End Ransomware
Protecting devices from malware is a critical responsibility for individuals and organizations alike. Modern ransomware operations are highly organized, technically advanced, and financially motivated. A single successful infection can result in severe data loss, operational disruption, reputational damage, and financial strain. One such sophisticated threat is End Ransomware, a strain that demonstrates the evolving tactics and psychological pressure mechanisms common in today's cybercrime landscape.
Table of Contents
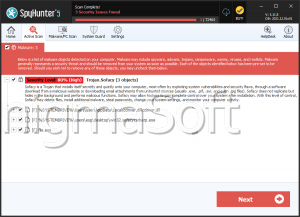
End Ransomware: A MedusaLocker Variant with Aggressive Tactics
In-depth analysis has identified End Ransomware as a variant belonging to the MedusaLocker family. Security researchers discovered this threat during investigations into active malware campaigns targeting both individual users and corporate environments.
Once executed on a compromised system, End Ransomware initiates a multi-stage attack routine. It encrypts files using a combination of RSA and AES cryptographic algorithms, ensuring that data becomes inaccessible without the attackers' decryption key. Encrypted files are appended with the '.end11' extension. For example, '1.png' is renamed to '1.png.end11,' and '2.pdf' becomes '2.pdf.end11.' This modification clearly signals successful encryption and prevents normal file access.
In addition to file encryption, the ransomware changes the victim's desktop wallpaper and drops a ransom note titled 'HOW_TO_RECOVER_DATA.html.' These actions are designed to maximize visibility and pressure, ensuring that the victim immediately understands the severity of the incident.
Ransom Note and Double Extortion Strategy
The ransom note claims that files have been encrypted but not permanently damaged, asserting that recovery is possible only with the attackers' assistance. Victims are warned not to use third-party recovery tools or attempt to rename or modify encrypted files, as doing so could allegedly cause irreversible damage.
A particularly concerning aspect of End Ransomware is its use of double extortion tactics. The note claims that confidential and personal data have been exfiltrated and stored on a private server controlled by the attackers. According to the message, stolen data will be destroyed after payment. However, refusal to comply allegedly results in public release or sale of the information.
Victims are instructed to contact the attackers via email at 'doctorhelperss@gmail.com' or 'korona@bestkoronavirus.com' for payment instructions. A strict 72-hour deadline is imposed, after which the ransom amount is said to increase. This artificial urgency is a common psychological tactic intended to reduce rational decision-making and accelerate payment.
It is important to emphasize that paying a ransom does not guarantee data recovery. Attackers may fail to provide a working decryption tool, demand additional payments, or disappear entirely after receiving funds.
Persistence and Lateral Risk
Leaving ransomware active on an infected system significantly increases risk. If not properly removed, the malware may continue encrypting newly created or previously untouched files. In networked environments, it may also attempt lateral movement, spreading to connected systems and shared storage resources.
Therefore, containment and eradication are essential steps following detection. Simply decrypting files, if even possible, without removing the malicious payload, can result in reinfection and additional damage.
Common Infection Vectors
End Ransomware, like many modern ransomware families, relies on multiple distribution techniques to maximize reach. These commonly include:
- Fraudulent emails containing malicious attachments or links
- Exploitation of unpatched software vulnerabilities
- Fake technical support scams
- Pirated software, cracking tools, and key generators
- Peer-to-peer networks and unofficial download platforms
- Malicious advertisements and compromised websites
The malicious payload is often concealed within executable files, scripts, compressed archives, or document formats such as Word, Excel, or PDF files. Once opened, or after additional user interaction such as enabling macros, the ransomware executes and begins encrypting data.
Strengthening Defenses: Essential Security Best Practices
Effective defense against ransomware, such as End, requires a layered and proactive security strategy. The following practices significantly reduce the likelihood and impact of infection:
- Maintain regular, offline, and immutable backups of critical data. Backups should be stored separately from the primary network to prevent ransomware from encrypting them as well.
- Apply security patches and software updates promptly to operating systems, applications, and firmware to eliminate exploitable vulnerabilities.
- Deploy reputable, up-to-date endpoint protection solutions capable of detecting ransomware behavior and blocking suspicious activity.
- Disable macros by default in office applications and restrict the execution of unauthorized scripts.
- Implement strong access controls and the principle of least privilege to limit user permissions and reduce lateral movement opportunities.
- Use multi-factor authentication for remote access services and administrative accounts.
- Conduct regular cybersecurity awareness training to help users identify phishing emails, malicious attachments, and social engineering attempts.
- Monitor network activity for anomalies, including unusual file modifications or outbound data transfers.
A comprehensive security posture combines technical controls with user education and consistent policy enforcement. Prevention is always more cost-effective and reliable than post-incident recovery.
Final Assessment
End Ransomware represents a sophisticated and dangerous threat within the MedusaLocker family. By combining strong encryption, data exfiltration, and time-based pressure tactics, it exemplifies the modern ransomware model built around financial extortion.
Organizations and individuals must recognize that ransomware defense is not a single tool or action but a continuous process. Proactive protection, rapid detection, and disciplined incident response remain the most effective strategies for minimizing damage and ensuring operational resilience in the face of evolving cyber threats.