Farattack Ransomware
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 100 % (High) |
| Infected Computers: | 2 |
| First Seen: | February 8, 2022 |
| Last Seen: | February 8, 2022 |
| OS(es) Affected: | Windows |
The Farattack Ransomware is a vicious malware threat that can prevent its victims from accessing their own data. The threat is delivered to the targeted computer stealthily after which it will engage a powerful encryption routine. By using an uncrackable cryptographic algorithm, Farattack will lock nearly all of the files stored on the breached device, rendering them unusable. Users who wish to restore their data will find that doing so without paying the hackers for their decryption key is nearly impossible.
Victims also will notice that all affected files now have '.farattack' appended to their original names as a new file extension. Furthermore, the threat will create a new text file containing its ransom note. The name of the text file is 'How_to_recovery.txt.'
Table of Contents
Ransom Note’s Overview
The message found inside the text file contains little useful information by itself. In fact, nearly the entire note is dedicated to explaining how the victims of the threat can contact the cybercriminals to receive additional instructions. The main communication channel appears to be via a dedicated website hosted on the TOR network.
However, if victims find accessing the site far too difficult, two email addresses - 'ithelp02@decorous.cyou' and 'ithelp02@wholeness.business,' are left as ways to contact the hackers. The Farattack Ransomware warns its victims that if they do not send a message within the first 72 hours, the price of the demanded ransom will be increased.
The full text of the note is:
'Contact us for price and get decryption software.
Note that this server is available via Tor browser only Follow the instructions to open the link:
qd7pcafncosqfqu3ha6fcx4h6sr7tzwagzpcdcnytiw3b6varaeqv5yd.onionType the addres "hxxps://www.torproject.org" in your Internet browser. It opens the Tor site.
Press "Download Tor", then press "Download Tor Browser Bundle", install and run it.
Now you have Tor browser. In the Tor Browser open qd7pcafncosqfqu3ha6fcx4h6sr7tzwagzpcdcnytiw3b6varaeqv5yd.onion
Start a chat and follow the further instructions.
If you can not use the above link, use the email:
ithelp02@decorous.cyou
ithelp02@wholeness.business- To contact us, create a new free email account on the site: protonmail.com
IF YOU DON'T CONTACT US WITHIN 72 HOURS, PRICE WILL BE HIGHER.'
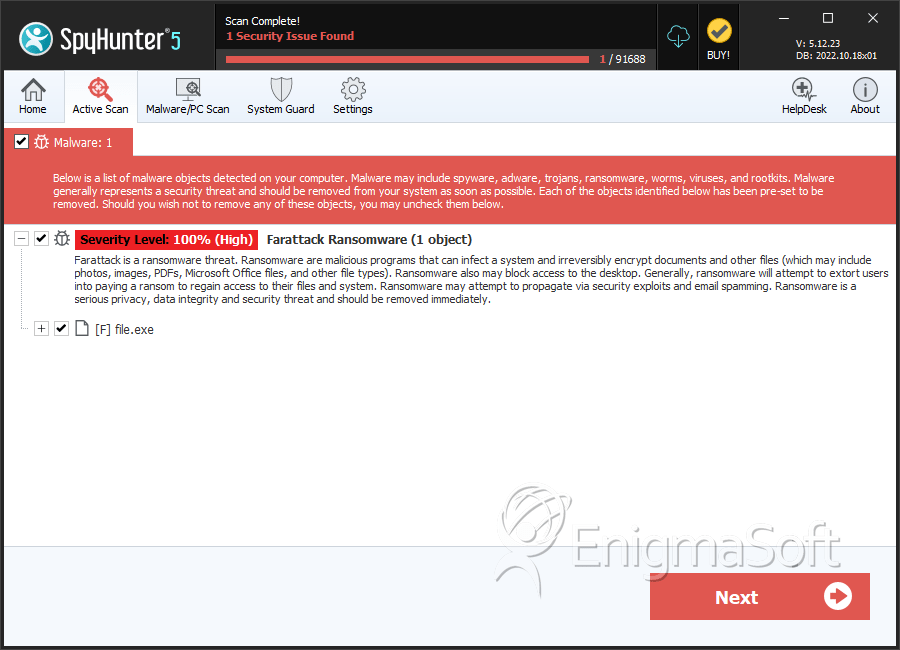
SpyHunter Detects & Remove Farattack Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 1c021f42e3a138060e1d298726d1579f | 1 |

