Full Storage Notification Email Scam
In the fast-paced digital world, vigilance is not just a precaution; it is a necessity. Cybercriminals are increasingly sophisticated, leveraging common concerns to deceive users. One such deceptive tactic is the 'Full Storage Notification' email scam, which preys on users' fear of losing access to their email accounts. By mimicking legitimate service alerts, these phishing attempts lure individuals into revealing sensitive information. Understanding the mechanics of this tactic and knowing how to avoid it is critical for safeguarding your personal and financial well-being.
The Anatomy of the 'Full Storage Notification' Scam
At first glance, the 'Full Storage Notification' email appears genuine. With subject lines like 'Free up space!' it claims the recipient's email inbox has reached its storage capacity. The message urges immediate action, often warning that failure to respond could result in service interruptions, email deletions, or account restrictions.
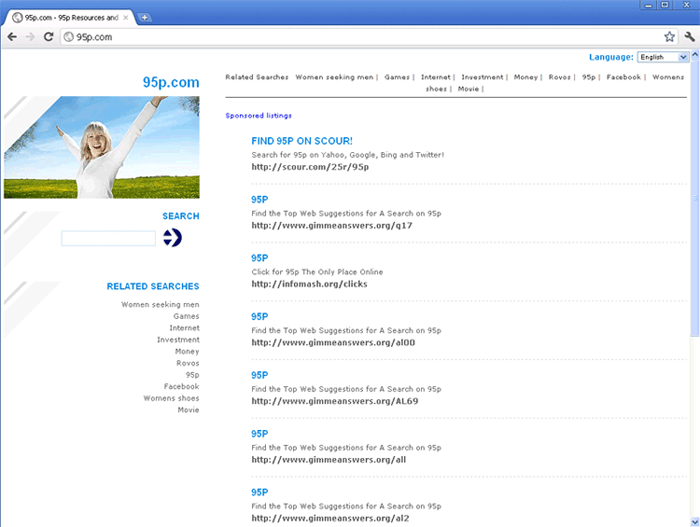
The email includes a prominent call-to-action, such as a 'Clear Cache' button, which redirects users to a deceptive website resembling a legitimate email service provider's login page. This page requests users to re-enter their credentials to resolve the supposed issue.
Unfortunately, fraudsters capture any information entered on this fake page. These stolen credentials can then be used for a range of malicious activities, from unauthorized account access to further phishing campaigns targeting others.
The True Cost of Falling Victim
The consequences of providing login credentials to fraudsters extend far beyond losing access to an email account. Cybercriminals can exploit stolen accounts in multiple ways:
- Hijacking Personal or Professional Identities: Fraudsters may use compromised accounts to impersonate victims, send fraudulent messages to contacts to solicit money or distribute malicious links.
- Accessing Sensitive Data: Emails often contain personal and financial information, contracts, invoices, and other confidential materials. Cybercriminals can leverage this data for extortion or identity theft.
- Expanding the Attack Surface: A compromised email address may serve as the gateway to other linked services, including social media, online banking, or e-commerce platforms. Scammers may attempt password resets on these accounts, leading to further breaches.
- Monetizing Stolen Information: In addition to direct exploitation, stolen credentials are frequently sold on the dark web, enabling other cybercriminals to misuse the information.
Victims may experience financial losses, damaged reputations, or even legal complications, mainly if fraudulent activities are carried out using their accounts.
A Sophisticated Deception: Spotting the Warning Signs
While some phishing emails are poorly constructed and have evident errors, others are alarmingly professional, mimicking authentic communication from service providers, companies, or institutions. Indicators of fraudulent emails include:
- Claims of urgency, pressuring recipients to act quickly.
- Generic greetings like 'Dear User' instead of addressing the recipient by name.
- Links or buttons redirecting to unfamiliar or suspicious URLs.
- Attachments or links that request personal information, particularly login credentials.
Even when emails appear polished, skepticism is warranted. Scammers frequently exploit well-known brands to create a sense of trust.
Mitigating the Risk: How to Protect Yourself
Taking preventive measures is the best defense against phishing scams like the 'Full Storage Notification':
- Verify Before Acting: Always double-check the sender's email address and inspect URLs before clicking. Genuine service providers typically use official domains.
- Avoid Clicking Links in Unsolicited Emails: Instead, visit the service provider's website directly to verify account details.
- Enable Two-Factor Authentication (2FA): Adding an extra layer of security helps protect accounts even if credentials are compromised.
- Educate Yourself: Familiarize yourself with common phishing tactics to stay one step ahead of scammers.
- Routinely Update Passwords: Use strong, unique passwords for each account, and avoid reusing them across platforms.
Act Swiftly If Compromised
If you suspect that your credentials have been harvested, take immediate action:
- Change the passwords for the affected account and any other accounts using the same credentials.
- Enable 2FA for added security.
- Monitor linked accounts for unusual activity.
- Contact the service provider's official support team to report the incident and seek assistance.
A Broader Cyber Threat: Beyond Email Tactics
The 'Full Storage Notification' scam is just one example of how spam emails are used to deceive users. Phishing emails are often a gateway to more significant cyber threats, including identity theft, financial fraud, and the spread of harmful software.
As phishing schemes become increasingly sophisticated, users must stay informed and cautious. Adopting a proactive approach to cybersecurity ensures a safer online experience and protects not only individual users but the broader digital community as well. Remember, a moment of vigilance can prevent significant harm.