Dever Ransomware
Dever Ransomware Image
Most authors of ransomware build their creations based on already existing data-encrypting Trojans. This is the case with the Dever Ransomware. This file-locking Trojan belongs to the Phobos Ransomware family. When the Dever Ransomware targets a system, it will make sure to lock all the files present on it. From images to audio files, documents, and archives – no data will be spared.
Propagation and Encryption
According to reports, the Dever Ransomware is being propagated via spam emails. The emails in question would contain a fake message riddled with social engineering tricks designed to convince users to launch the attached file. Executing the attachment would ensure that the target's system gets compromised. Often, the emails appear to be from a large and well-known company or a government body. The Dever Ransomware would use an encryption algorithm to lock all the targeted files. When the encryption is completed, you may notice that the names of the files have been altered. The Dever Ransomware applies a – '.id[
The Ransom Note
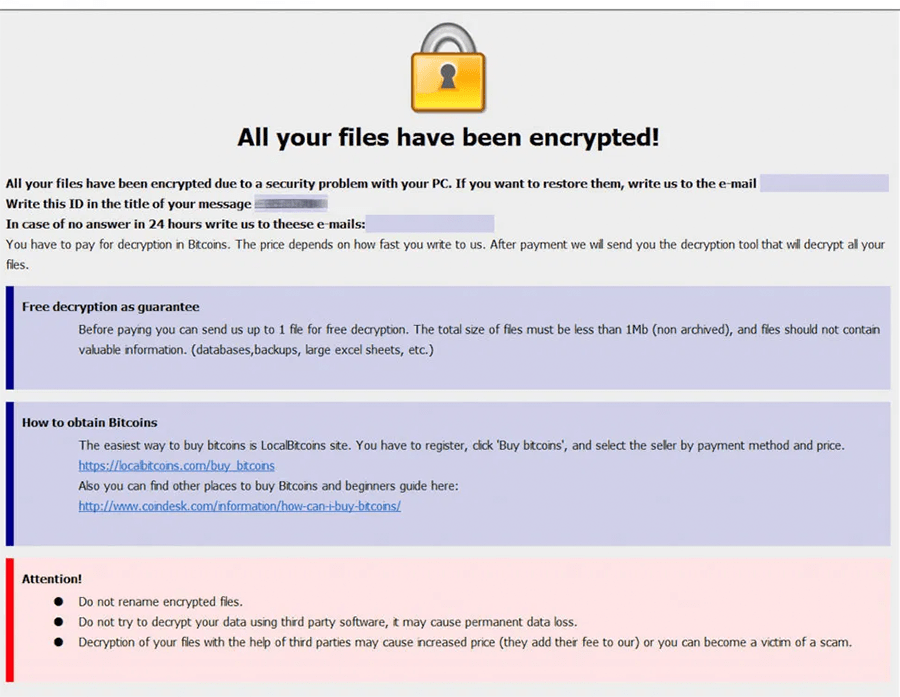
The Dever Ransomware will drop its ransom note on the desktop of the user. The ransom message will be saved in a file called 'info.txt.' In the ransom note, the authors of the Dever Ransomware do not mention how much they would like to be paid. However, they make sure to give out three email addresses where victims can get in touch with them to receive further information – ‘lizethroyal@aol.com,' ‘bexonvelia@aol.com,' and ‘maitlandtiffaney@aol.com.' It is likely that the attackers would require the payment in the shape of Bitcoin as using cryptocurrency helps them keep their anonymity and avoid repercussions. The attackers promise to provide users who pay the ransom fee with a decryption tool.
It is not a good idea to trust the words of cyber crooks. Most victims of ransomware who pay the fee required never receive the decryption tool promised to them. This is why obtaining a reputable anti-virus solution will help you remove the Dever Ransomware from your computer safely and swiftly.

