Foxy Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 3 |
| First Seen: | January 25, 2019 |
| Last Seen: | December 3, 2022 |
| OS(es) Affected: | Windows |
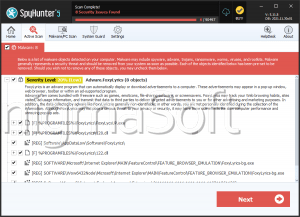
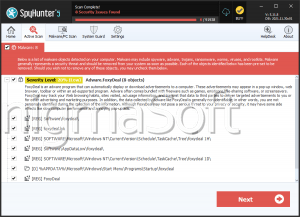
The Foxy Ransomware is an encryption ransomware Trojan that was first observed on November 8, 2017. The Foxy Ransomware, like most other encryption ransomware Trojans, is designed to take the victims' files hostage by enciphering them with a strong encryption algorithm and then demanding the payment of a ransom in exchange for the decryption key. The Foxy Ransomware and similar threats may be delivered using corrupted email attachments. These email attachments may take the form of Microsoft Word documents with bad macro scripts that download and install the Foxy Ransomware onto the victim's computer. The Foxy Ransomware seems to be based on HiddenTear, an open source ransomware family that has been responsible for countless infections since its initial release in August 2015. The Foxy Ransomware is nearly identical to a variety of ransomware Trojans released within a short time between each other, which may mean that the Foxy Ransomware is part of a new RaaS (Ransomware as a Service) or a wave of ransomware attacks.
Table of Contents
How the Foxy Ransomware’s Infection Works
The Foxy Ransomware uses the AES 256 encryption to make the victim's files unusable, targeting the user-generated files such as media files and files associated with commonly used software. The Foxy Ransomware will often run as 'WindowsSoundDriver.exe' or 'Foxy - Rnsmwre.exe' on the infected computer's Task Manager. The Foxy Ransomware scans the victim's computer for eligible files for the attack, avoiding the Windows system files (so that the victim's computer is still functional enough to deliver a ransom note and enable payment). The Foxy Ransomware marks the encrypted files by adding the file extension '.nightmare' to the end of each file's name. The following are some of the file types that may be encrypted during a Foxy Ransomware infection:
.3dm, .3g2, .3gp, .7zip, .aaf, .accdb, .aep, .aepx, .aet, .ai, .aif, .as, .as3, .asf, .asp, .asx, .avi, .bmp, .c, .class, .cpp, .cs, .csv, .dat, .db, .dbf, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .dxf, .efx, .eps, .fla, .flv, .gif, .h, .idml, .iff, .indb, .indd, .indl, .indt, .inx, .jar, .java, .jpeg, .jpg, .js, .m3u, .m3u8, .m4u, .max, .mdb, .mid, .mkv, .mov, .mp3, .mp4, .mpa, .mpeg, .mpg, .msg, .pdb, .pdf, .php, .plb, .pmd, .png, .pot, .potm, .potx, .ppam, .ppj, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prel, .prproj, .ps, .psd, .py, .ra, .rar, .raw, .rb, .rtf, .sdf, .sdf, .ses, .sldm, .sldx, .sql, .svg, .swf, .tif, .txt, .vcf, .vob, .wav, .wma, .wmv, .wpd, .wps, .xla, .xlam, .xll, .xlm, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .xml, .xqx, .xqx, .zip.
How the Cybercrooks can Profit from the Foxy Ransomware and Similar Threats
Threats like the Foxy Ransomware function by delivering a ransom note to the victim demanding payment of a ransom. In the case of the Foxy Ransomware, this threat delivers a program window named 'Foxy – Ransomware' on the victim's computer. The Foxy Ransomware's ransom note has the following text:
'1.) What happened to my PC/Files?
- Your files has been encrypted, that means, they are useless to you.
2.) Can I recover my Files?
- Of course. Just pay the price shown below, to the also shown below, Bitcoin Address and after we received the Payment you get the decryption key.
[48 HOURS COUNDOWN TIMER]
If the Countdown is finished, all your files get deleted
Pay Fast, get safe!
[Do Payment|BUTTON]
[Decrypt Files|BUTTON]'
Unfortunately, the files that have been encrypted by the Foxy Ransomware cannot be decrypted without the decryption key that its perpetrators hold in their possession. However, computer users must refrain from paying the Foxy Ransomware ransom or contacting these people. It is very unlikely that they will help computer users restore their files, and paying the Foxy Ransomware ransom allows them to continue financing their activities and creating new threats like the Foxy Ransomware. Instead of paying the ransom, computer users should take preventive measures, mainly having file backups on a portable memory device or the cloud. File backups enable computer users to restore their files after removing the Foxy Ransomware with the help of an effective security program.
URLs
Foxy Ransomware may call the following URLs:
| news-cezimu.cc |