Flashback
MAC.OSX.Flashback, also known as MACOS/Flashback.A, Fakeflash, or Flashback, is a Trojan horse that has plagued MacOS-based machines since 2011. As such, MAC.OSX.Flashback plants malware on your Mac when, and if, anything urges you to execute it. Usually, Flashback may land on your machine under the guise of a Flash Player update, a Java vulnerability, or any other seemingly innocuous piece of software. That is why you may never notice the infection until its payload comes into action. However, to do so, Flashback will need to have found its way into your MacOS X system first.
Table of Contents
Flashback Infection Vectors
Although Mac-tailored malware attacks bear no comparison with Windows-based threats, that trend hardly applies to Trojans in particular. No one is immune to malicious email attachments and suspicious web downloads. Whether an email will invite you to open a seemingly important document – an invoice, a transportation bill, or any other similar file – or a particular site will entice you to get a fake Flash Player or Java update, the risk is always there. These are the primary channels cybercriminals use to smuggle Trojans into your system—the MACOS/Flashback.A Trojan makes no exception. The image below is indicative of a Flashback Trojan infection disguised as a fake Adobe Flash Player update. That is the same dialogue box you would see when you update it for real, which makes Trojans so dangerous to tackle.
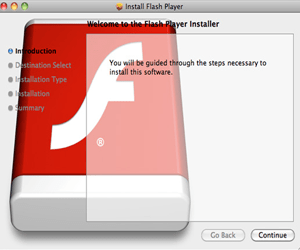
Fake Flash Player dialog alert message from Flashback threat.
Flashback Potential Damage
Like other Trojans out there, Flashback is notorious for its multifaceted nature when it comes to the damage it inflicts. Some victims have complained bitterly about stolen financial credentials. Others have suffered a significant slowdown in their machines' processing power. Still others have found themselves embroiled in a botnet designed to carry out DDoS attacks, and so forth. Some researchers have even observed keyboard capturing activities, as well as backdoor-like behavior. All in all, the crooks behind the Flashback Trojan appear to utilize the entire spectrum of possibilities for the malware damage inflicted upon unsuspecting MacOS users.
Flashback Avoidance, Mitigation, and Removal
To avoid getting a Flashback Trojan infection, always update your software from the official website of the corresponding vendor. A malicious email attachment, on the other hand, can be a tougher nut to crack. Sometimes, you may receive a malware-laden email on behalf of one of your trusted contacts, even if the latter may be blissfully unaware of such an act. To eliminate Java-related vulnerabilities, you will either need to rely on timely patches or disable Java altogether.
Once Flashback/Fakeflash has struck your machine, there’s little room to mitigate the extent of the damage unless you deploy a reputable anti-malware solution at the earliest opportunity. For it’s always better to act in the nick of time than not act at all.
