Ekans Ransomware
 The EKANS Ransomware is a threat that first appeared in December 2019. Most ransomware threats are built in a rather simple manner as the majority of cybercriminals borrow the code of already existing threats and only tweak it slightly to fit their preferences. However, this is not what happens with the EKANS Ransomware. This is a very high-end Trojan that does not target everyday users. Instead, the EKANS Ransomware goes after industrial facilities like large factories or powerplants. The EKANS Ransomware targets ICS (Industrial Control Systems) in particular.
The EKANS Ransomware is a threat that first appeared in December 2019. Most ransomware threats are built in a rather simple manner as the majority of cybercriminals borrow the code of already existing threats and only tweak it slightly to fit their preferences. However, this is not what happens with the EKANS Ransomware. This is a very high-end Trojan that does not target everyday users. Instead, the EKANS Ransomware goes after industrial facilities like large factories or powerplants. The EKANS Ransomware targets ICS (Industrial Control Systems) in particular.
Note: Snake Ransomware also goes by the handle 'EKANS Ransomware'
Experienced and highly skilled cybercriminals can afford to go after targets that cannot stay offline for long – medical institutions, banks, factories, etc. However, most cyber crooks do not target ICS, as it is not easy to generate revenue from such attacks. Furthermore, ICS’ inner workings are not easy to discover and study. However, the authors of the EKANS Ransomware, in addition to the hackers behind Snake ransomware, have managed to create a very potent threat that is capable of targeting 64 software processes. The processes in question are either unique to ICS or are commonly utilized in ICS. This is a far more complex campaign compared to previous ransomware attacks launched against ICS. Previous campaigns would normally go after regular PCs that are connected to the facility’s system. In contrast, the EKANS Ransomware is capable of shutting down crucial processes of ICS.
EKANS Ransomware Uses Aggressive Execution and Encryption Actions to Attack Vulnerable Computers
The EKANS ransomware is written in the Go programming language. Analysts from Dragos found that it uses custom Go libraries to construct and ensure the execution of the ransomware.
Once the EKANS ransomware infiltrates a system, it searches for an "EKANS" Mutex value. If the value is found, the ransomware execution will be stopped, and an "already encrypted!" message will be displayed. If the value is not found, the ransomware will proceed with encryption via Windows Management Interface (WMI) calls. The victim's Volume Shadow Copy backups will also be removed.
Before encrypting the victim's files, the EKANS ransomware will force stop a number of processes whose names are contained in a hard-coded list. While some of these processes are, expectedly, related to security and management software like Microsoft System Center and Qihoo 360 Safeguard, the majority of "killed" processes are related to data backup solutions, databases, or ICS-related processes. The malware can't inject commands or manipulate ICS-related processes. It just shuts them down. However, shutting down a data historian process would cause a loss of view condition within the targeted network.
During encryption, the EKANS ransomware will append files with five random characters (upper-case and lower-case) connected to the original file extension. Below is a list of examples.
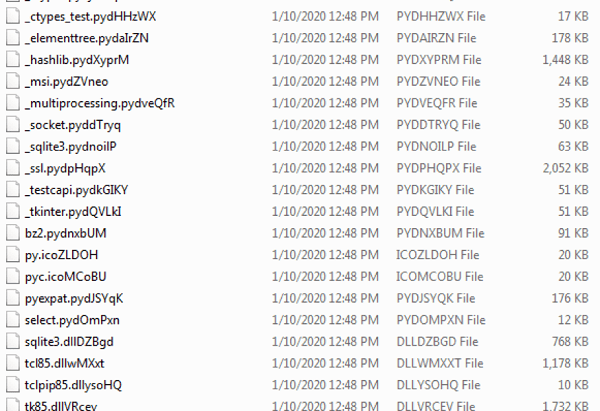
EKANS ransomware encrypted files list. Source: Dragos
Once the encryption process is over, the EKANS ransomware will drop a ransom note in the system drive (usually C:\) as well as the active user's desktop. The ransom note reads:
---------------------------------------------
| What happened to your files?
---------------------------------------------
We breached your corporate network and encrypted the data on your computers. The encrypted data includes documents, databases, photos, and more - all were encrypted using military grade encryption algorithms (AES-256 and RSA-2048). You cannot access those files right now. But dont worry!
You can still get those files back and be up and running again in no time.
----------------------------------------------
| How to contact us to get your files back?
----------------------------------------------
The only way to restore your files is by purchasing a decryption tool loaded with a private key we created specifically for your network.
Once run on an affected computer, the tool will decrypt all encrypted files - and you can resume day-to-day operations, preferably with better cyber security in mind. If you are interested in purchasing the decryption tool contact us at bapcocrypt@ctemplar.com
----------------------------------------------
| How can you be certain we have the decryption tool?
----------------------------------------------
In your mail to us attach up to 3 files (up to 3MB, no databases or spreadsheets).
We will send them back to you decrypted
After studying the EKANS Ransomware, cybersecurity experts have found that this Trojan is rather similar to a ransomware threat deployed in 2019 dubbed Megacortex. The Megacortex threat is believed to originate from the United Kingdom as its creators had referenced various stores located in the city of Sunderland. Going even further into the rabbit hole, the Megacortex malware is likely linked to another threat called Reitspoof that was being propagated via spam messages on Skype in 2019. However, some malware researchers suspect that this may be a complex operation carried out by a state-sponsored hacking group, and the links to the previously mentioned threats might have been placed on purpose to mislead analysts.
According to researchers, it is very likely that Bapco, the national oil company of Bahrain, has fallen victim to the EKANS Ransomware. The BBC recently reported that Honda was hit by a cyberattack, which the company confirmed in a tweet. Another attack that was disclosed via Twitter hit Edesur S.A., a company belonging to Enel Argentina, an energy distribution company that operates in the City of Buenos Aires. Both the attacks against Honda and Enel appear to be related, and the evidence points to the EKANS ransomware. The complex and well-built EKANS Ransomware may set a new trend in the world of ransomware, and we may start seeing more threats of this type targeting ICS.

