FileCoder Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 6,542 |
| Threat Level: | 100 % (High) |
| Infected Computers: | 1,963 |
| First Seen: | July 15, 2015 |
| Last Seen: | March 16, 2026 |
| OS(es) Affected: | Windows |
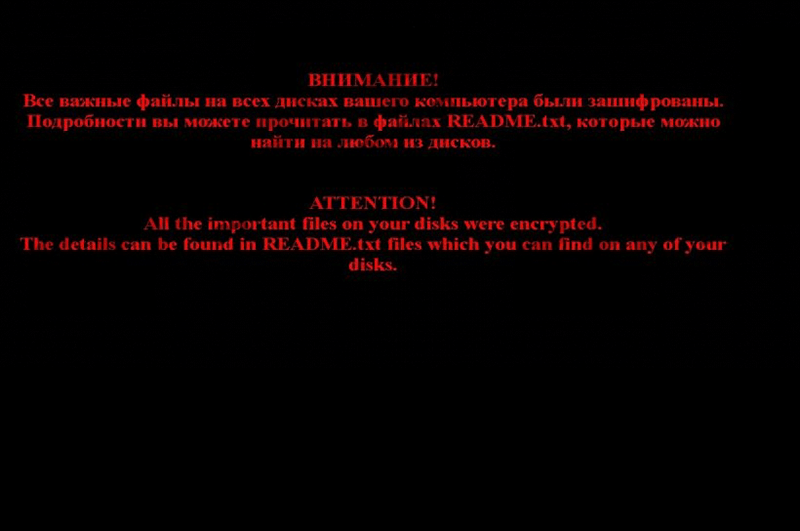
FileCoder Ransomware Image
FileCoder Trojans are Trojan infections that encrypt content on the victim's computer. FileCoder infections are a form of ransomware. Essentially, they take the victim's computer hostage, encrypting the victim's files and then demanding payment of a ransom in exchange for decrypting software. There has been an unusual increase in Filecoder infections lately. FileCoder Ransomware infections are often accompanied by a social engineering component that may try to convince computer users that the files were infected by the law enforcement of by Microsoft. However, regardless of the specific variant of FileCoder Ransomware infecting the victim's computer, the basic scam is essentially the same.
Table of Contents
FileCoder Ransomware Attacks Have Spiked in Recent Months
According to malware researchers, weekly attacks involving Filecoder attacks have tripled during the Summer of 2013 when compared to the average number of attacks in the period between January and June of 2013. The majority of FileCoder Ransomware attacks take place in the Russian Federation, with about 44 percent of attacks located in this part of the world. However, a large number of Filecoder attacks have also occurred in the rest of Europe and the United States.
To Avoid FileCoder Ransomware Attacks You Should Be Careful When Browsing the Internet
Filecoder Trojans can infect computers in a variety of ways. The following are the most common ways in which criminals can infect your computer with a FileCoder Ransomware infection:
- Most Filecoder attacks come from drive-by downloads on attack websites. These are Web pages that are set up specifically to deliver threats to victims PCs. Computer users are directed to these types of attack websites using risky scripts and redirect Trojans that may be inserted into poorly protected legitimate websites.
- The Filecoder Trojan may also be distributed through spam email attachments. Spam email attachments containing threats have become harder to detect due to phishing techniques that have risen in recent years. Criminals have become adept at disguising their email messages so they appear to come from a legitimate source convincing computer users that they should open an attached file. For example, a fake message from FedEx may arrive into the victim's inbox claiming that an attached PDF file contains information about a package. However, the file is specially engineered to install a Filecoder variant on the victim's computer.
- Filecoder variants may also be installed directly by criminals on computers that have already become compromised.
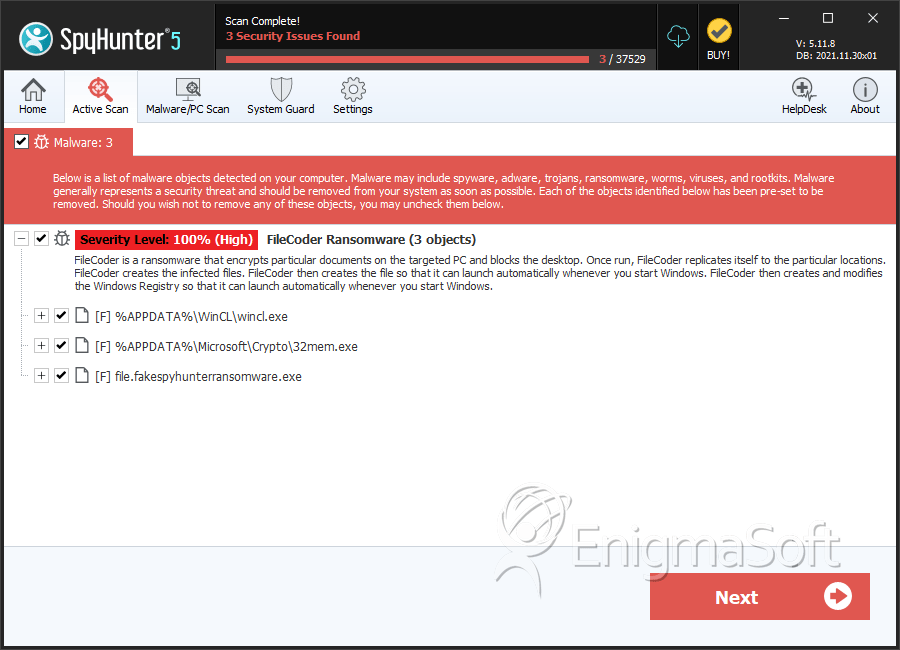
SpyHunter Detects & Remove FileCoder Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | wincl.exe | d5e9cc571996cd3fafe496ce4834001f | 225 |
| 2. | file.fakespyhunterransomware.exe | f8c589dec8eb0e8fa5e36b0b49372cfc | 2 |
| 3. | 32mem.exe | f308e97e0674acd978d9df9b66880b10 | 1 |
Registry Details
Analysis Report
General information
| Family Name: | FileCoder Ransomware |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
6ac1a8abe9f47761e1668c8cb90174b0
SHA1:
44e5d1a82f8047753188bf9c386c5d55ac76c759
SHA256:
57566FF4060944D7E6D3416B7CB6646C8607139496998B76FC8D18AAA5F6D799
File Size:
1.19 MB, 1188231 bytes
|
|
MD5:
92fa3a24687cf7c65ce60c122485cb4d
SHA1:
9a8d1c2cf3ab6a1dd065816dcbcbe96d40f1b1c7
SHA256:
6C6FAAFC283CFA051E1D6BC5F283FF1A400007A1171FD993070247A8CC06CA89
File Size:
1.19 MB, 1188236 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| File Version | 1.00 |
| Internal Name | TJprojMain |
| Original Filename | TJprojMain.exe |
| Product Name | Project1 |
| Product Version | 1.00 |
File Traits
- .NET
- x86
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|
