRAMFILES(x86)%\Jarhair |
| %PROGRAMFILES(x86)%\Jarness |
| %PROGRAMFILES(x86)%\Junetoe |
| %PROGRAMFILES(x86)%\Legness |
| %PROGRAMFILES(x86)%\Lerfopervather Host |
| %PROGRAMFILES(x86)%\MIO\loader |
| %PROGRAMFILES(x86)%\Mapbob |
| %PROGRAMFILES(x86)%\Moncar |
| %PROGRAMFILES(x86)%\Newjob |
| %PROGRAMFILES(x86)%\Nolarry |
| %PROGRAMFILES(x86)%\Nosekiss |
| %PROGRAMFILES(x86)%\Onfat |
| %PROGRAMFILES(x86)%\Ontoe |
| %PROGRAMFILES(x86)%\Outbob |
| %PROGRAMFILES(x86)%\Pearhas |
| %PROGRAMFILES(x86)%\Setleaf |
| %PROGRAMFILES(x86)%\Setmike |
| %PROGRAMFILES(x86)%\Shutness |
| %PROGRAMFILES(x86)%\Stancine |
| %PROGRAMFILES(x86)%\Standoor |
| %PROGRAMFILES(x86)%\Standuck |
| %PROGRAMFILES(x86)%\Stanper |
| %PROGRAMFILES(x86)%\Tooleat |
| %PROGRAMFILES(x86)%\Toolhair |
| %PROGRAMFILES(x86)%\Tooltony |
| %PROGRAMFILES(x86)%\Weness |
| %PROGRAMFILES(x86)%\Yeahfire |
| %PROGRAMFILES(x86)%\Yeahseed |
| %PROGRAMFILES(x86)%\Yeahship |
| %PROGRAMFILES(x86)%\Yeshat |
| %PROGRAMFILES(x86)%\Zooarm |
| %PROGRAMFILES(x86)%\Zootony |
| %PROGRAMFILES(x86)%\birdjob |
| %PROGRAMFILES(x86)%\fishhas |
| %PROGRAMFILES(x86)%\hotcine |
| %PROGRAMFILES(x86)%\legass |
| %PROGRAMFILES(x86)%\redjane |
| %PROGRAMFILES(x86)%\seteat |
| %UserProfile%\Local Settings\Application Data\Weness |
| %UserProfile%\Local Settings\Application Data\Yestony |
Analysis Report
General information
| Family Name: | PUP.Ghokswa Browser |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
3fd4a18dd50b38f69fb9f1378c696cf6
SHA1:
b23b95b7ed8805643ccd007facdfb04ec2eff1e6
SHA256:
08D8A5A7F437FA0236885312301A5D8ABE6181E36790C1D1F608252975D43553
File Size:
293.59 KB, 293592 bytes
|
|
MD5:
c47ea0f342fa1a83a93105aed3f2de80
SHA1:
542ffa2ed78f0ba55eeee4f6e57da84631ada659
SHA256:
E4F3FB36E0672AB34392DA614536FF4C50BA6654A38528E051CC7BDEB343986D
File Size:
12.29 KB, 12288 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have exports table
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Build I D | 20160928101353 |
| Company Name | Mozilla Foundation |
| File Version |
|
| Legal Copyright | License: MPL 2 |
| Legal Trademarks | Mozilla |
| Original Filename | AccessibleMarshal.dll |
| Product Name | Firefox |
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Shan Feng | thawte SHA256 Code Signing CA | Self Signed |
File Traits
- 2+ executable sections
- dll
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 24 |
|---|---|
| Potentially Malicious Blocks: | 0 |
| Whitelisted Blocks: | 24 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Network Info Queried |
|
| Encryption Used |
|
| Network Wininet |
|
| Network Winhttp |
|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\542ffa2ed78f0ba55eeee4f6e57da84631ada659_0000012288.,LiQMAxHB
|
