DynoWiper Malware
In the final week of December 2025, the Russian nation-state hacking group widely known as Sandworm was attributed to what has been described as the largest cyber attack attempt ever recorded against Poland's power system. The incident unfolded during the last days of the year and was publicly acknowledged by national authorities as the most intense assault on the country's energy infrastructure in years.
Despite the scale and sophistication of the operation, the attack was unsuccessful. Poland's energy minister, Milosz Motyka, confirmed that no disruption to electricity supply was observed.
Table of Contents
Critical Infrastructure Under Direct Digital Fire
The attacks, detected on December 29 and 30, 2025, were directed at two combined heat and power (CHP) plants and at a system responsible for managing electricity generated from renewable sources, including wind turbines and photovoltaic farms. Military cyberspace forces characterized the activity as the strongest hostile cyber campaign against Polish energy infrastructure in recent memory.
Researchers analyzing the incident reported no evidence that the attempted sabotage achieved any operational impact.
DynoWiper Emerges as a New Destructive Tool
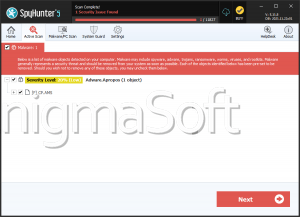
According to a newly released report by information security specialists, the operation involved a previously undocumented wiper malware named DynoWiper, also tracked as Win32/KillFiles.NMO. The attribution to Sandworm is based on technical and behavioral overlaps with earlier destructive campaigns linked to the same adversary, particularly those conducted after Russia's full-scale invasion of Ukraine in February 2022.
The wiper was deployed as part of a coordinated attempt to disrupt Poland's energy sector, signaling continued investment by the threat actor in purpose-built tools designed for infrastructure sabotage.
Government Response and Regulatory Countermeasures
Polish authorities stated that all indicators point to groups directly connected to Russian services. In response, the government is preparing additional safeguards, including the advancement of key cybersecurity legislation. The planned measures are expected to impose stricter requirements for risk management, protection of both information technology (IT) and operational technology (OT) systems, and the handling of cyber incidents affecting critical services.
A Symbolic Date with Historical Resonance
The timing of the activity carried particular significance. The attempted Polish grid intrusion coincided with the tenth anniversary of Sandworm's landmark attack on Ukraine's power grid in December 2015. That earlier campaign leveraged the BlackEnergy malware to deploy a destructive component known as KillDisk, triggering power outages lasting four to six hours and leaving roughly 230,000 residents in the Ivano-Frankivsk region without electricity.
A Decade of Persistent Disruption
Sandworm has built a long record of targeting critical infrastructure, most notably in Ukraine. Ten years after the 2015 blackout, the group continues to pursue disruptive objectives across multiple sectors.
In June 2025, researchers disclosed that a Ukrainian critical infrastructure organization had been struck by a previously unseen data-wiping malware dubbed PathWiper, which showed functional similarities to HermeticWiper, another Sandworm-associated tool. During the same year, the group was also observed deploying additional destructive malware families, including ZEROLOT and Sting, within a Ukrainian university network, followed by a broader wave of data-wiping attacks against Ukrainian government, energy, logistics, and grain sector entities between June and September 2025.
Strategic Implications for Energy Sector Defense
The attempted intrusion into Poland's power ecosystem reinforces the assessment that Sandworm remains focused on cyber operations capable of producing physical-world consequences. The emergence of DynoWiper, alongside a growing catalog of wipers, highlights the continued evolution of destructive malware and underscores the urgency for energy providers to strengthen resilience, monitoring, and coordinated response mechanisms across both IT and OT environments.