Dexter Ransomware
Protecting digital environments from malware has become a critical responsibility for individuals and organizations alike. Modern ransomware operations are increasingly refined, capable of causing severe data loss and operational disruption within minutes of execution. One such emerging threat identified by security researchers is known as Dexter Ransomware, a malicious program engineered to encrypt valuable data and extort victims for financial gain.
Table of Contents
Dexter Ransomware at a Glance
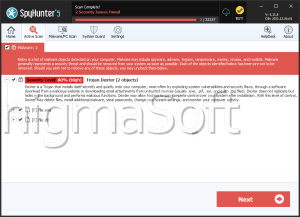
Dexter ransomware surfaced during in-depth investigations into newly circulating malware strains. Its primary objective is data encryption followed by coercion, a model consistent with contemporary ransomware campaigns. Once active on a compromised system, the malware scans for targeted files and encrypts them using cryptographic routines that render the data inaccessible to the victim.
Encrypted files are renamed with an added 'dexter' extension, making the impact immediately visible. For example, a file previously named '1.png' is transformed into '1.pngdexter,' clearly signaling successful compromise. After completing the encryption routine, Dexter presents a ransom note through a pop-up window to ensure the victim is aware of the attack.
Ransom Demands and Attacker Tactics
The ransom note claims that all affected files have been encrypted and states that decryption is only possible through cooperation with the attackers. Victims are instructed to pay a ransom in Bitcoin cryptocurrency. Notably, inconsistencies appear in the demanded amounts: the note references both a fiat value of 1500 USD and a Bitcoin amount of 0.0030 BTC, figures that do not align with real-time exchange rates and suggest either carelessness or deliberate obfuscation by the attackers.
Such discrepancies highlight an important reality of ransomware incidents: attackers provide no consumer guarantees. Even when payment is made, victims frequently receive no decryption keys or tools. As a result, cybersecurity professionals strongly discourage ransom payments, as they neither ensure data recovery nor reduce future risk, while directly funding further criminal operations.
Data Recovery and Damage Control
Once files are encrypted by Dexter ransomware, decryption without attacker involvement is generally infeasible. Removing the malware from the operating system is essential to prevent further encryption or lateral spread, but this action alone does not restore already locked files.
Reliable data recovery depends on the availability of clean backups created prior to infection. Effective backup strategies rely on redundancy and isolation, ensuring copies are stored in multiple locations such as offline storage devices and secure remote servers. Without such backups, victims often face permanent data loss.
Infection Vectors and Distribution Methods
Dexter ransomware relies heavily on user interaction and deceptive delivery mechanisms. Social engineering and phishing remain dominant infection vectors, with malicious files masquerading as legitimate content or being bundled with seemingly harmless software. These files may appear in multiple formats, including executable programs, compressed archives, office documents, scripts, and other commonly trusted file types.
The infection process is triggered when a malicious file is opened or executed. Distribution channels are broad and opportunistic, ranging from compromised download sites and peer-to-peer networks to fraudulent email attachments, malicious advertisements, online scams, illegal software activation tools, and fake software updates. In some cases, malware variants also possess self-propagation capabilities, allowing them to spread through local networks or removable storage devices.
Strengthening Defenses Against Ransomware
Effective defense against threats like Dexter ransomware depends on layered security practices and informed user behavior. Systems should be maintained with up-to-date operating systems and applications to minimize exposure to known vulnerabilities. Reputable security software with real-time protection capabilities plays a key role in detecting and blocking malicious activity before execution.
User awareness is equally critical. Caution should be exercised when handling unsolicited emails, links, or attachments, especially those that create urgency or promise unexpected rewards. Downloading software exclusively from trusted and verified sources significantly reduces exposure to trojanized installers. Regular, automated backups stored across isolated environments provide the last line of defense, ensuring that data can be restored without engaging with attackers.
Conclusion
Dexter ransomware exemplifies the ongoing evolution of ransomware threats, combining familiar extortion tactics with deceptive distribution strategies. Its ability to encrypt data swiftly and pressure victims through misleading ransom demands underscores the importance of proactive cybersecurity measures. By prioritizing prevention, maintaining resilient backups, and avoiding engagement with cybercriminals, users can significantly reduce the impact of ransomware incidents and protect the integrity of their digital assets.