Eeyee Ransomware
The Eeyee Ransomware is a malware designed specifically to lock the files and data of its victims. Ransomware threats achieve their nefarious goals by executing an encryption routine involving an uncrackable cryptographic algorithm. While the affected files will still be present on the system, they will be rendered inaccessible and unusable.
The attackers will then extort the victim for money in exchange for providing the required decryption keys. Most ransomware operations also employ other extortion avenues, such as collecting private data and then threatening to release it to the public.
As part of its programming, the Eeyee Ransomware will generate a random ID key for the specific victim, consisting of a lengthy string of characters. This key alongside '.eeyee' will be appended to the original names of all encrypted files. Finally, the threat will deliver a ransom note to the compromised system. The ransom-demanding message will be placed inside a text file named '6pZZ_HOW_TO_DECRYPT.txt.'
Table of Contents
Ransom Note Details
The hacker's message states that information, such as personal data, financial reports, or other essential documents has been obtained from the compromised devices. Victims who do not wish to pay the demanded ransom will have their information published on a dedicated leak site hosted on the TOR network. Communication with the attackers can be carried out through a separate site hosted on the same network. To access it, users will need to enter the login and password credentials found inside the ransom note.
The full text of the note is:
'Your network has been breached and all data were encrypted.
Personal data, financial reports and important documents are ready to disclose.To decrypt all the data and to prevent exfiltrated files to be disclosed at
hxxp://hiveleakdbtnp76ulyhi52eag6c6tyc3xw7ez7iqy6wc34gd2nekazyd.onion/
you will need to purchase our decryption software.Please contact our sales department at:
hxxp://hivecust6vhekztbqgdnkks64ucehqacge3dij3gyrrpdp57zoq3ooqd.onion/Login:
Password:
To get an access to .onion websites download and install Tor Browser at:
hxxps://www.torproject.org/ (Tor Browser is not related to us)Follow the guidelines below to avoid losing your data:Do not modify, rename or delete *.key.eeyee files. Your data will be
undecryptable.Do not modify or rename encrypted files. You will lose them.
Do not report to the Police, FBI, etc. They don't care about your business.
They simply won't allow you to pay. As a result you will lose everything.Do not hire a recovery company.
They can't decrypt without the key.
They also don't care about your business.They believe that they are good negotiators, but it is not.
They usually fail. So speak for yourself.
Do not reject to purchase.
Exfiltrated files will be publicly disclosed.'
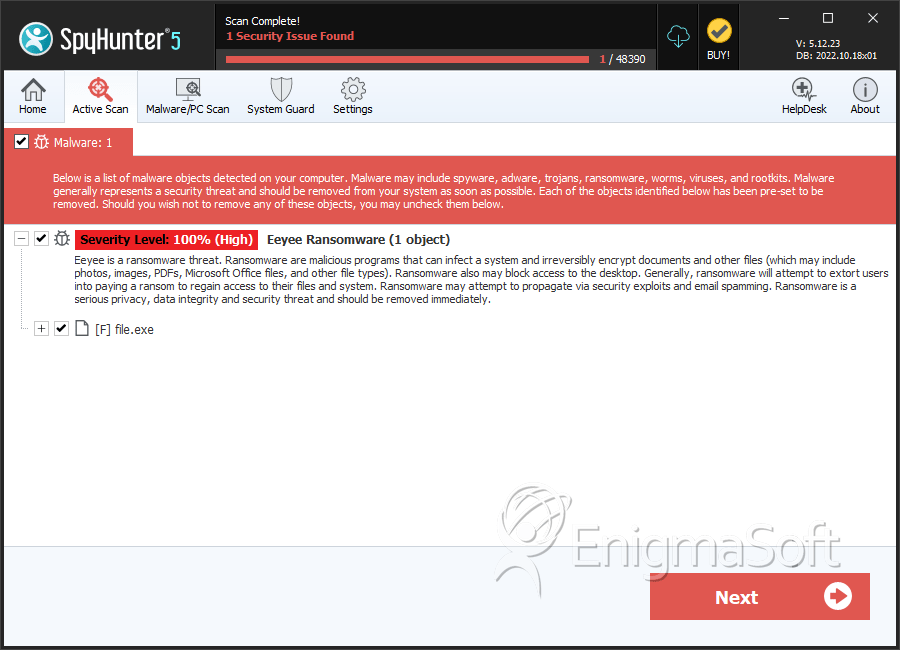
SpyHunter Detects & Remove Eeyee Ransomware
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 9be36e26502078b2ce42beb735e96673 | 0 |

